Over time the business has tied itself in knots in its makes an attempt at augmenting (or upgrading) the password, utilizing all types of complicated terminology resembling two-factor authentication (2FA), two-step authentication, multifactor authentication (MFA), and the extra fashionable confusion of common second issue (U2F), Quick IDentity On-line 2 (FIDO2), WebAuthn, and passkeys.
Up till now, most of us have been joyful sufficient to get somebody to undertake any of the above. Something greater than a password is an enchancment, however we now have now reached the purpose the place we have to elevate the minimal bar of acceptability. On this put up I’ll take a look at the present state of bypassing “stronger” authentication strategies – and, I consider, level out the perfect path ahead.
Not two good
Too lots of the easiest “2FA” choices are usually not true to what two-factor authentication is actually meant to be. Ideally the 2 components are two of the next three sorts: one thing you know (like a password or PIN), one thing you have (like a USB/Bluetooth token, SmartCard or public/personal keypair), or one thing you are (like a fingerprint or faceprint). Sadly, many of the early options boil all the way down to one thing and . . . one thing else .
Take the RSA token, SMS textual content message, or TOTP (time-based one-time passwords; e.g., Google Authenticator or Authy) types of “2FA,” the place usually you might be introduced with a 6-digit code that rotates each 30 seconds. Whereas individuals have criticized SMS implementations of this resulting from the potential of SIM swapping, the fact is they’re all weak and prone to interception.
Right here’s the issue. Think about you might be despatched a well-crafted (maybe AI-generated?) phishing e-mail. For the scammer to achieve compromising you at this stage, you need to consider the e-mail is authentic, whether or not you might be utilizing multifactor authentication or not. That is the place difficult somebody for 2 various things they know (their password and a secret code that’s dynamically generated) ends in tears: For those who actually suppose you might be logging into your financial institution, e-mail, or company account, you’ll fortunately disclose not simply your password, however the secret code as effectively. Any such authentication is barely in a single course; the scammer is verifying your id, however you haven’t verified the id of the entity asking for the proof.
There are the truth is freely accessible instruments to automate this deception. One of many extra well-liked known as evilginx2. Initially primarily based on the favored internet server nginx, it’s now a standalone Go utility that serves as an all-in-one software to phish knowledge-based multifactor authentication and steal session cookies to bypass authentication. This has lowered the barrier for malfeasance to new depths.
How did we get right here?
If we contemplate the historical past of credential compromise, all of it started with sniffing unencrypted Wi-Fi or performing different network-based assaults earlier than issues have been encrypted. Again in 2010 there was an notorious software referred to as FireSheep that was designed to permit attackers to go to a restaurant and passively steal individuals’s logins as a result of lack of encryption on the net.
In response to those assaults, and to Edward Snowden’s leaks in 2013, we moved to encrypting practically the whole lot on-line. That change secured us in opposition to what are known as machine-in-the-middle (MitM) assaults. We now have practically ubiquitous use of HTTPS throughout the online and even in our smartphone apps, which stops any random passersby from capturing the whole lot you would possibly see or do on-line.
Criminals then moved on to credential theft, and to a big diploma most of us have moved on to some variation of multifactor authentication, however once more, often merely the most affordable and best variation — one thing we all know, plus an ephemeral something-else we all know. That is an ineffective velocity bump, and we should transfer on as soon as once more.
Trade consensus has, after many a committee assembly and requirements physique creation, settled on a broadly agreed-upon commonplace often known as the Internet Authentication API, or WebAuthn. If you wish to dive deeply into the confusion over the assorted bits and items, there’s a Reddit thread for that, however I received’t go too deeply into these weeds right here.
A stroll by way of WebAuthn
WebAuthn/passkeys make multifactor authentication near phish-proof. Nothing is ideal, in fact, and current analysis has found a limited-but-interesting MitM assault vector involving specialised {hardware} units and a since-patched CVE, however from right here ahead we’re referring to it as phishing-resistant multifactor authentication.
Let’s stroll by way of the method. I need to create an account on a preferred social media web site. Utilizing my smartphone or pc with passkey help, I select to create a brand new account with a passkey. The location prompts me for my desired username (often my e-mail deal with). My gadget sends the username to the location, and it responds again with my username, a problem, and the location’s area title. My gadget generates a singular cryptographic keypair, shops it safely alongside the location title and username, indicators the problem from the location, and attaches the related public key for the location to now use as my identifier.
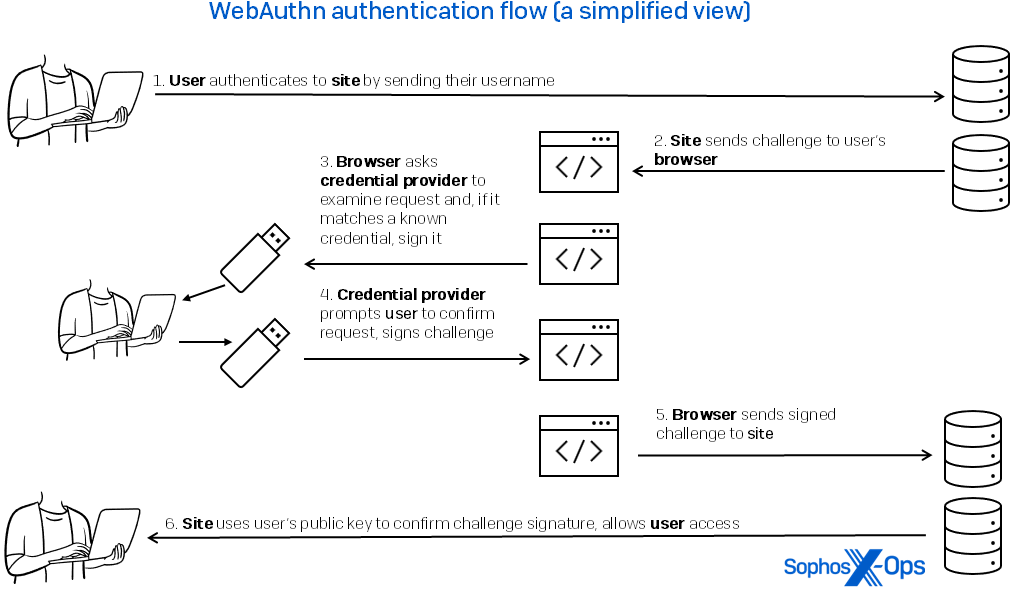
Subsequent time I’m going to this web site, I’ll not want or use a password, which by this definition is only a shared secret and might be stolen or replayed. As an alternative, as proven in Determine 1, I ship the username that’s matched to that web site’s area title. The location responds with a problem. My gadget seems up the important thing for that area title and makes use of it to signal the problem, proving my id.
Determine 1: The user-experience circulation of WebAuthn authorization is clean, with many of the motion occurring among the many person’s credential supplier, the browser, and the location
For extra info, vertx.io has a developer-centric dive into the mechanics of the method.
What might presumably go incorrect?
With this mix of information factors, the important thing can’t simply be stolen or reused, and I can’t be tricked into attempting to signal into an imposter web site with a lookalike area title. (There’s a small assault floor right here as effectively: For those who add a passkey for zuzax.com and I can create a subdomain underneath my management as an attacker, phish.zuzax.com, I can get you to signal a replayed problem.)
Past my gadget, the place the keys are saved determines their security in opposition to theft and abuse. Utilizing {hardware} U2F tokens, like a YubiKey or SmartCard, ensures the keys are locked to that gadget and can’t be extracted and bodily theft is the one sensible possibility. Some {hardware} tokens require a biometric, PIN, or passphrase to unlock as effectively. With the arrival of passkeys, the key keys may be synchronized throughout your OS vendor’s cloud (iCloud, Google Drive, OneDrive) or by way of your password supervisor (Bitwarden, 1password, and so on.) making them extra prone to theft in case your account is compromised.
And, in fact, it needs to be applied. The burden of implementation lies with the websites (the place we now have made moderately fast progress on this previously yr) and, as ever, with enterprises that should allow and use it of their particular environments. This isn’t so totally different to our fixed recommendation to safety practitioners to deal with MFA as primary hygiene (together with patching and disabling pointless RDP), nevertheless it nonetheless needs to be budgeted for and completed.
The final remaining weak spot is the session cookie that will get set upon login, however that’s a subject for an additional article.
It goes each methods (and strikes us ahead)
As a person, I ought to be capable of show my id to my gadget through the use of a PIN, fingerprint, or faceprint, and have the gadget do the work of authenticating each events. That’s an important a part of this transaction — its bidirectionality.
Everyone knows password theft is an issue, and we now have actually solely prolonged their lifetimes by attempting to reinforce them with different flavors of knowledge-based authentication. Info may be and will probably be stolen, intercepted, and replayed. If we really need to have multifactor authentication, we should transfer past data and demand stronger proof.
This is a chance to maneuver past safety being a supply of friction for customers; the truth is, it actively improves safety whereas diminishing the friction. Right this moment’s passkey implementations may be finicky and awkward, however I’m satisfied those that embrace it’ll profit essentially the most and that in brief order we are going to clear up the person interface challenges. We don’t have a alternative. It’s the greatest answer accessible to us and the criminals received’t anticipate us to argue the deserves.