Scams
Your telephone quantity is greater than only a option to contact you – scammers can use it to focus on you with malicious messages and even exploit it to realize entry to your checking account or steal company information
13 Aug 2024
•
,
5 min. learn

Final month, we checked out how scammers can achieve entry to your telephone quantity and the way information breaches and phishing campaigns might make acquiring it straightforward. On this blogpost, we’ll focus extra on why telephone numbers are precious targets and focus on the dangers related to their compromise.
The $cam business
On-line scammers proceed to rake in staggering earnings from all kinds of fraudulent schemes. Lately, many such schemes have been orchestrated by prison syndicates that run rip-off compounds in Southeast Asia, the place trafficked people are coerced into executing elaborate ploys, equivalent to pig butchering.
Other than constructing pretend on-line relationships, the ways of many on-line fraudsters usually contain creating situations that demand pressing motion or depend on different ruses, together with purported financial institution or PayPal account takeovers, gadgets compromised with malware, failed package deal deliveries, and even kidnapped family and different schemes leveraging synthetic intelligence (AI).
On the coronary heart of many on-line fraud schemes is phishing and different social engineering assaults. Their success lies largely of their low-cost/high-reward nature, scalability, capability to exploit human weaknesses, in addition to the challenges of cross-border legislation enforcement. To prime it off, it might take one profitable “phish” to repay your complete operation.
Throw me some numbers
Let’s now have a look at how telephone numbers match into this, why they’re, along with account login credentials, so precious to scammers, and the way they are often leveraged for malicious ends.
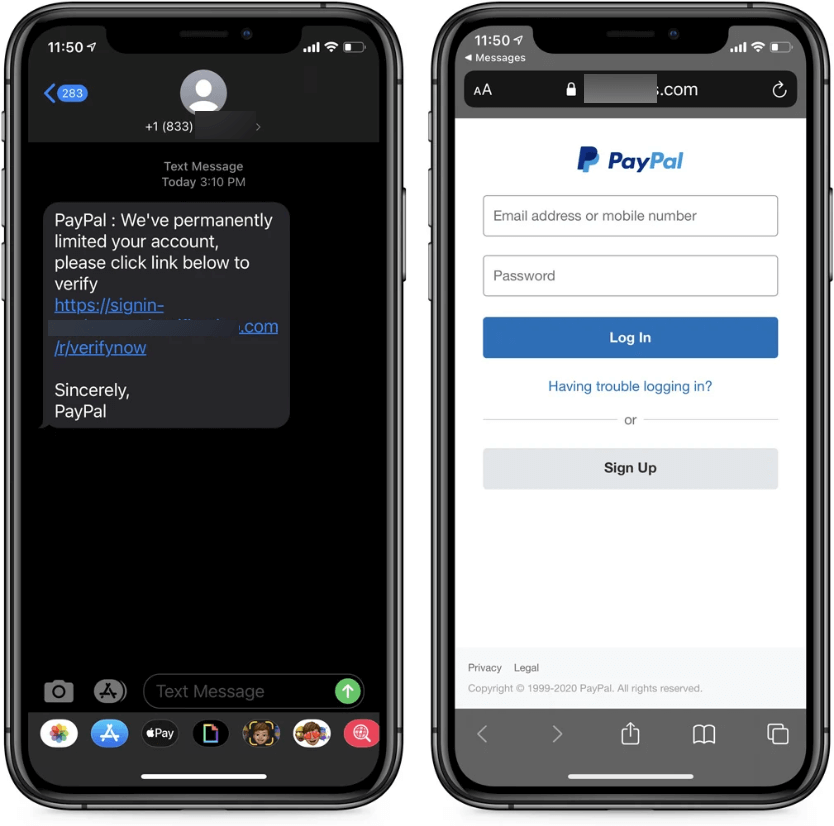
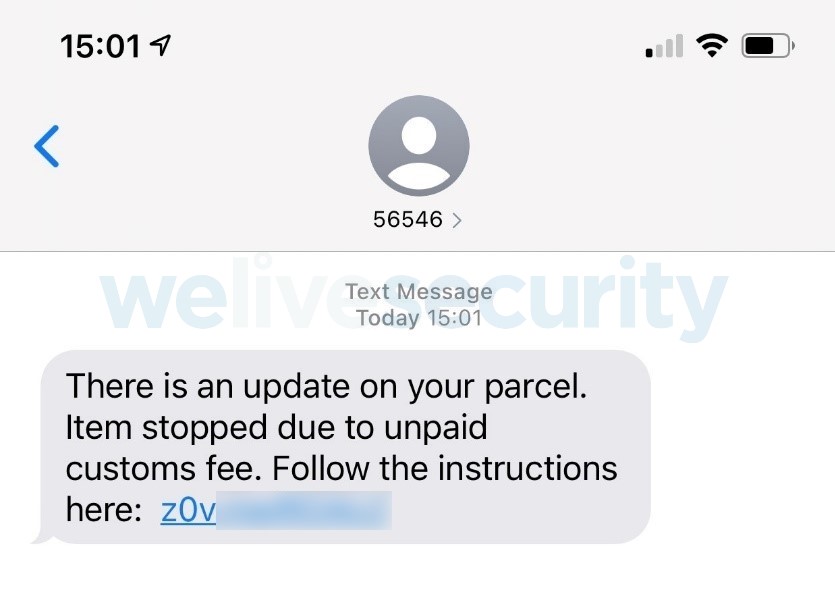
Smishing and hacking
For starters, menace actors might goal you with malware disguised as benign hyperlinks or attachments that may, nevertheless, set up spyware and adware or different malware in your gadget or exfiltrate your private information from it. Alternatively, they will ship you messages that purpose to trick you into surrendering your login credentials or different private info on phishing web sites.
For instance, ESET Risk Report H1 2024 highlighted the proliferation of GoldPickaxe malware that in its iOS iteration employs a multistage social engineering scheme that persuades victims to put in a Cellular System Administration profile, giving menace actors full management over the sufferer’s telephone.
Name forwarding, SIM swaps and Caller ID spoofing
Regardless of the rise of digital communication, telephone calls and messages stay a trusted technique for exchanging confidential info.
- In name forwarding schemes, scammers contact you or your service supplier and finally have telephone calls forwarded out of your telephone quantity to a quantity beneath their management. Whereas the supplier may ask for verification, the scammer might have already got entry to extra of your private particulars (from information leaks or public sources), making this rip-off straightforward to carry out.
- Equally, SIM swapping fraudsters can trick your cell provider into activating their SIM card beneath your title/previous quantity, successfully porting your quantity to their SIM card. This rip-off is “louder” than name forwarding mainly since you lose entry to your telephone community in consequence. Whereas additionally requiring some analysis into the sufferer’s life for the verification course of, SIM swapping has been a critical menace for years.
- Scammers can spoof their Caller ID by impersonating your quantity, utilizing Voice over Web Protocol (VoIP) or spoofing providers, and different strategies. Consequently, attackers might masks their id whereas committing monetary scams and different crimes and pretending to be you or your trusted contact.
Why are all these scams such a menace? Lately, many on-line providers depend on telephone numbers for authentication and account restoration. Compromising a telephone quantity can, subsequently, be tantamount to bypassing your safety safeguards, together with two-factor authentication (2FA). Moreover, scammers might impersonate you to defraud your contacts – or your employer.
Phishing for company information
Lately, many workers use private or firm telephones to test their company emails or messages. This creates a notable vector for assaults, as computer systems are not the only real entry factors for tried compromise. Scammers might impersonate enterprise executives or accounting departments to request cash transfers for “enterprise” functions.
Certainly, the last word objective for a lot of scammers is to realize entry to company programs and funds. The human component performs a vital position in these schemes, too. We regularly don’t confirm the legitimacy of requests earlier than complying with them, making it straightforward for phishing assaults to succeed and finally leading to substantial monetary harm to companies.
CEO fraud
For example, think about being an accountant at a big monetary firm. You’re taking part in round with Excel whenever you obtain a telephone name, seemingly out of your boss, asking you to wire over cash for a enterprise deal whose success hinges in your immediate motion. Such scams are fairly actual. For the reason that name seems to come back out of your boss’s quantity, it’s possible you’ll not query its legitimacy – and also you wouldn’t be alone.
The information runs purple with mentions of this “CEO fraud”, a subset of enterprise e-mail compromise (BEC) fraud. Right this moment, such scams are supercharged by AI, with menace actors utilizing voice cloning to higher impersonate somebody (in case caller ID spoofing wasn’t sufficient).
So, what to do in such harmful occasions?
Elevating the security internet
Fortunately, there are a number of methods folks and companies can keep freed from telephone scams:
- Validate: By no means reply or work together with unknown callers/senders, and everytime you obtain a request for private information from a “trusted” entity, name them first and ask whether or not the request you acquired was real.
- Attain out to your service supplier: To stop forwarding or SIM swaps, ask your service supplier to safe your account in opposition to undesirable adjustments with extra safety components like SIM locks to forestall swapping or extra complete verification checks.
- Thoughts what you share: To stop scams from gathering extra information on you, thoughts what you share about your self on-line. Impersonation depends on presenting oneself as somebody you recognize, so attempt to restrict your public publicity.
- Overlook SMS: To stop fraud, defend your accounts with app-based two-factor authentication as a substitute of SMS-based one. The latter will be simply intercepted and let crooks to compromise your accounts with ease.
- Use cell safety: Phishing, both by means of messages or calls, will be detected by sturdy cell safety software program. For companies, cell menace protection and safe authentication will help overcome such threats.
To conclude, since a telephone quantity generally is a doorway for menace actors and result in large-scale enterprise compromise and hundreds of thousands in harm. It ought to be stored as personal as potential – similar to another distinctive identifier, in any case.
As phishing stays a significant menace, keep vigilant and bear in mind: validation and authentication are your keys to staying safe!
Within the meantime, why not take a look at your phish-spotting prowess in our fast quiz?


