Menace actors are exploiting an unspecified zero-day vulnerability in Cambium Networks cnPilot routers to deploy a variant of the AISURU botnet known as AIRASHI to hold out distributed denial-of-service (DDoS) assaults.
In response to QiAnXin XLab, the assaults have leveraged the safety flaw since June 2024. Extra particulars in regards to the shortcomings have been withheld to forestall additional abuse.
A few of the different flaws weaponized by the distributed denial-of-service (DDoS) botnet embrace CVE-2013-3307, CVE-2016-20016, CVE-2017-5259, CVE-2018-14558, CVE-2020-25499, CVE-2020-8515, CVE-2022-3573, CVE-2022-40005, CVE-2022-44149, CVE-2023-28771, in addition to these impacting AVTECH IP cameras, LILIN DVRs, and Shenzhen TVT units.
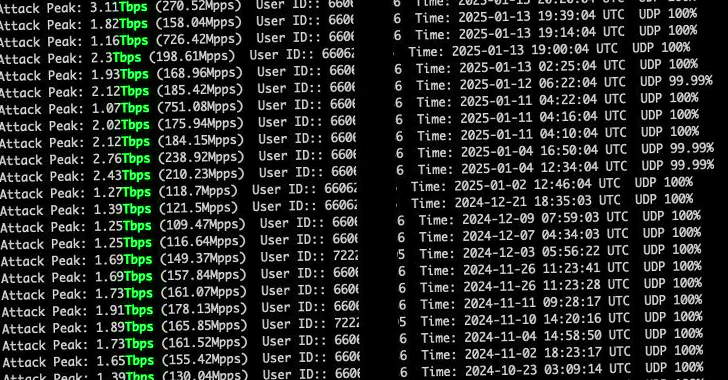
“The operator of AIRASHI has been posting their DDoS functionality take a look at outcomes on Telegram,” XLab stated. “From historic knowledge, it may be noticed that the assault capability of the AIRASHI botnet stays steady round 1-3 Tbps.”
A majority of the compromised units are positioned in Brazil, Russia, Vietnam, and Indonesia, with China, the USA, Poland, and Russia changing into the first targets of the malicious swarm.
AIRASHI is a variant of the AISURU (aka NAKOTNE) botnet that was beforehand flagged by the cybersecurity firm in August 2024 in reference to a DDoS assault concentrating on Steam across the identical time coinciding with the launch of the sport Black Fantasy: Wukong.
A often up to date botnet, choose variations of AIRASHI have additionally been discovered incorporating proxyware performance, indicating that the risk actors intend to increase their companies past facilitating DDoS assaults.
AISURU is alleged to have briefly suspended its assault actions in September 2024, just for it to reappear a month later with up to date options (dubbed kitty) and refreshed once more a second time on the finish of November (aka AIRASHI).
“The kitty pattern started spreading in early October 2024,” XLab famous. “In comparison with earlier AISURU samples, it has simplified the community protocol. By the tip of October, it began utilizing SOCKS5 proxies to speak with the C2 server.”
AIRASHI, however, is available in a minimum of two completely different flavors –
- AIRASHI-DDoS (first detected in late October), which primarily focuses on DDoS assaults, but additionally helps arbitrary command execution and reverse shell entry
- AIRASHI-Proxy (first detected in early December), which is a modified model of AIRASHI-DDoS with proxy performance
The botnet, along with constantly tweaking its strategies to acquire the C2 server particulars through DNS queries, depends on a very new community protocol that includes HMAC-SHA256 and CHACHA20 algorithms for communication. Moreover, AIRASHI-DDoS helps 13 message sorts, whereas AIRASHI-Proxy helps solely 5 message sorts.
The findings present that unhealthy actors proceed to take advantage of vulnerabilities in IoT units each as an preliminary entry vector and for constructing botnets that use them to place added weight behind highly effective DDoS assaults.
The event comes as QiAnXin make clear a cross-platform backdoor named alphatronBot that has focused the Chinese language authorities and enterprises to enlist contaminated Home windows and Linux programs right into a botnet. Lively for the reason that begin of 2023, the malware adopted a reliable open-source peer-to-peer (P2P) chat utility named PeerChat to speak to different contaminated nodes.
The decentralized nature of the P2P protocol implies that an attacker can challenge instructions by any of the compromised nodes with out having to route them by a single C2 server, thus making the botnet much more resilient to takedowns.
“The 700+ P2P networks constructed into the backdoor encompass contaminated community system elements from 80 international locations and territories,” the corporate stated. “The nodes contain MikroTik routers, Hikvision cameras, VPS servers, DLink routers, CPE units, and so forth.”
Final 12 months, XLab additionally detailed a complicated and stealthy payload supply framework codenamed DarkCracks that exploits compromised GLPI and WordPress websites to perform as downloaders and C2 servers.
“Its main goals are to assemble delicate info from contaminated units, keep long-term entry, and use the compromised, steady, high-performance units as relay nodes to manage different units or ship malicious payloads, successfully obfuscating the attacker’s footprint,” it stated.
“The compromised programs had been discovered to belong to vital infrastructure throughout completely different international locations, together with faculty web sites, public transportation programs, and jail customer programs.”