Authored by Lakshya Mathur, Vallabh Chole & Abhishek Karnik
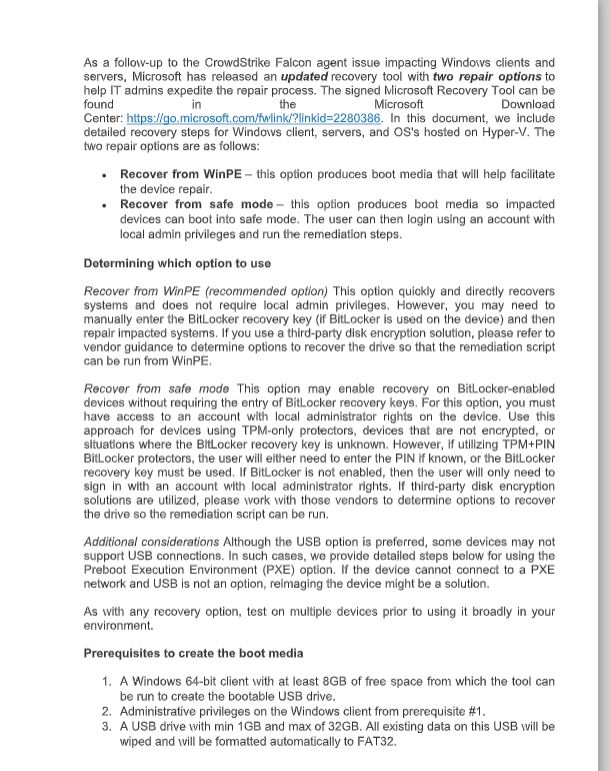
Lately we witnessed one of many most important IT disruptions in historical past, affecting a variety of sectors similar to banking, airways, and emergency companies. On the coronary heart of this disruption was CrowdStrike, recognized for its Falcon enterprise safety options. The difficulty stemmed from a defective safety replace that corrupted the Home windows OS kernel, resulting in a widespread Blue Display screen of Dying (BSOD).
The incident spurred opportunistic behaviors amongst scammers and malware creators. McAfee Labs famous:
- Non-Supply Scams: Early indicators of potential non-delivery scams shortly after the occasion, with some on-line shops shortly advertising merchandise that mocked the CrowdStrike incident.
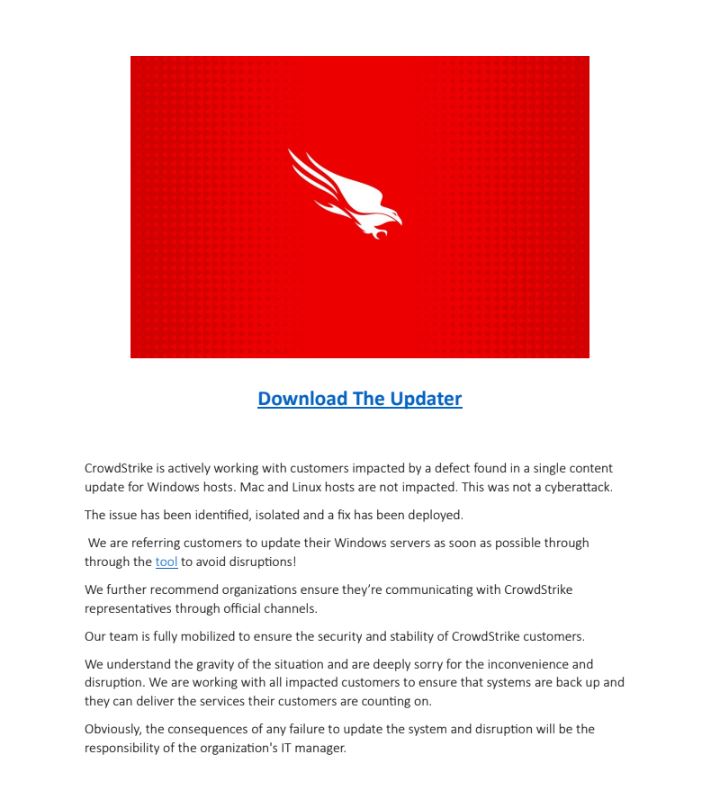
- Area Spoofing: A noticeable surge in area registrations containing the time period “CrowdStrike” following the onset of the outage, there was Scammers might register domains to trick folks into pondering the location is said to a reputable or acquainted firm, to deceive customers into visiting the location for phishing assaults, spreading malware, or gathering delicate data.
- Malware: Malware builders swiftly disguised dangerous software program like Remcos, Wiper, and Stealers as remediation instruments for the outage. Unsuspecting folks might have downloaded this software program in an effort to revive their techniques.
Voice Scams: There have been additionally reviews of robocalls providing help for these points, although these claims haven’t been verified by McAfee.
It’s necessary to notice that Mac and Linux customers had been unaffected by this incident, as the issues had been confined to Home windows techniques. Moreover, since CrowdStrike primarily serves the enterprise market, the crashes predominantly affected enterprise companies somewhat than private client techniques. Nevertheless, the ripple results of the disruption might have precipitated inconvenience for shoppers coping with affected service suppliers, and all shoppers must be additional vigilant concerning unsolicited communications from sources claiming to be an impacted enterprise.
This weblog outlines the assorted malware threats and scams noticed because the outage occurred on Friday, July 19, 2024.
CrowdStrike Themed Malware
- Stealer payload by way of doc-based Macros
This file, which appears to offer restoration pointers, covertly incorporates a macro that silently installs malware designed to steal data.
Malicious doc first web page
An infection Chain
Zip -> Doc -> Cmd.exe -> Curl.exe -> Malicious URL -> Rundll32.exe -> Infostealer DLL payload
Doc file makes use of malicious macros, Curl.exe and Certutil.exe to obtain malicious infostealer DLL payload.
The stealer terminates all working Browser processes after which tries to steal login knowledge and coolies from completely different browsers. All of the stolen knowledge is saved underneath %Temp% folder in a textual content file. This knowledge is distributed to the attacker’s C2 server.
- PDF file downloading Wiper Malware
Attackers use a PDF file and malicious spam to trick victims into downloading a supposed restoration instrument. Clicking the offered hyperlink connects to a malicious URL, which then downloads a Wiper malware payload. This knowledge wiper is extracted underneath %Temp% folder and its fundamental objective is to destroy knowledge saved on the sufferer’s gadget.
PDF file with CrowdStrike remediation instrument theme
An infection Chain
PDF -> Malicious URL -> Zip -> Wiper payload
- Remcos RAT delivered with CrowdStrike Repair theme
Zip recordsdata labeled “crowdstrike-hotfix.zip” that carry Hijack Loader malware, which then deploys Remcos RAT, have been noticed being distributed to victims. Moreover, the zip file features a textual content file with directions on easy methods to execute the .exe file to resolve the difficulty.
Remcos RAT permits attackers to take distant entry to the sufferer’s machine and steal delicate data from their system.
CrowdStrike Outage Impersonated Domains & URLs
As soon as the outage gained media consideration, quite a few domains containing the phrase “crowdstrike” had been registered, aimed toward manipulating search engine outcomes. Over the weekend, a number of of those newly registered domains grew to become lively.
Listed below are some examples:
https[:]//pay.crowdstrikerecovery[.]com/ , pay[.]clown-strike[.]com , pay[.]strikeralliance[.]com
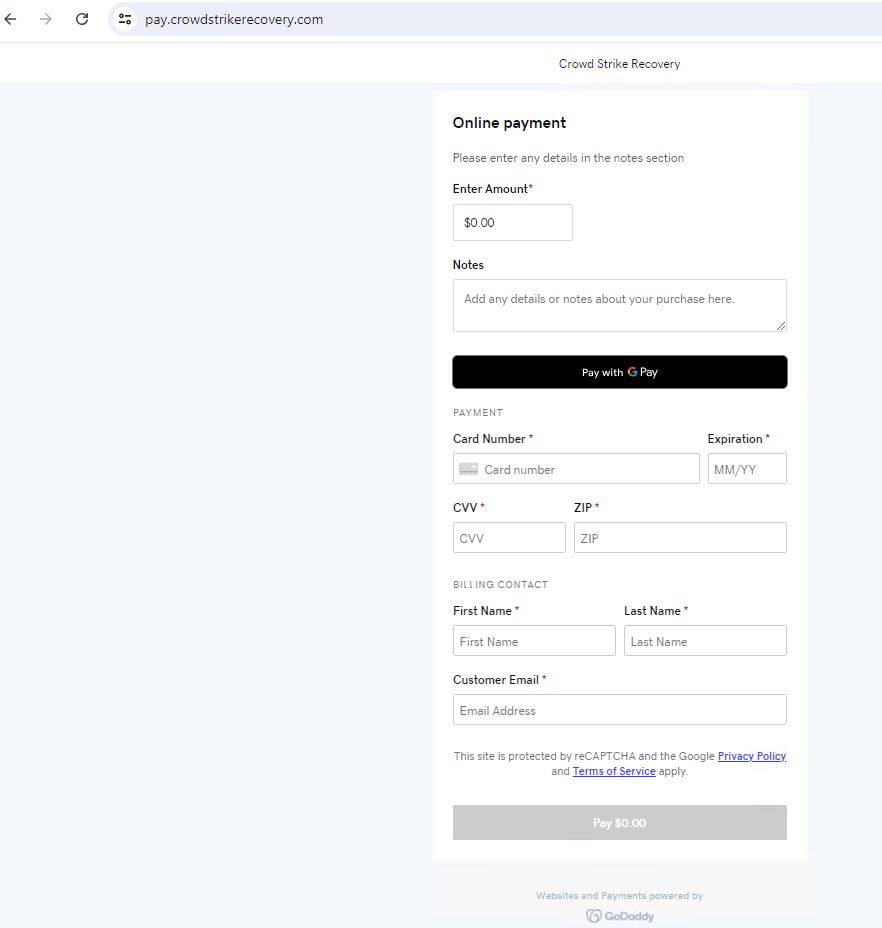
The rogue domains result in the funds web page
Crowdstrike-helpdesk[.]com
Domains which might be at present parked and never reside
- Moreover, quite a few cryptocurrency wallets had been established utilizing a theme impressed by CrowdStrike.
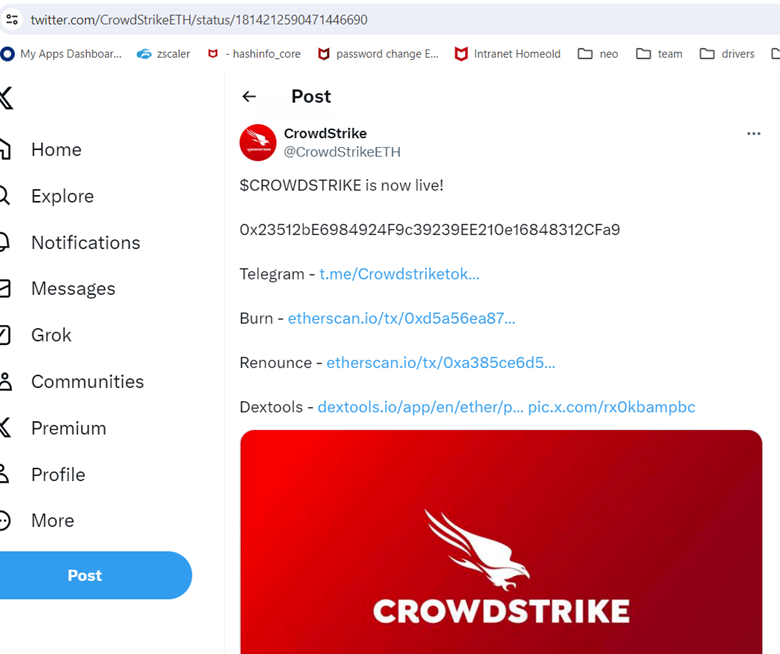
twitter[.]com/CrowdStrikeETH/
Another wallets associated to CrowdStrike Outage aside from above talked about.
bitcoin:1M8jsPNgELuoXXXXXXXXXXXyDNvaxXLsoT
ethereum:0x1AEAe8c6XXXXXXXXXXX76ac49bb3816A4eB4455b
To summarize, the vast majority of shoppers utilizing gadgets at house may not be straight affected by this incident. Nevertheless, when you’ve got skilled points similar to airline delays, banking disruptions, healthcare, or related service interruptions since July nineteenth, they might be associated to this occasion.
Be cautious in the event you obtain telephone calls, SMS messages, emails, or any type of contact providing help to treatment this case. Until you use a enterprise that makes use of CrowdStrike, you’re probably not affected.
For the remediation course of and steps comply with the official article from CrowdStrike – https://www.crowdstrike.com/falcon-content-update-remediation-and-guidance-hub/
Listing of recognized malware hashes and probably undesirable domains:
| Hashes | Sort |
| 96dec6e07229201a02f538310815c695cf6147c548ff1c6a0def2fe38f3dcbc8 | Wiper Zip |
| 803727ccdf441e49096f3fd48107a5fe55c56c080f46773cd649c9e55ec1be61 | Stealer Docx |
| c44506fe6e1ede5a104008755abf5b6ace51f1a84ad656a2dccc7f2c39c0eca2 | RemcosRAT Zip |
| 19001dd441e50233d7f0addb4fcd405a70ac3d5e310ff20b331d6f1a29c634f0 | Wiper PDF |
| d6d5ff8e9dc6d2b195a6715280c2f1ba471048a7ce68d256040672b801fda0ea | RemcosRAT DLL |
| 4491901eff338ab52c85a77a3fbd3ce80fda738046ee3b7da7be468da5b331a3 | Wiper EXE |
| Domains |
| hxxps://crowdstrike0day[.]com |
| hxxps://crowdstrikefix[.]com |
| hxxps://crowdstrike-bsod[.]com |
| hxxps://crowdstrikedoomsday[.]com |
| hxxps://crowdstrikedown[.]website |
| hxxps://www[.]crowdstriketoken[.]com |
| hxxps://crowdstriketoken[.]com |
| hxxps://crowdstrikebsod[.]com |
| hxxps://fix-crowdstrike-apocalypse[.]com |
| hxxp://crowdfalcon-immed-update[.]com |
| hxxp://crowdstrikefix[.]com |
| hxxp://fix-crowdstrike-apocalypse[.]com |
| hxxps://crowdstrike[.]phpartners[.]org |
| hxxps://www[.]crowdstrikefix[.]com |
| hxxp://crowdstrikebsod[.]com |
| hxxp://crowdstrikeclaim[.]com |
| hxxp://crowdstrikeupdate[.]com |
| hxxp://crowdstrike[.]buzz |
| hxxp://crowdstrike0day[.]com |
| hxxp://crowdstrike-bsod[.]com |
| hxxp://crowdstrikedoomsday[.]com |
| hxxp://crowdstrikedown[.]website |
| hxxp://crowdstrikefix[.]zip |
| hxxp://crowdstrike-helpdesk[.]com |
| hxxp://crowdstrikeoutage[.]data |
| hxxp://crowdstrikereport[.]com |
| hxxp://crowdstriketoken[.]com |
| hxxp://crowdstuck[.]org |
| hxxp://fix-crowdstrike-bsod[.]com |
| hxxp://microsoftcrowdstrike[.]com |
| hxxp://microsoftcrowdstrike[.]com/ |
| hxxp://whatiscrowdstrike[.]com |
| hxxp://www[.]crowdstrikefix[.]com |


