Generative AI (GenAI) is making waves internationally. Its reputation and widespread use has additionally attracted the eye of cybercriminals, resulting in numerous cyberthreats. But a lot dialogue round threats related to instruments like ChatGPT has centered on how the expertise may be misused to assist fraudsters create convincing phishing messages, produce malicious code or probe for vulnerabilities.
Maybe fewer individuals are speaking about the usage of GenAI as a lure and a Malicious program during which to cover malware. Examples should not too troublesome to return by. Final 12 months, for example, we wrote a couple of marketing campaign that urged Fb customers to check out the most recent model of Google’s respectable AI software “Bard”; as a substitute, the advertisements served a malicious imposter software.
Such campaigns are examples of a worrying development, they usually’re clearly not going wherever. It’s, subsequently, key to know how they work, be taught to identify the warning indicators, and take precautions in order that your id and funds aren’t in danger.
How are the dangerous guys utilizing GenAI as a lure?
Cybercriminals have numerous methods of tricking you into putting in malware disguised as GenAI apps. These embody:
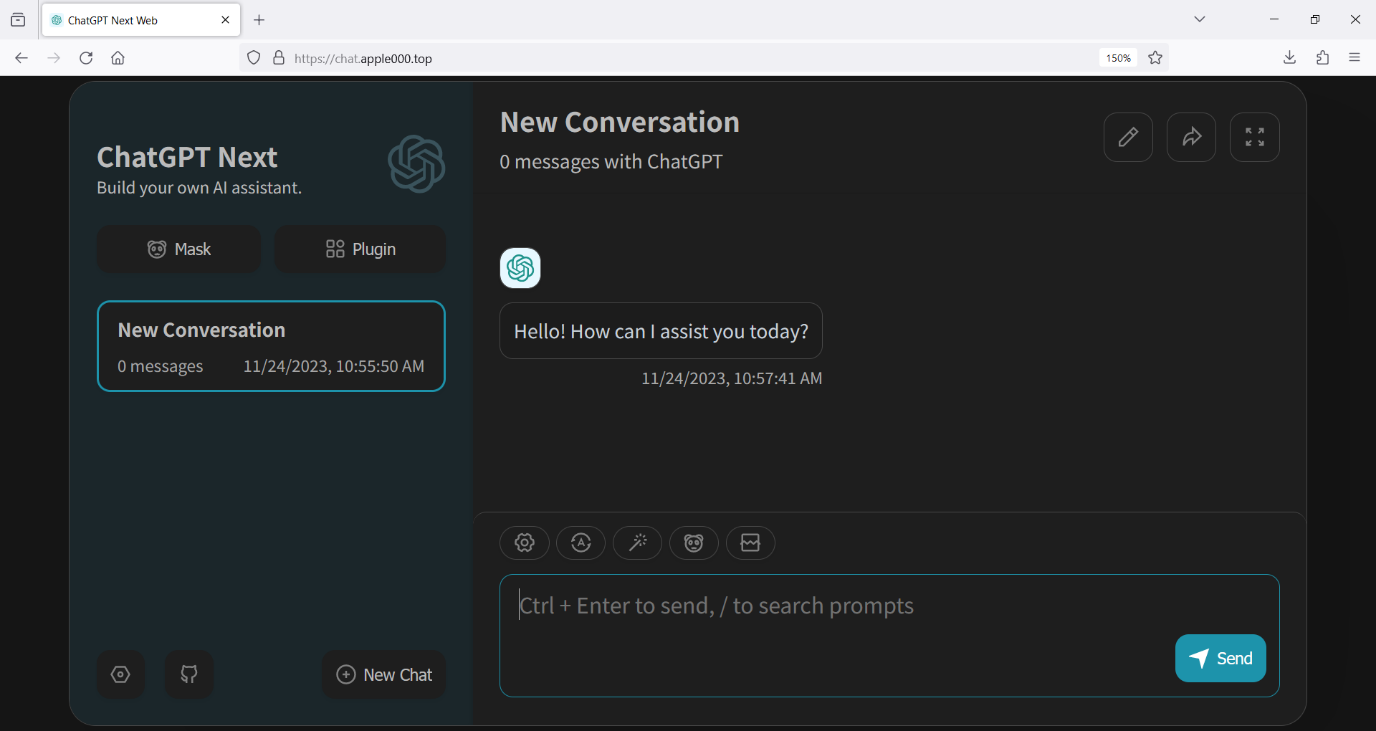
Phishing websites
Within the second half of 2023, ESET blocked over 650,000 makes an attempt to entry malicious domains containing “chapgpt” or comparable textual content. Victims almost certainly arrive there after clicking by way of from a hyperlink on social media, or through an e mail/cellular message. A few of these phishing pages could include hyperlinks to put in malware disguised as GenAI software program.
Net browser extensions
ESET’s H1 2024 risk report particulars a malicious browser extension which customers are tricked into putting in after being lured by Fb advertisements promising to take them to the official web site of OpenAI’s Sora or Google’s Gemini. Though the extension masquerades as Google Translate, it’s really an infostealer often called “Rilide Stealer V4,” which is designed to reap customers’ Fb credentials.
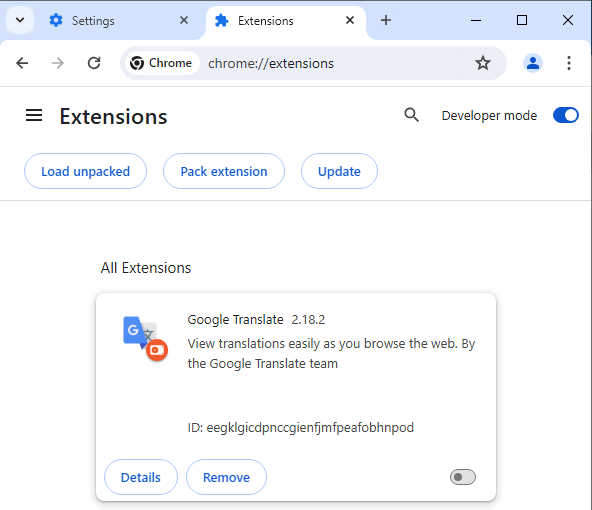
Since August 2023, ESET telemetry recorded over 4,000 makes an attempt to put in the malicious extension. Different malicious extensions declare to supply GenAI performance, and may very well accomplish that in a restricted kind, in addition to ship malware, based on Meta.
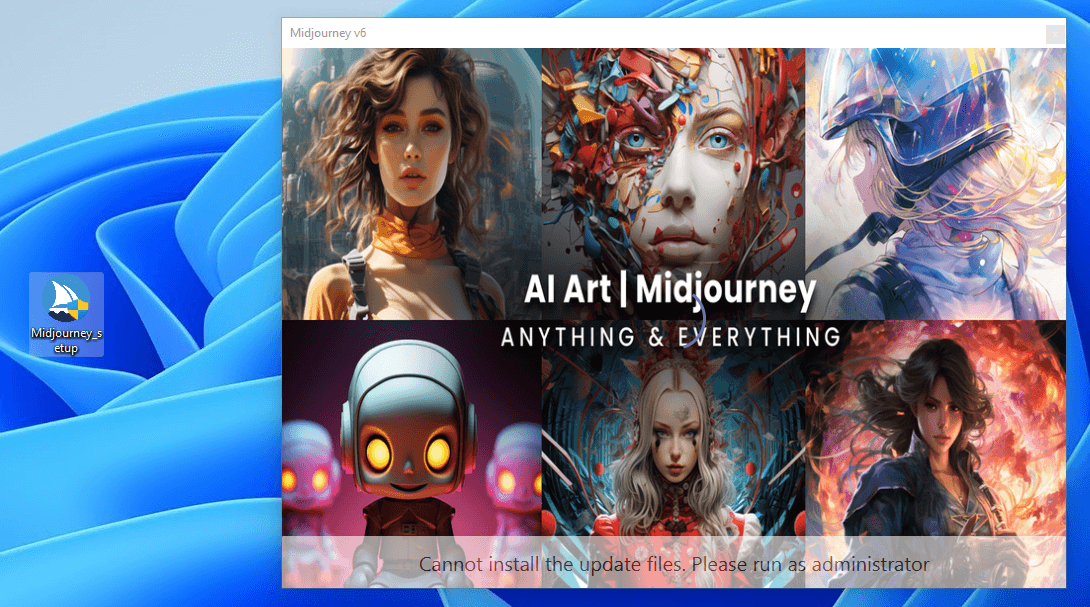
Pretend apps
There have additionally been numerous reviews of faux GenAI apps posted particularly to cellular app shops, with many of those apps containing malware. Some are laden with malicious software program designed to steal delicate data from the person’s gadget. This could embody login credentials, private identification particulars, monetary data, and extra.
Others are scams designed to generate income for the developer by promising superior AI capabilities, usually for a price. As soon as downloaded, they might bombard customers with advertisements, solicit in-app purchases, or require subscriptions for companies which are both non-existent or of extraordinarily poor high quality.
Malicious advertisements
Malicious actors are using the recognition of GenAI instruments to trick customers into clicking on malicious promoting. Malicious Fb advertisements are significantly prevalent. Meta warned final 12 months that many of those campaigns are designed to compromise “companies with entry to advert accounts throughout the web.”
Menace actors hijack a respectable account or web page, change the profile data to make it seems as if an genuine ChatGPT or different GenAI-branded web page, after which use the accounts to run pretend advertisements. These provide hyperlinks to the most recent model of GenAI instruments, however in actuality deploy infostealer malware, based on researchers.
The artwork of the lure
People are social creatures. We wish to imagine the tales we’re instructed. We’re additionally covetous. We wish to pay money for the most recent devices and apps. Menace actors exploit our greed, our concern of lacking out, our credulity and our curiosity to get us to click on on malicious hyperlinks or obtain apps with malware hidden inside.
However for us to hit that set up button, what’s on provide needs to be fairly head turning, and – like all the most effective lies – it needs to be grounded in a kernel of reality. Social engineers are significantly adept at mastering these darkish arts – persuading us to click on on salacious information tales about celebrities, or present affairs (keep in mind these tall tales about pretend COVID-19 vaccines?). Generally they’ll provide us one thing free of charge, at an unbelievable low cost, or earlier than anybody else will get it. As we defined right here, we fall for these tips as a result of:
- We’re in a rush, particularly if we’re viewing the content material on our cellular gadget
- They’re good storytellers, and are more and more fluent, utilizing (paradoxically) GenAI to inform their tales seamlessly in a number of languages
- We like to get one thing for nothing, even when it’s too good to be true
- The dangerous guys are good at sharing data on what works and what doesn’t, whereas we’re much less good at in search of out or taking recommendation
- We’re hardwired to respect authority, or at the least the legitimacy of a proposal, so long as it’s “formally” branded
On the subject of GenAI, malware-slingers are getting more and more subtle. They use a number of channels to unfold their lies. And so they’re disguising malware as all the things from ChatGPT and video creator Sora AI, to picture generator Midjourney, DALL-E and picture editor Evoto. Most of the variations they tout aren’t but accessible, which pulls within the sufferer: “ChatGPT 5” or “DALL-E 3” for instance.
They guarantee malware continues to fly underneath the radar by often adapting their payloads to keep away from detection by safety instruments. And so they take an excessive amount of effort and time to make sure their lures (akin to Fb advertisements) look the half. If it doesn’t look official, who’s going to obtain it?
What could possibly be in danger?
So what’s the worst that might occur? If you happen to click on to obtain a pretend GenAI app in your cellular or a web site and it installs malware, what’s the top objective for the dangerous guys? In lots of circumstances it’s an info-stealer. These items of malware are designed, because the identify suggests, to reap delicate data. It may embody credentials to your on-line accounts, akin to work log-ins, or saved bank cards, session cookies (to bypass multifactor authentication), belongings saved in crypto wallets, information streams from immediate messaging apps, and way more.
It’s not nearly info-stealer malware, after all. Cybercriminals may theoretically cover any kind of malware in apps and malicious hyperlinks, together with ransomware and distant entry Trojans (RATs). For the sufferer, this might result in:
- A hacker gaining full distant management over your PC/cell phone and something saved on it. They may use entry to steal your most delicate private and monetary data, or flip your machine right into a “zombie” laptop to launch assaults on others
- They may use your private data for id fraud which may be extraordinarily distressing, to not point out costly, for the sufferer
- They may use monetary and id particulars to acquire new credit score traces in your identify, or to steal crypto belongings and entry and drain financial institution accounts
- They may even use your work credentials to launch an assault in your employer, or a companion/provider group. A current digital extortion marketing campaign which used infostealer malware to achieve entry to Snowflake accounts led to the compromise of tens of thousands and thousands of buyer particulars
keep away from malicious GenAI lures
Some tried-and-tested greatest practices ought to maintain you heading in the right direction and away from GenAI threats. Take into account the next:
- Solely set up apps from official app shops
Google Play and the Apple App Retailer have rigorous vetting processes and common monitoring to weed out malicious apps. Keep away from downloading apps from third-party web sites or unofficial sources, as they’re much more prone to host malicious wares.
- Double test the builders behind apps and any opinions of their software program
Earlier than downloading an app, confirm the developer’s credentials and search for different apps they’ve developed and browse person opinions. Suspicious apps usually have poorly written descriptions, restricted developer historical past, and unfavorable suggestions highlighting points.
- Be cautious of clicking on digital advertisements
Digital advertisements, particularly on social media platforms like Fb, generally is a widespread vector for distributing malicious apps. As an alternative of clicking on advertisements, straight seek for the app or software in your official app retailer to make sure you’re getting the respectable model.
- Verify net browser extensions earlier than putting in them
Net browser extensions can improve your net expertise however may pose safety dangers. Verify the developer’s background and browse opinions earlier than putting in any extensions. Stick with well-known builders and extensions with excessive scores and substantial person suggestions.
- Use complete safety software program from a good vendor
Guarantee you may have strong safety software program from a good vendor put in in your PC and all cellular units. This supplies real-time safety towards malware, phishing makes an attempt, and different on-line threats.
Phishing stays a perennial risk. Be cautious of unsolicited messages that immediate you to click on on hyperlinks or open attachments. Confirm the sender’s id earlier than interacting with any e mail, textual content, or social media message that seems suspicious.
- Allow multi-factor authentication (MFA) for all of your on-line accounts
MFA provides an additional layer of safety to your on-line accounts by requiring a number of verification strategies. Allow MFA wherever potential to guard your accounts even when your password is compromised.
As proven above, cybercriminals can’t resist exploiting the thrill round new releases. If you happen to see a proposal to obtain a brand new model of a GenAI software, confirm its availability by way of official channels earlier than continuing. Verify the official web site or trusted information sources to verify the discharge.
GenAI is altering the world round us at a fast tempo. Be sure it doesn’t change yours for the more serious.

