Besieged by scammers looking for to phish person accounts over the phone, Apple and Google regularly warning that they may by no means attain out unbidden to customers this manner. Nevertheless, new particulars in regards to the inner operations of a prolific voice phishing gang present the group routinely abuses reputable companies at Apple and Google to pressure a wide range of outbound communications to their customers, together with emails, automated cellphone calls and system-level messages despatched to all signed-in units.

Picture: Shutterstock, iHaMoo.
KrebsOnSecurity lately informed the saga of a cryptocurrency investor named Tony who was robbed of greater than $4.7 million in an elaborate voice phishing assault. In Tony’s ordeal, the crooks seem to have initially contacted him by way of Google Assistant, an AI-based service that may interact in two-way conversations. The phishers additionally abused reputable Google companies to ship Tony an electronic mail from google.com, and to ship a Google account restoration immediate to all of his signed-in units.
Right now’s story pivots off of Tony’s heist and new particulars shared by a scammer to elucidate how these voice phishing teams are abusing a reputable Apple phone assist line to generate “account affirmation” message prompts from Apple to their clients.
Earlier than we get to the Apple rip-off intimately, we have to revisit Tony’s case. The phishing area used to steal roughly $4.7 million in cryptocurrencies from Tony was verify-trezor[.]io. This area was featured in a writeup from February 2024 by the safety agency Lookout, which discovered it was one in every of dozens being utilized by a prolific and audacious voice phishing group it dubbed “Crypto Chameleon.”
Crypto Chameleon was openly making an attempt to voice phish workers on the U.S. Federal Communications Fee (FCC), in addition to these working on the cryptocurrency exchanges Coinbase and Binance. Lookout researchers found a number of voice phishing teams have been utilizing a brand new phishing equipment that carefully mimicked the only sign-on pages for Okta and different authentication suppliers.
As we’ll see in a second, that phishing equipment is operated and rented out by a cybercriminal often called “Perm” a.ok.a. “Annie.” Perm is the present administrator of Star Fraud, one of many extra consequential cybercrime communities on Telegram and one which has emerged as a foundry of innovation in voice phishing assaults.
A evaluation of the numerous messages that Perm posted to Star Fraud and different Telegram channels confirmed they labored carefully with one other cybercriminal who glided by the handles “Aristotle” and simply “Stotle.”
It’s not clear what prompted the rift, however sooner or later final 12 months Stotle determined to activate his erstwhile enterprise associate Perm, sharing extraordinarily detailed movies, tutorials and secrets and techniques that shed new mild on how these phishing panels function.
Stotle defined that the division of spoils from every theft is determined upfront by all members. Some co-conspirators will probably be paid a set price for every name, whereas others are promised a proportion of any general quantity stolen. The particular person in control of managing or renting out the phishing panel to others will typically take a proportion of every theft, which in Perm’s case is 10 p.c.
When the phishing group settles on a goal of curiosity, the scammers will create and be a part of a brand new Discord channel. This enables every logged on member to share what’s presently on their display, and these screens are tiled in a collection of packing containers so that everybody can see all different name participant screens directly.
Every participant within the name has a selected function, together with:
-The Caller: The particular person talking and making an attempt to social engineer the goal.
-The Operator: The person managing the phishing panel, silently transferring the sufferer from web page to web page.
-The Drainer: The one that logs into compromised accounts to empty the sufferer’s funds.
-The Proprietor: The phishing panel proprietor, who will regularly eavesdrop on and take part in rip-off calls.
‘OKAY, SO THIS REALLY IS APPLE’
In a single video of a reside voice phishing assault shared by Stotle, scammers utilizing Perm’s panel focused a musician in California. All through the video, we are able to see Perm monitoring the dialog and working the phishing panel within the higher proper nook of the display.
In step one of the assault, they peppered the goal’s Apple system with notifications from Apple by trying to reset his password. Then a “Michael Eager” known as him, spoofing Apple’s cellphone quantity and saying they have been with Apple’s account restoration group.
The goal informed Michael that somebody was making an attempt to alter his password, which Michael calmly defined they might examine. Michael stated he was going to ship a immediate to the person’s system, and proceeded to position a name to an automatic line that answered as Apple assist saying, “I’d prefer to ship a consent notification to your Apple units. Do I’ve permission to try this?”
On this phase of the video, we are able to see the operator of the panel is asking the actual Apple buyer assist cellphone quantity 800-275-2273, however they’re doing so by spoofing the goal’s cellphone quantity (the sufferer’s quantity is redacted within the video above). That’s as a result of calling this assist quantity from a cellphone quantity tied to an Apple account and choosing “1” for “sure” will then ship an alert from Apple that shows the next message on all related units:
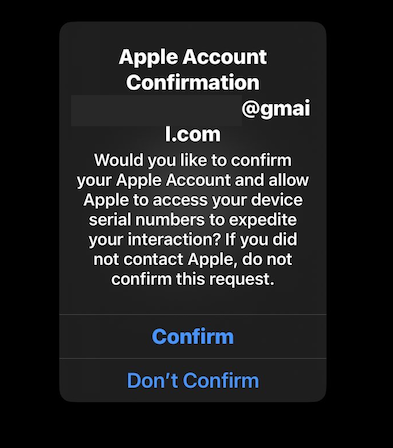
Calling the Apple assist quantity 800-275-2273 from a cellphone quantity tied to an Apple account will trigger a immediate just like this one to look on all linked Apple units.
KrebsOnSecurity requested two completely different safety companies to check this utilizing the caller ID spoofing service proven in Perm’s video, and positive sufficient calling that 800 quantity for Apple by spoofing my cellphone quantity because the supply prompted the Apple Account Affirmation to pop up on all of my signed-in Apple units.
In essence, the voice phishers are utilizing an automatic Apple cellphone assist line to ship notifications from Apple and to trick folks into considering they’re actually speaking with Apple. The phishing panel video leaked by Stotle reveals this system fooled the goal, who felt utterly comfy that he was speaking to Apple after receiving the assist immediate on his iPhone.
“Okay, so this actually is Apple,” the person stated after receiving the alert from Apple. “Yeah, that’s undoubtedly not me making an attempt to reset my password.”
“Not an issue, we are able to go forward and maintain this at the moment,” Michael replied. “I’ll go forward and immediate your system with the steps to shut out this ticket. Earlier than I do this, I do extremely counsel that you simply change your password within the settings app of your system.”
The goal stated they weren’t positive precisely how to try this. Michael replied “no drawback,” after which described the right way to change the account password, which the person stated he did on his personal system. At this level, the musician was nonetheless accountable for his iCloud account.
“Password is modified,” the person stated. “I don’t know what that was, however I recognize the decision.”
“Yup,” Michael replied, organising the killer blow. “I’ll go forward and immediate you with the subsequent step to shut out this ticket. Please give me one second.”
The goal then obtained a textual content message that referenced details about his account, stating that he was in a assist name with Michael. Included within the message was a hyperlink to a web site that mimicked Apple’s iCloud login web page — 17505-apple[.]com. As soon as the goal navigated to the phishing web page, the video confirmed Perm’s display within the higher proper nook opening the phishing web page from their finish.
“Oh okay, now I log in with my Apple ID?,” the person requested.
“Yup, then simply observe the steps it requires, and should you want any assist, simply let me know,” Michael replied.
Because the sufferer typed of their Apple password and one-time passcode on the pretend Apple website, Perm’s display could possibly be seen within the background logging into the sufferer’s iCloud account.
It’s unclear whether or not the phishers have been in a position to steal any cryptocurrency from the sufferer on this case, who didn’t reply to requests for remark. Nevertheless, shortly after this video was recorded, somebody leaked a number of music recordings stolen from the sufferer’s iCloud account.
On the conclusion of the decision, Michael provided to configure the sufferer’s Apple profile in order that any additional adjustments to the account would want to occur in particular person at a bodily Apple retailer. This seems to be one in every of a number of scripted ploys utilized by these voice phishers to realize and preserve the goal’s confidence.
A tutorial shared by Stotle titled “Social Engineering Script” consists of a variety of ideas for rip-off callers that may assist set up belief or a rapport with their prey. When the callers are impersonating Coinbase workers, for instance, they may supply to signal the person up for the corporate’s free safety electronic mail publication.
“Additionally, on your safety, we’re in a position to subscribe you to Coinbase Bytes, which is able to mainly provide you with updates to your electronic mail about knowledge breaches and updates to your Coinbase account,” the script reads. “So we should always have gone forward and efficiently subscribed you, and you need to have gotten an electronic mail affirmation. Please let me know if that’s the case. Alright, good.”
In actuality, all they’re doing is getting into the goal’s electronic mail handle into Coinbase’s public electronic mail publication signup web page, however it’s a remarkably efficient approach as a result of it demonstrates to the would-be sufferer that the caller has the power to ship emails from Coinbase.com.
Requested to remark for this story, Apple stated there was no breach, hack, or technical exploit of iCloud or Apple companies, and that the corporate is repeatedly including new protections to deal with new and rising threats. For instance, it stated it has carried out price limiting for multi-factor authentication requests, which have been abused by voice phishing teams to impersonate Apple.
Apple stated its representatives won’t ever ask customers to offer their password, system passcode, or two-factor authentication code or to enter it into an online web page, even when it seems like an official Apple web site. If a person receives a message or name that claims to be from Apple, here’s what the person ought to count on.
AUTODOXERS
In response to Stotle, the goal lists utilized by their phishing callers originate largely from a couple of crypto-related knowledge breaches, together with the 2022 and 2024 breaches involving person account knowledge stolen from cryptocurrency {hardware} pockets vendor Trezor.
Perm’s group and different crypto phishing gangs depend on a mixture of selfmade code and third-party knowledge dealer companies to refine their goal lists. Often called “autodoxers,” these instruments assist phishing gangs rapidly automate the acquisition and/or verification of private knowledge on a goal prior to every name try.
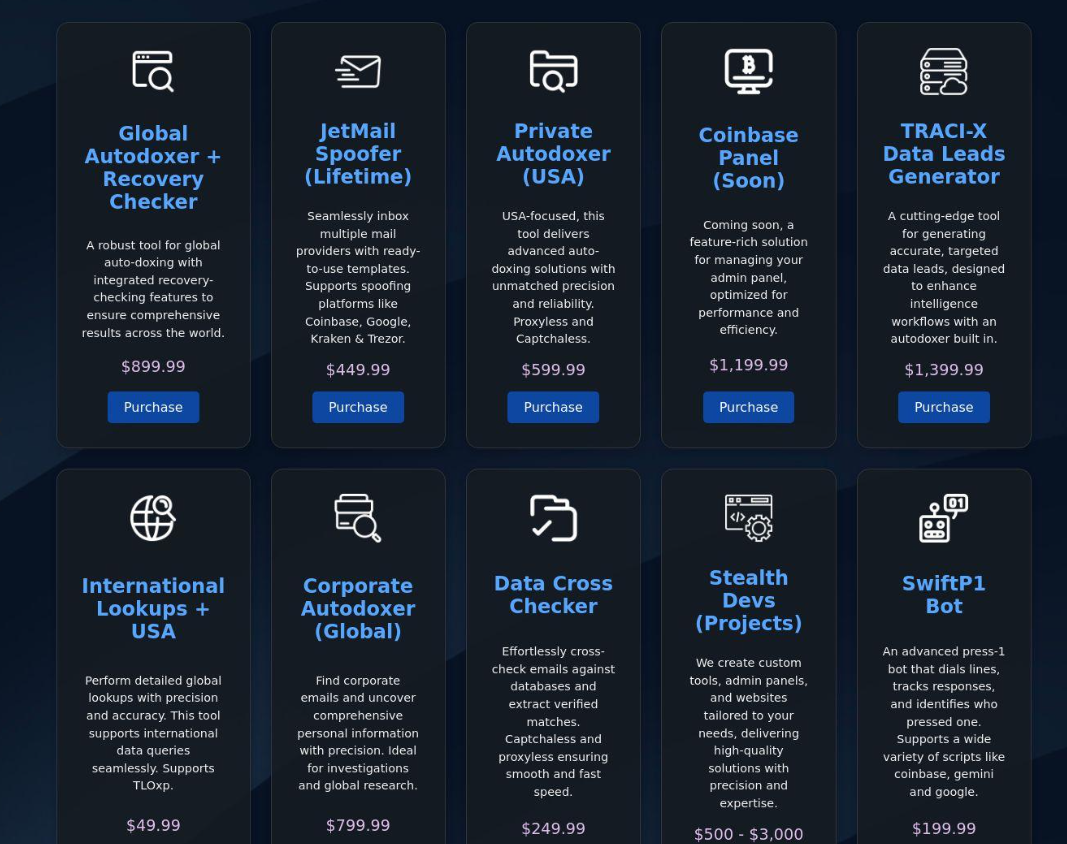
One “autodoxer” service marketed on Telegram that promotes a spread of voice phishing instruments and companies.
Stotle stated their autodoxer used a Telegram bot that leverages hacked accounts at shopper knowledge brokers to assemble a wealth of details about their targets, together with their full Social Safety quantity, date of beginning, present and former addresses, employer, and the names of relations.
The autodoxers are used to confirm that every electronic mail handle on a goal listing has an lively account at Coinbase or one other cryptocurrency change, guaranteeing that the attackers don’t waste time calling individuals who don’t have any cryptocurrency to steal.
A few of these autodoxer instruments additionally will verify the worth of the goal’s house handle at property search companies on-line, after which kind the goal lists in order that the wealthiest are on the prime.
CRYPTO THIEVES IN THE SHARK TANK
Stotle’s messages on Discord and Telegram present {that a} phishing group renting Perm’s panel voice-phished tens of 1000’s of {dollars} value of cryptocurrency from the billionaire Mark Cuban.
“I used to be an fool,” Cuban informed KrebsOnsecurity when requested about the June 2024 assault, which he first disclosed in a short-lived put up on Twitter/X. “We have been taking pictures Shark Tank and I used to be dashing between pitches.”

Picture: Shutterstock, ssi77.
Cuban stated he first obtained a discover from Google that somebody had tried to log in to his account. Then he obtained a name from what seemed to be a Google cellphone quantity. Cuban stated he ignored a number of of those emails and calls till he determined they most likely wouldn’t cease except he answered.
“So I answered, and wasn’t paying sufficient consideration,” he stated. “They requested for the circled quantity that comes up on the display. Like a moron, I gave it to them, they usually have been in.”
Sadly for Cuban, someplace in his inbox have been the key “seed phrases” defending two of his cryptocurrency accounts, and armed with these credentials the crooks have been in a position to drain his funds. All informed, the thieves managed to steal roughly $43,000 value of cryptocurrencies from Cuban’s wallets — a comparatively small heist for this crew.
“They should have carried out some key phrase searches,” as soon as inside his Gmail account, Cuban stated. “I had despatched myself an electronic mail I had forgotten about that had my seed phrases for two accounts that weren’t very lively any longer. I had moved virtually every little thing however some smaller balances to Coinbase.”
LIFE IS A GAME: MONEY IS HOW WE KEEP SCORE
Cybercriminals concerned in voice phishing communities on Telegram are universally obsessive about their crypto holdings, primarily as a result of on this group one’s demonstrable wealth is primarily what confers social standing. It’s not unusual to see members sizing each other up utilizing a verbal shorthand of “figs,” as in figures of crypto wealth.
For instance, a low-level caller with no expertise will generally be mockingly known as a 3fig or 3f, as in an individual with lower than $1,000 to their identify. Salaries for callers are sometimes additionally referenced this manner, e.g. “Weekly wage: 5f.”

This meme shared by Stotle makes use of humor to depict an all-too-common pathway for voice phishing callers, who are sometimes minors recruited from gaming networks like Minecraft and Roblox. The picture that Lookout utilized in its weblog put up for Crypto Chameleon will be seen within the decrease proper hooded determine.
Voice phishing teams regularly require new members to offer “proof of funds” — screenshots of their crypto holdings, ostensibly to show they aren’t penniless — earlier than they’re allowed to hitch.
This proof of funds (POF) demand is typical amongst thieves promoting high-dollar gadgets, as a result of it tends to chop down on the time-wasting inquiries from criminals who can’t afford what’s on the market anyway. However it has develop into so frequent in cybercrime communities that there are actually a number of companies designed to create pretend POF photos and movies, permitting clients to brag about giant crypto holdings with out truly possessing stated wealth.
A number of of the phishing panel movies shared by Stotle function audio that implies co-conspirators have been training responses to sure name situations, whereas different members of the phishing group critiqued them or tried disrupt their social engineering by being verbally abusive.
These teams will set up and function for a couple of weeks, however are inclined to disintegrate when one member of the conspiracy decides to steal some or the entire loot, referred to in these communities as “snaking” others out of their agreed-upon sums. Nearly invariably, the phishing teams will splinter aside over the drama brought on by one in every of these snaking occasions, and particular person members finally will then re-form a brand new phishing group.
Allison Nixon is the chief analysis officer for Unit 221B, a cybersecurity agency in New York that has labored on a variety of investigations involving these voice phishing teams. Nixon stated the fixed snaking throughout the voice phishing circles factors to a psychological self-selection phenomenon that’s in determined want of educational examine.
“Briefly, an individual whose ethical compass lets them rob previous folks may also be a foul enterprise associate,” Nixon stated. “That is one other basic flaw on this ecosystem and why most teams finish in betrayal. This structural drawback is nice for journalists and the police too. A lot of snitching.”
POINTS FOR BRAZENNESS
Requested in regards to the dimension of Perm’s phishing enterprise, Stotle stated there have been dozens of distinct phishing teams paying to make use of Perm’s panel. He stated every group was assigned their very own subdomain on Perm’s important “command and management server,” which naturally makes use of the area identify commandandcontrolserver[.]com.
A evaluation of that area’s historical past by way of DomainTools.com reveals there are at the very least 57 separate subdomains scattered throughout commandandcontrolserver[.]com and two different associated management domains — thebackendserver[.]com and lookoutsucks[.]com. That latter area was created and deployed shortly after Lookout revealed its weblog put up on Crypto Chameleon.
The dozens of phishing domains that cellphone house to those management servers are all stored offline when they aren’t actively being utilized in phishing assaults. A social engineering coaching information shared by Stotle explains this apply minimizes the possibilities {that a} phishing area will get “redpaged,” a reference to the default pink warning pages served by Google Chrome or Firefox every time somebody tries to go to a website that’s been flagged for phishing or distributing malware.
What’s extra, whereas the phishing websites are reside their operators usually place a CAPTCHA problem in entrance of the primary web page to stop safety companies from scanning and flagging the websites as malicious.
It could appear odd that so many cybercriminal teams function so overtly on instantaneous collaboration networks like Telegram and Discord. In any case, this weblog is replete with tales about cybercriminals getting caught thanks to private particulars they inadvertently leaked or disclosed themselves.
Nixon stated the relative openness of those cybercrime communities makes them inherently dangerous, however it additionally permits for the speedy formation and recruitment of recent potential co-conspirators. Furthermore, at the moment’s English-speaking cybercriminals are typically extra afraid of getting house invaded or mugged by fellow cyber thieves than they’re of being arrested by authorities.
“The most important structural menace to the web felony ecosystem just isn’t the police or researchers, it’s fellow criminals,” Nixon stated. “To guard them from themselves, each felony discussion board and market has a status system, although they realize it’s a significant legal responsibility when the police come. That’s the reason I’m not anxious as we see criminals migrate to varied ‘encrypted’ platforms that promise to disregard the police. To guard themselves higher in opposition to the regulation, they need to ditch their protections in opposition to fellow criminals and that’s not going to occur.”

