Govt Abstract
In September 2024, LevelBlue carried out a complete menace hunt focusing on artifacts indicative of Phishing-as-a-Service (PhaaS) exercise throughout our monitored buyer fleet. In the course of the investigation, the LevelBlue Managed Detection and Response (MDR) Blue Workforce found a brand new PhaaS package, now recognized as RaccoonO365. The hunt confirmed true-positive compromises of Workplace 365 accounts, prompting swift buyer notifications and steering on remediation actions. The preliminary findings have been handed over to the LevelBlue Labs Risk Intelligence staff, which additional uncovered extra infrastructure and deconstructed the package’s JavaScript. This evaluation offered crucial insights into the options and capabilities of the rising PhaaS package.
Investigation
An anomalous artifact recognized throughout a buyer investigation was escalated to the Risk Looking staff for evaluation. Additional examination revealed that this artifact was linked to a selected Phishing-as-a-Service (PhaaS) platform often called ‘RaccoonO365’. Promoted as a cutting-edge phishing toolkit, it makes use of a customized Person Agent, domains mimicking Microsoft O365 companies, and Cloudflare infrastructure. Together with these findings in our threat-hunting queries led to 2 extra discoveries tallying three complete detections throughout the shopper fleet. The 2 proactive detections recognized occasions acquired, however no alarms have been triggered within the concerned buyer’s LevelBlue USM Wherever cases. The third reactive detection was a confirmed enterprise e-mail compromise (BEC), detected after triggering an alarm. The menace actor utilized the consumer agent ‘RaccoonO365’ previous to the enterprise e-mail compromise detection that means there was a brief interval of unauthorized entry that went undetected. Every incidence was triaged individually, and investigations have been carried out in all three buyer cases referring to the noticed exercise. Partnering with LevelBlue Labs, a brand new Correlation Rule was created to go looking particularly for a RaccoonO365 consumer agent inside related logs. As well as, the LevelBlue Labs staff uncovered extra structural and descriptive options attributed to RaccoonO365, which later was changed into a Pulse Indicator of Compromise (IOC) detection.
Expanded Investigation
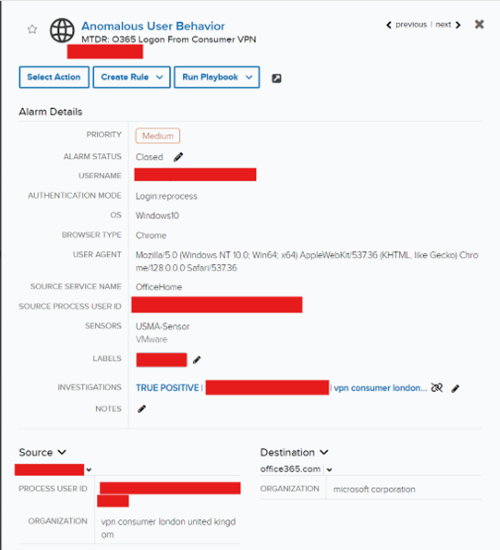
Alarm and USMA log assessment
1. An unrelated potential enterprise e-mail compromise (BEC) alarm was acquired and triaged by the LevelBlue MDR SOC. The recognized consumer utilized a overseas VPN to efficiently log into buyer’s Microsoft Workplace setting. A customized alarm rule was created on account of its excessive likelihood of being a True Constructive. Whereas conducting their investigation, they uncovered a suspicious consumer agent associated to the compromised e-mail tackle –RaccoonO365.
2. Data was handed off to LevelBlue Risk Hunters to conduct additional inner and exterior analysis for the recognized artifact.
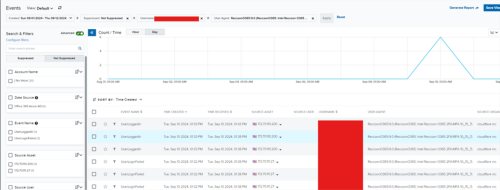
3. A devoted menace hunter carried out a assessment of occasions together with the topic consumer agent. Occasion logs have been in contrast towards one another and the profitable logins offered extra key knowledge factors.
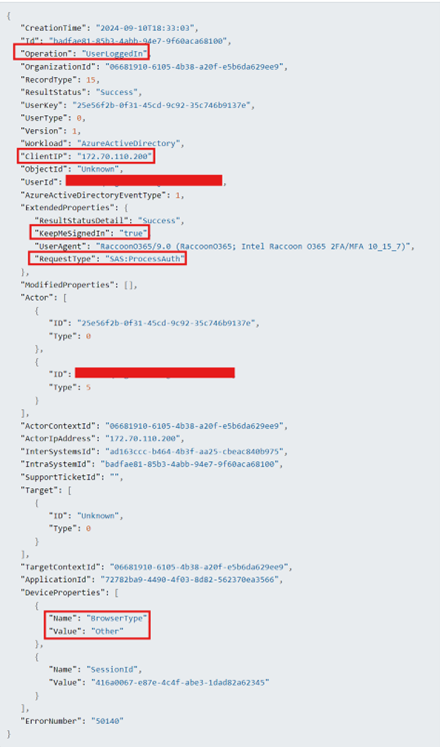
Shared Entry Signature (SAS) authentication
- “SAS authentication” refers to a way of consumer entry management utilizing a “Shared Entry Signature” (SAS) token, which basically grants short-term, restricted entry to particular sources inside a cloud platform like Azure. This enables customers to entry knowledge with out straight sharing the complete account entry key, by offering a novel token containing the useful resource URL and an expiry time, signed with a cryptographic key, to authenticate entry to that useful resource.
4. Broad seek for recognized consumer agent “RaccoonO365/9.0 (RaccoonO365; Intel Raccoon O365 2FA/MFA 10_15_7)” throughout whole buyer fleet.
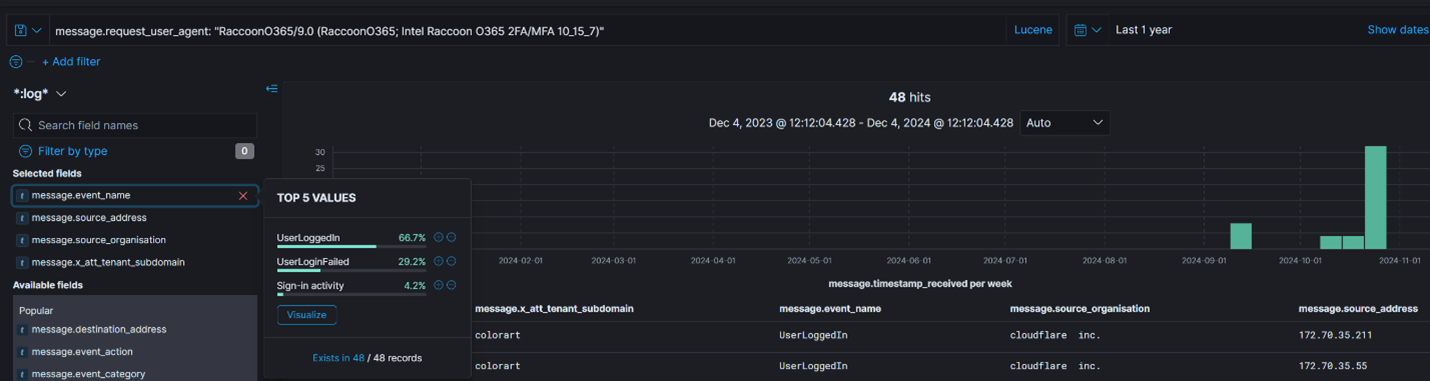
48 complete occurrences during the last 12 months throughout three buyer cases. Cloudflare noticed as the principle supply ISP. Subnets 172.69.xx.xx, 172.70.xx.xx, and 172.71.xx.xx recognized in exercise. Three occasion names noticed, ‘UserLoggedIn’, ‘UserLoginFailed’ and ‘Signal-in exercise’.
5. Seek for failed login occasions together with consumer agent “RaccoonO365/9.0 (RaccoonO365; Intel Raccoon O365 2FA/MFA 10_15_7)” to establish cause for failure.
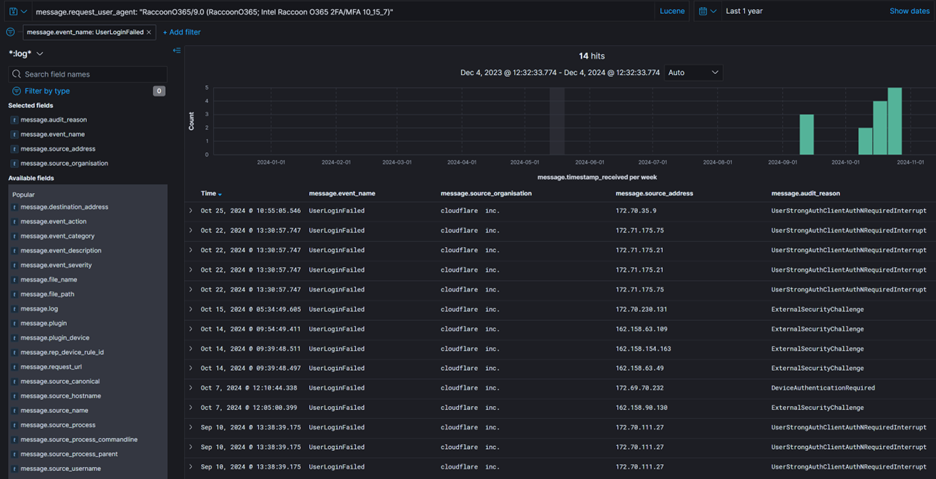
Recognized justifications for failed logins have been: UserStrongAuthClientAuthNRequiredInterrupt – Sturdy authentication is required and the consumer didn’t cross MFA problem (AADSTS50074) ExternalSecurityChallenge – Exterior safety problem was not happy (AADSTS50158) DeviceAuthenticationRequired – System authentication is required (AADSTS50097)
6. Seek for ‘Signal-in exercise’ occasions together with consumer agent “RaccoonO365/9.0 (RaccoonO365; Intel Raccoon O365 2FA/MFA 10_15_7)”.
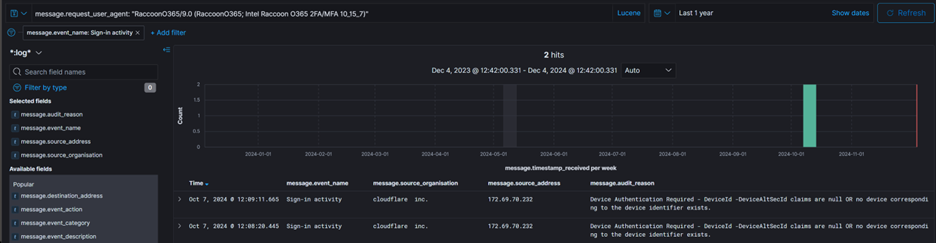
Noticed occasions have been denied, nonetheless findings included a brand new knowledge supply ‘Azure AD Signal In’ to incorporate in our search –no extra findings noticed underneath alternate knowledge supply (not pictured).
7. Alarm log seek for consumer agent “RaccoonO365/9.0 (RaccoonO365; Intel Raccoon O365 2FA/MFA 10_15_7)” inside recognized knowledge sources ‘Workplace 365 Audit’, and ‘Azure AD Signal In’.
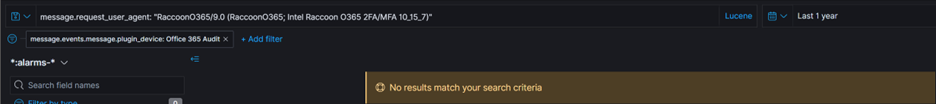
No findings throughout the final 12 months.
SOC Investigations
1. Topic investigation A was created previous to menace hunt in response to an alarm acquired by the MDR SOC. If unauthorized VPN entry to a goal community is noticed, it must be addressed quickly by revoking concerned lively periods and resetting the affected e-mail accounts in addition to MFA tokens.
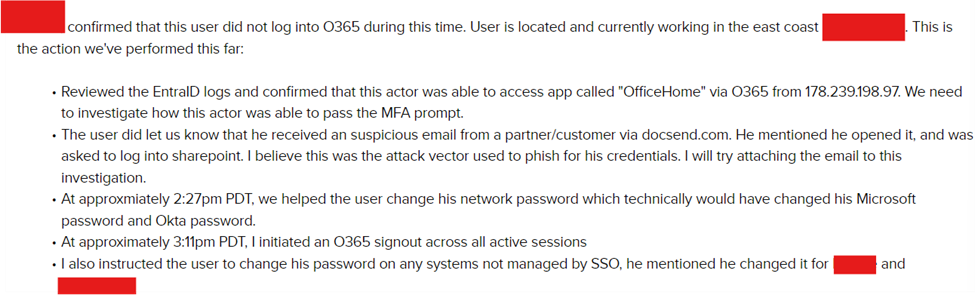
Additional triage was carried out through buyer request.
The LevelBlue MDR SOC was in a position to establish the supply URL that contributed to the enterprise e-mail compromise –though the menace actor eliminated the malicious recordsdata from the shared repository.
2. Risk Hunt Investigations B and C have been opened by the LevelBlue MDR SOC, however didn’t embody a corresponding alarm inside every buyer occasion respectively. Investigation B concerned a consumer who had beforehand been compromised not too long ago using the topic consumer agent RaccoonO365. The LevelBlue MDR SOC was in a position to monitor down the e-mail sender of the originating phishing e-mail.
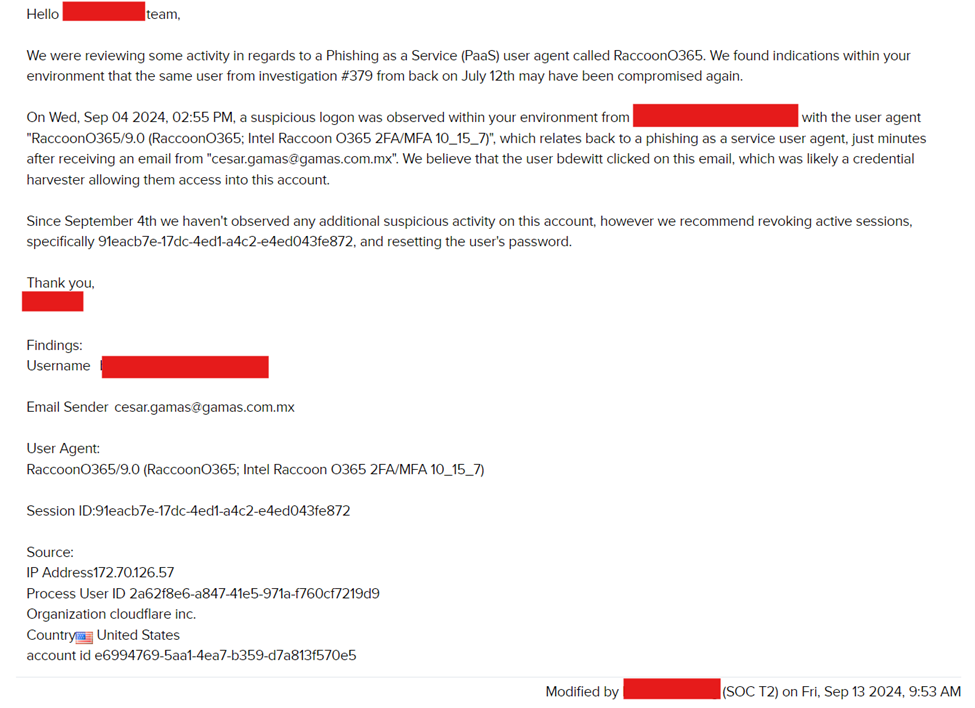
MDR SOC created an investigation primarily based on the collaboration with Risk Hunters and findings.
3. Investigation C and its included occasions didn’t comprise the topic consumer agent RaccoonO365/9.0 (RaccoonO365; Intel Raccoon O365 2FA/MFA 10_15_7). The Cloudflare subnet vary 172.71.xx.xx recognized beforehand, offered IPs that have been utilized by a buyer e-mail account.
MDR SOC created an investigation primarily based on the collaboration with Risk Hunters and findings.
Cloudflare CAPTCHA Turnstile
The Cloudflare ISP “Turnstile” providing has develop into more and more in style inside PhaaS kits. This know-how behind the providing from Cloudflare permits for automated rotation of problem web page choices that give phishing campaigns false legitimacy within the eyes of victims and filter out challenges which might be much less efficient. Related machine studying fashions can go as far as to detect whether or not a topic consumer has handed beforehand administered CAPTCHA challenges. The menace actor’s finish aim is to make sure that the phishing hyperlink is clicked on by a human consumer quite than a bot. One other ancillary profit granted through the usage of Cloudflare’s CAPTCHA is the prevention of bots and automatic net scans.
Technical Analyses – LevelBlue Labs
RaccoonO365 is designed to focus on Microsoft 365 and Outlook customers, specializing in enterprise customers and cloud dependent enterprises. Its main aim is to bypass multi-factor authentication (MFA) protections and steal session cookies by subtle phishing strategies. This package is obtainable by a subscription mannequin on Telegram, providing numerous pricing tiers. Subscribers obtain entry to phishing templates, instruments for producing dynamic URLs, and performance to steal session cookies. The package makes use of Base64 encoding and XOR obfuscation for JavaScript, alongside session cookie hijacking, to successfully bypass MFA. To stay stealthy and improve marketing campaign longevity, RaccoonO365 makes use of Cloudflare Turnstile. This service gives CAPTCHA challenges for filtering out bots and lowering detection by safety techniques. This service can be utilized by infamous PaaS platforms similar to Tycoon2FA, Greatness, or ONNX. Initially, the Risk Actor promoted the Phishing package by a Telegram channel and the web site raccoono365 [.]com, however these are now not publicly accessible. Two extra web sites have been later created, raccoono365 [.]web and raccoono365 [.]org.

Determine 1: Raccoono365 web site (raccoono365[.]com)
Nonetheless, the Risk Actor had transitioned to a brand new area, walkingdead0365[.]com, which seems to function the admin panel for the RaccoonO365 phishing package.
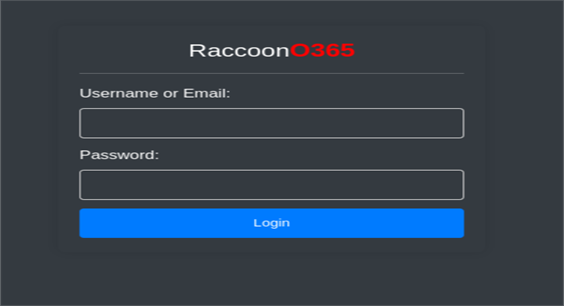
Determine 2: RaccoonO365 Login Web page (walkingdead0365[.]com)
On September 23, Trustwave printed an insightful weblog detailing numerous phishing kits, together with RaccoonO365. The weblog highlighted the rising sophistication and accessibility of phishing-as-a-service (PaaS) platforms. Trustwave shared a screenshot from the Raccoon Telegram channel, showcasing its subscription-based pricing mannequin.
The RaccoonO365 phishing package operates on a subscription-based mannequin with tiered pricing, making it accessible to cybercriminals of various budgets. Plans vary from a 4-day free trial for $50 to longer durations like 11 days for $75, 20 days for $175, one month for $250, and two months for $450—considerably discounted from their authentic costs. When the RaccoonO365 license expires, a message will seem on the web site claiming that the license needs to be renewed.
Determine 3: License Expiration
The infrastructure supporting the RaccoonO365 phishing package is often hosted in IPs underneath Cloudflare’s ASN AS13335. The recognized domains are strategically crafted to impersonate Microsoft Workplace 365 companies, incorporating key phrases similar to “drive,” “file,” “cloud,” “doc,” “suite,” and “shared” to deceive customers.
HTML/Javascript Evaluation
Evaluation of user-agent strings referencing RaccoonO365 prompted additional investigation into this uncommon identify. An preliminary search indicated that RaccoonO365 is a newly recognized phishing package with restricted public reporting. As of scripting this weblog, an organization by the identify of Morado not too long ago printed data on the PaaS package not beforehand reported. The safety staff uncovered a number of insights that overlapped with the findings of LevelBlue Labs.
As quickly because the focused consumer is offered with a malicious URL hyperlink, the redirection HTML web page reveals indicators of obfuscation and hex encoding that dynamically masses a decoded block of HTML/Javascript.
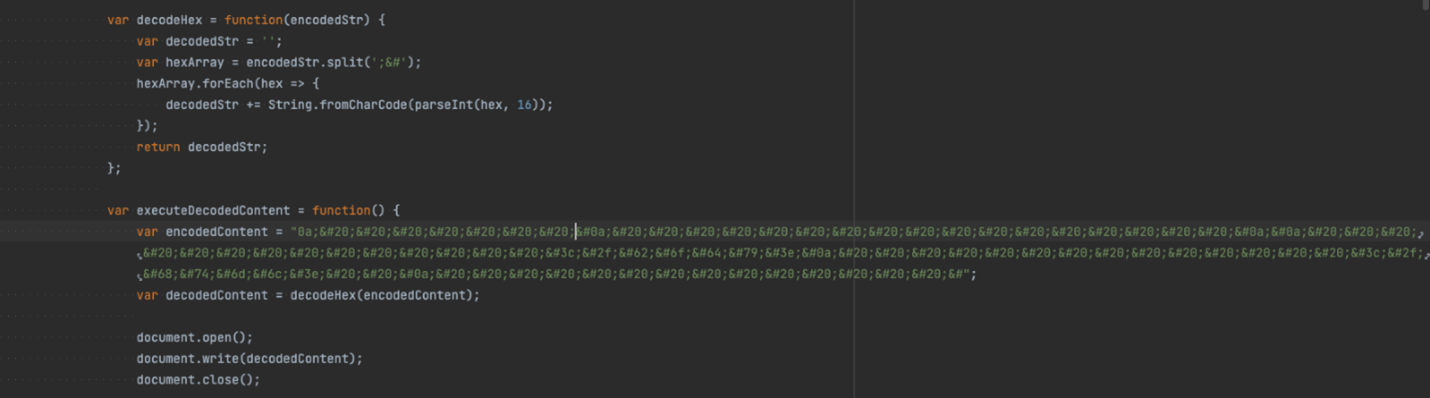
Determine 4: encodedContent
The decoded Javascript block seems by the visiting consumer’s cookies and checks if the ‘visited’ tag is current in any of them. If the visited tag is current, the visiting consumer will get redirected to the official Microsoft web site.
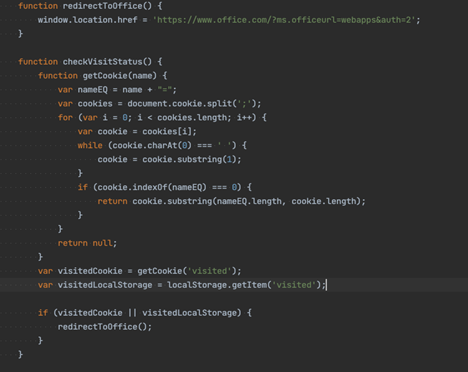
Determine 5: checkVisitStatus()
The code additionally seems to enumerate the visiting consumer brokers and makes an attempt to establish them through an inventory in the event that they go to from a cell phone. It seems that the makers of RaccoonO365 usually are not too involved with customers accessing the phishing domains from cell units, because the anti-debugging options usually are not enabled if visiting from a listed cell consumer agent.
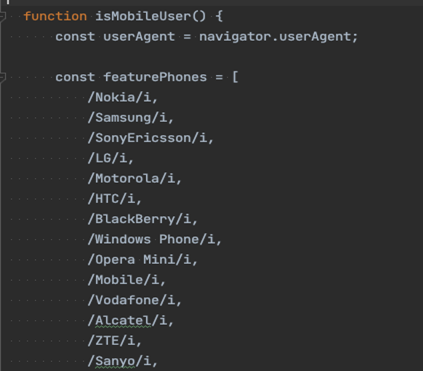
Determine 6: Cellular Person Agent Checklist
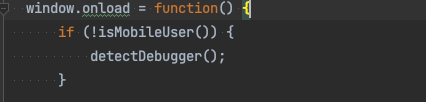
Determine 7: Not Cellular Person
Increasing on the visiting consumer, the code makes an attempt to detect the net browser getting used whereas visiting the Phishing web page. If the visiting consumer is utilizing both Chrome, Firefox, or Edge, anti-analysis features similar to setInterval(), are used to detect when the debugging instruments are opened by the net browser.
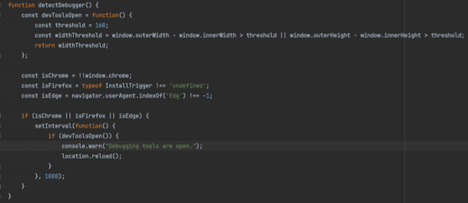
Determine 8: Chrome, Firefox, Edge
The Javascript additionally goals to detect scanning consumer brokers trying to entry/crawl by the phishing domains. The hardcoded listing seems for frequent scanning brokers similar to scrapy, googlebot, curl, amongst many extra. After validating the consumer agent just isn’t a part of the hardcoded lists, it then proceeds to run the notblocked() perform which proceeds to shows a faux PDF picture file.
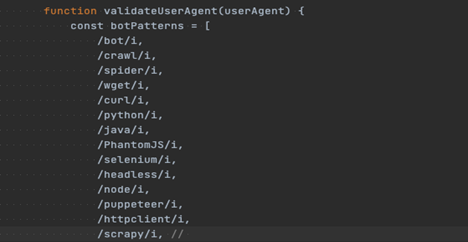
Determine 9: Bot Patterns
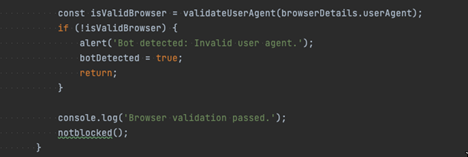
Determine 10: Bot Detected
Upon touchdown on the ultimate phishing web page the place consumer is prompted to enter their Workplace 365 username and password, the LevelBlue Labs staff uncovered what seems to be configuration settings which point out how RaccoonO365 handles authentication flows between the phished consumer, relaying server, and legit Microsoft companies.
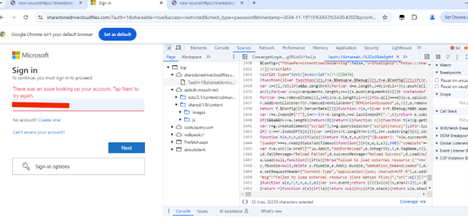
Determine 11: Phishing Website
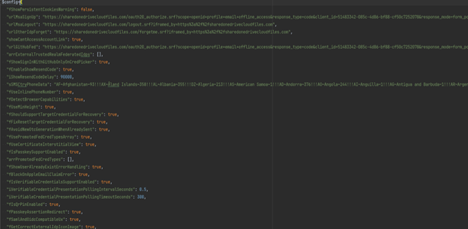
Determine 12: Configuration Choices
For instance, we see a number of redirection URLs set for when a consumer makes an attempt to reset their password. The password reset request is first despatched to the official Microsoft web site https://passwordreset.microsoftonline.com/, and upon finishing the reset, the response is then redirected again to the phishing area.
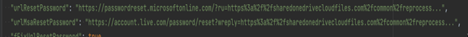
Determine 13: Password Reset
Different config settings similar to fEnableShowResendCode & iShowResendCodeDelay seem to handle resend code behaviors in two-factor authentication flows:
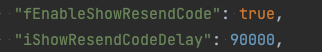
Determine 14: MFA Choices
Primarily based on latest reporting by the safety staff Morado, the RaccoonO365 phishing-as-a-service (PhaaS) package is present process important evolution, with updates to its infrastructure and options anticipated. LevelBlue Labs will proceed monitoring these developments, incorporating new options and indicators of compromise (IOCs) to boost protections for USM Wherever customers. Leveraging the insights from deconstructing the phishing package, the LevelBlue staff labored carefully with affected clients to implement swift remediation actions, mitigate additional dangers, and strengthen defenses towards comparable threats. Response Remediation Upon receiving remediation suggestions from LevelBlue, the shopper acted swiftly to make sure any compromised O365 accounts have been accounted for and remediated.
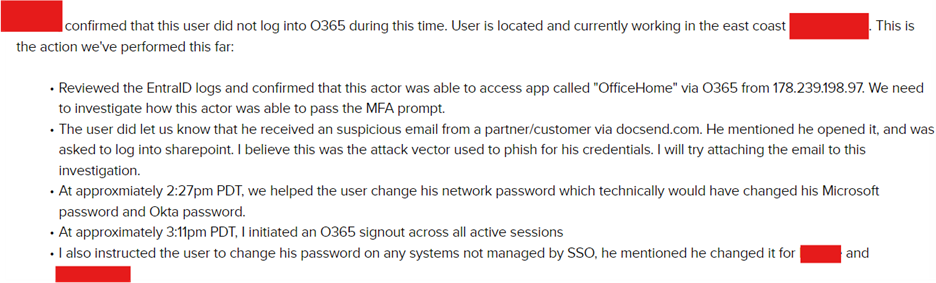
Investigation A’s buyer response to the remediation suggestions. Additional triage was carried out through buyer request.
LevelBlue SOC was in a position to establish the supply URL that contributed to the enterprise e-mail compromise –though the menace actor eliminated the malicious recordsdata from the shared repository. 1. The LevelBlue Labs staff was consulted on behalf of the SOC and Risk Hunters’ collaborative findings. Together with all three USM Wherever associated findings in addition to open-source IOCs and analysis, the aim was to supply justification for including a brand new correlation rule which might profit the purchasers being monitored.

2. Whereas a Correlation Rule was labored on by LevelBlue Labs, to supply protection primarily based on the logging data and findings throughout the September seventeenth submitted menace hunt, the MDR SOC applied an Orchestration Rule throughout the shopper fleet accounting for the artifacts recognized throughout the menace hunt.
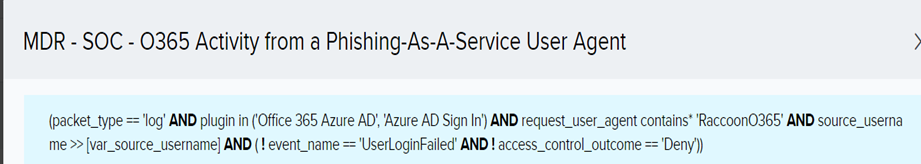
Detections
LevelBlue USM Wherever clients will profit from a Pulse created with new domains found attributed to RaccoonO365. The Pulse title might be discovered beneath.
RaccoonO365 AiTM – C2 IP/Area Tracker
The next correlation guidelines are designed to assist USMA customers establish potential phishing makes an attempt and adversary-in-the-middle (AiTM) assault exercise.
|
Rule Technique Title |
|
O365 Adversary In The Center Phishing – MFA Reset Verfication Modified With Login |
|
Okta Phishing Detection with FastPass Origin Verify |
RaccoonO365 Domains Noticed by LevelBlue Labs
|
TYPE |
INDICATOR |
DESCRIPTION |
|
DOMAIN |
sharedfilesclouddrive[.]com
|
RaccoonO365 area |
|
DOMAIN
|
doccloudonedrivefiles[.]com |
RaccoonO365 area
|
|
DOMAIN
|
e-sharedonedrivefile[.]com |
RaccoonO365 area
|
|
DOMAIN
|
e-storagedrive[.]com |
RaccoonO365 area
|
|
DOMAIN
|
ecloud-sharedfile[.]com |
RaccoonO365 area
|
|
DOMAIN
|
eclouddrivesharedfiles[.]com |
RaccoonO365 area
|
|
DOMAIN
|
ecloudfileshare[.]com |
RaccoonO365 area
|
|
DOMAIN
|
office365suite[.]cloud
|
RaccoonO365 area
|
|
DOMAIN
|
docsoffice365[.]cloud
|
RaccoonO365 area
|
|
DOMAIN
|
officefilesecloud[.]cloud
|
RaccoonO365 area
|
|
SURICATA IDS SIGNATURES |
|
alert http $EXTERNAL_NET any -> $HOME_NET any (msg:”AV USER_AGENTS RaccoonO365 user_agent noticed”; move:established,to_server; content material:”RaccoonO365″; http_user_agent; startswith; reference:url,https://ig3thack3d4u.com/weblog/RaccoonO365PAAS; classtype:web-application-attack; sid:4002782; rev:1; metadata:created_at 2024_12_10, updated_at 2024_12_10;) |

