How To
Password leaks are more and more frequent and determining whether or not the keys to your individual kingdom have been uncovered is likely to be tough – until you already know the place to look
03 Jun 2024
•
,
6 min. learn

Just lately, I got here throughout a report detailing “the mom of all breaches” – or to be extra actual, the leak of an unlimited compilation of knowledge that was stolen throughout numerous assaults on varied firms and on-line providers, together with LinkedIn and Twitter (now X). The information cache reportedly comprised an astonishing 26 billion data that had been replete with a variety of delicate data, together with authorities knowledge and folks’s login credentials.
Whereas this isn’t the primary time {that a} large stash of person knowledge has been there for the taking, the sheer variety of compromised data eclipsed earlier recognized leaks (and their compilations). Simply take into account that the notorious Cam4 knowledge leak in 2020 uncovered near 11 billion data of varied sorts and the breach at Yahoo in 2013 compromised all three billion person accounts. Lest we overlook: the aptly named Assortment No. 1, which made it onto the open web in 2019, uncovered 773 million login names and passwords beforehand stolen from varied organizations, earlier than being adopted by 4 extra “collections” of this sort simply weeks later.
The place does that depart us? Maybe the important thing takeaway is that even should you apply stringent private safety measures, your account credentials can nonetheless get caught up in such collections, primarily as a result of breaches at massive firms. This begs the query – how will you discover out in case your credentials have been compromised? Learn on.
Firm disclosures
Enterprise could also be topic to particular regulatory necessities that oblige them to reveal hacking incidents and unpatched vulnerabilities. Within the U.S., for example, publicly-traded firms have to report “materials” cyber-incidents to the U.S. Securities and Change Fee (SEC) inside 96 hours, or 4 enterprise days, of their incidence.
How does this assist common people? Such transparency could not solely assist construct belief with prospects nevertheless it additionally informs them if their accounts or knowledge have been compromised. Firms sometimes notify customers of knowledge breaches by way of electronic mail, however since SEC filings are public, chances are you’ll find out about such incidents from different sources, presumably even information stories overlaying them.
Have I been pwned?
Maybe the best means of checking whether or not a few of your knowledge, reminiscent of your electronic mail tackle or any of your passwords, has been uncovered in a knowledge leak is to go to haveibeenpwned.com. The positioning encompasses a free instrument that may inform you when and the place your knowledge popped up.
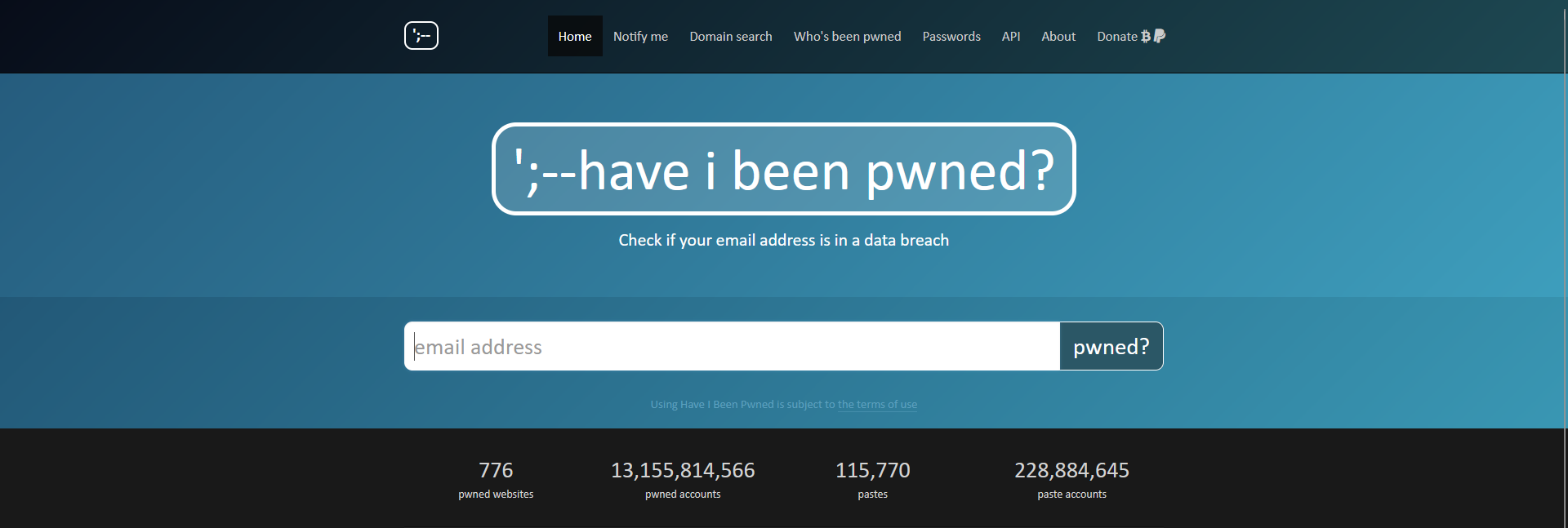
Merely enter your electronic mail tackle, click on “pwned?” and voila! A message will seem informing you of the safety standing of your credentials in addition to the precise leak they had been caught up in. For many who are fortunate, the end result shall be inexperienced, signaling no pwnage, and for these much less lucky, the positioning will flip pink, itemizing wherein knowledge leak(s) your credentials appeared.
Internet browsers
Some internet browsers, together with Google Chrome and Firefox, can examine in case your passwords have been included in any recognized knowledge leak. Chrome can even suggest stronger passwords by way of its password supervisor module or provide different options to reinforce your password safety.
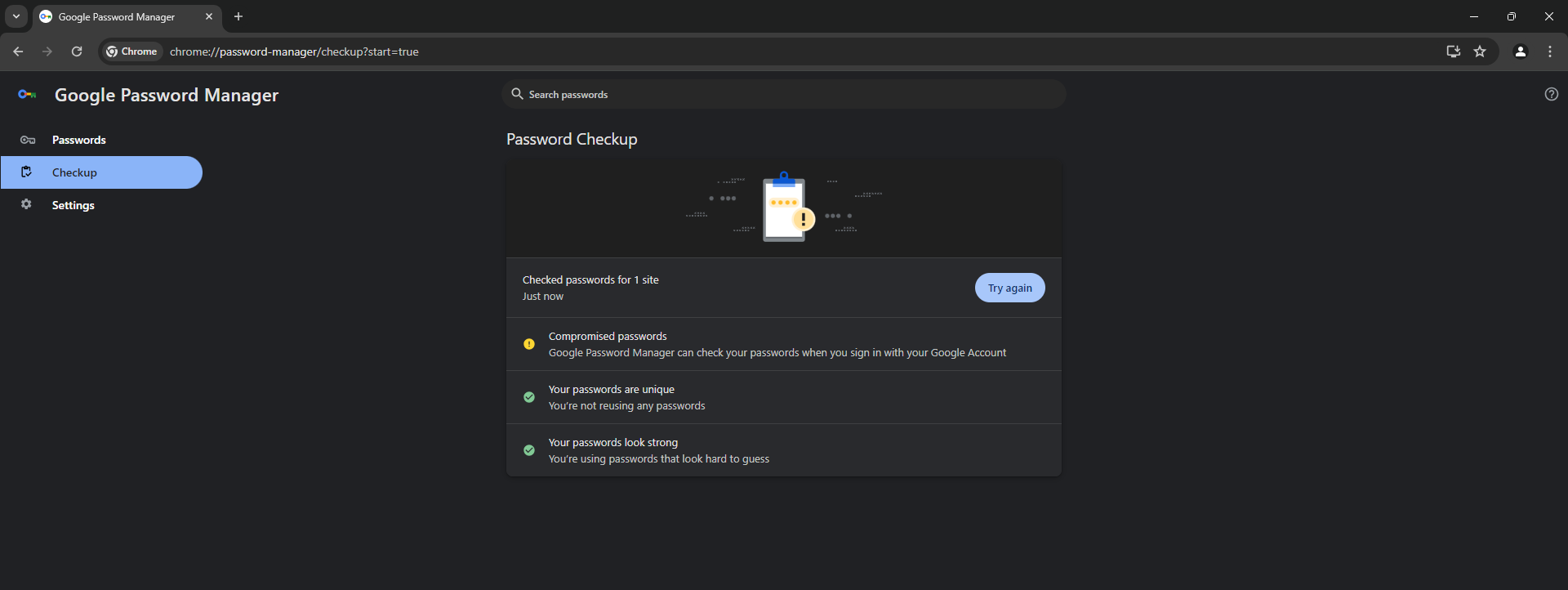
Nonetheless, chances are you’ll need to up your sport additional and use a devoted password supervisor that has a confirmed observe file of taking knowledge safety severely, together with by way of sturdy encryption. These instruments are additionally usually bundled with respected multi-layered safety software program.
Password managers
Password managers are invaluable in the case of juggling a big assortment of login credentials, as they can’t solely securely retailer them, however generate advanced and distinctive passwords for every of your on-line accounts. It ought to go with out saying, nevertheless, that you’ll want to use a powerful however memorable grasp password that holds the keys to your kingdom.
Alternatively, these password vaults aren’t resistant to compromise and stay engaging targets for malicious actors, for instance because of credential-stuffing assaults or assaults exploiting software program vulnerabilities. Even so, the advantages – which embody built-in leaked password checks and integration with two-factor authentication (2FA) schemes which can be accessible on many on-line platforms lately – outweigh the dangers.
How one can stop (the impression of) credential leaks?
Now, what about stopping leaks within the first place? Can a median web person shield themselves towards credential leaks? In that case, how? Certainly, how will you maintain your accounts secure?
To begin with, and we will’t stress this sufficient, don’t depend on passwords alone. As an alternative, make sure that your accounts are protected by two types of identification. To that finish, use two-factor authentication (2FA) on each service that allows it, ideally within the type of a devoted safety key for 2FA or an authenticator app reminiscent of Microsoft Authenticator or Google Authenticator. It will make it considerably tougher for attackers to achieve unauthorized entry to your accounts – even when they’ve by some means acquired their palms in your password(s).
Associated studying: Microsoft: 99.9 p.c of hacked accounts didn’t use MFA
As for password safety as such, keep away from writing your logins down on paper or storing them in a note-taking app. It’s additionally higher to keep away from storing your account credentials in internet browsers, which normally solely retailer them as easy textual content recordsdata, making them weak to knowledge exfiltration by malware.
Different primary account safety suggestions contain utilizing sturdy passwords, which make it tougher for crooks to commit brute-force assaults. Steer clear of easy and quick passwords, reminiscent of a phrase and a quantity. When doubtful, use this ESET instrument to generate sturdy and distinctive passwords for every of your accounts.
Associated studying: How usually do you have to change your passwords?
It’s additionally good observe to use passphrases, which may be safer in addition to simpler to recollect. As an alternative of random letter and image mixtures, they comprise a sequence of phrases which can be sprinkled by capitals and presumably particular characters.
Likewise, use a special password for every of your accounts to forestall assaults reminiscent of credential stuffing, which takes benefit of individuals’s penchant for reusing the identical credentials throughout a number of on-line providers.
A more moderen method to authentication depends on passwordless logins, reminiscent of passkeys, and there are additionally different login strategies like safety tokens, one-time codes or biometrics to confirm account possession throughout a number of gadgets and methods.
Firm-side prevention
Firms have to spend money on safety options, reminiscent of detection and response software program, that may stop breaches and safety incidents. Moreover, organizations have to proactively shrink their assault floor and react as quickly as one thing suspicious is detected. Vulnerability administration can be essential, as staying on prime of recognized software program loopholes and patching them in a well timed method helps stop exploitation by cybercriminals.
In the meantime, the ever-present human issue can even set off a compromise, for instance after an worker opens a suspicious electronic mail attachment or clicks a hyperlink. Because of this the significance of cybersecurity consciousness coaching and endpoint/mail safety can’t be understated.
Associated studying: Strengthening the weakest hyperlink: prime 3 safety consciousness matters on your staff
Any firm that severely tackles knowledge safety also needs to take into account a knowledge loss prevention (DLP) resolution and implement a sturdy backup coverage.
Moreover, dealing with massive volumes of consumer and worker knowledge requires stringent encryption practices. Native encryption of credentials can safeguard such delicate knowledge, making it tough for attackers to use stolen data with out entry to the corresponding encryption keys.
All in all, there is no such thing as a one-size-fits-all resolution, and each firm must tailor its knowledge safety technique to its particular wants and adapt to the evolving risk panorama. Nonetheless, a mix of cybersecurity finest practices will go a good distance in the direction of stopping knowledge breaches and leaks.


