ESET Analysis
ESET researchers found a zero-day Telegram for Android exploit that enables sending malicious recordsdata disguised as movies
22 Jul 2024
•
,
6 min. learn
ESET researchers found a zero-day exploit that targets Telegram for Android, which appeared on the market for an unspecified value in an underground discussion board submit from June 6th, 2024. Utilizing the exploit to abuse a vulnerability that we named EvilVideo, attackers may share malicious Android payloads by way of Telegram channels, teams, and chat, and make them seem as multimedia recordsdata.
We had been in a position to find an instance of the exploit, permitting us to investigate it additional, and report it to Telegram on June 26th, 2024. On July 11th, they launched an replace that fixes the vulnerability in Telegram variations 10.14.5 and above.
Determine 1 is a video demonstration and clarification of the EvilVideo vulnerability.
Determine 1. Rationalization of the EvilVideo vulnerability
Key factors of the blogpost:
- On June 26th, 2024 in an underground discussion board, we discovered an commercial for a zero-day exploit that targets Telegram for Android.
- We named the vulnerability it exploits EvilVideo and reported it to Telegram; their group patched it on July 11th, 2024.
- EvilVideo permits attackers to ship malicious payloads that seem as video recordsdata in unpatched Telegram for Android.
- The exploit solely works on Android Telegram variations 10.14.4 and older.
Discovery
We discovered the exploit being marketed on the market on an underground discussion board: see Determine 2.
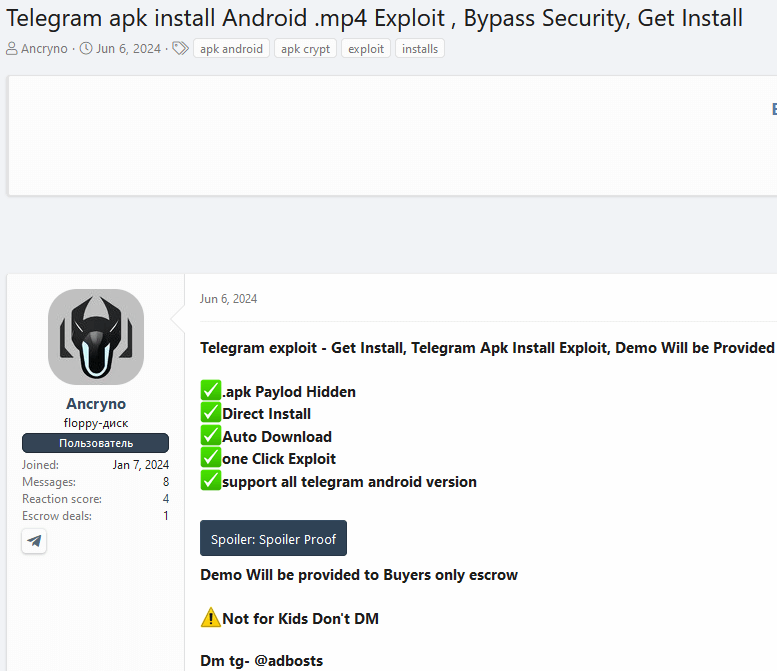
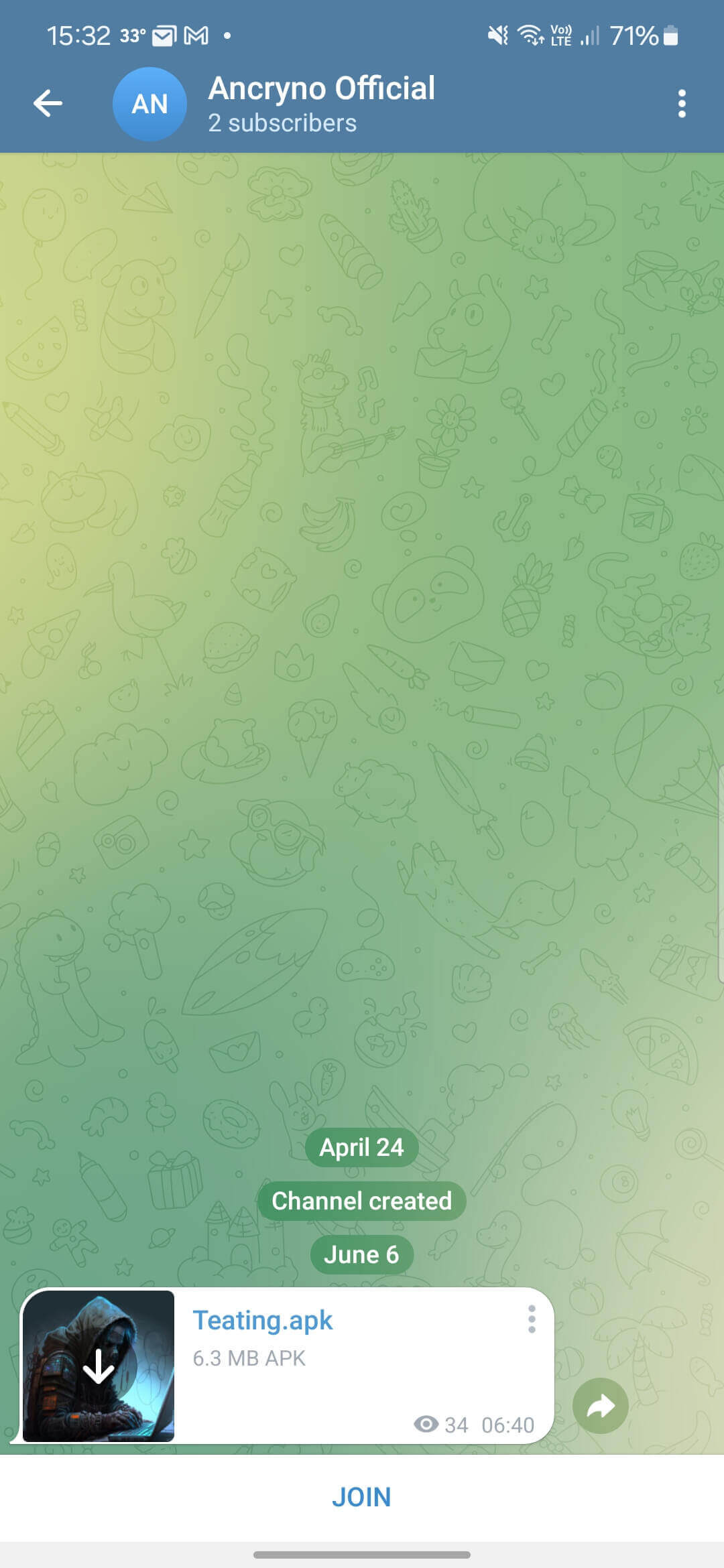
Within the submit, the vendor exhibits screenshots and a video of testing the exploit in a public Telegram channel. We had been in a position to establish the channel in query, with the exploit nonetheless out there. That allowed us to get our palms on the payload and check it ourselves.
Evaluation
Our evaluation of the exploit revealed that it really works on Telegram variations 10.14.4 and older. We speculate that the particular payload is almost certainly crafted utilizing the Telegram API, because it permits builders to add particularly crafted multimedia recordsdata to Telegram chats or channels programmatically.
The exploit appears to depend on the menace actor having the ability to create a payload that shows an Android app as a multimedia preview and never as a binary attachment. As soon as shared in chat, the malicious payload seems as a 30-second video (Determine 3).
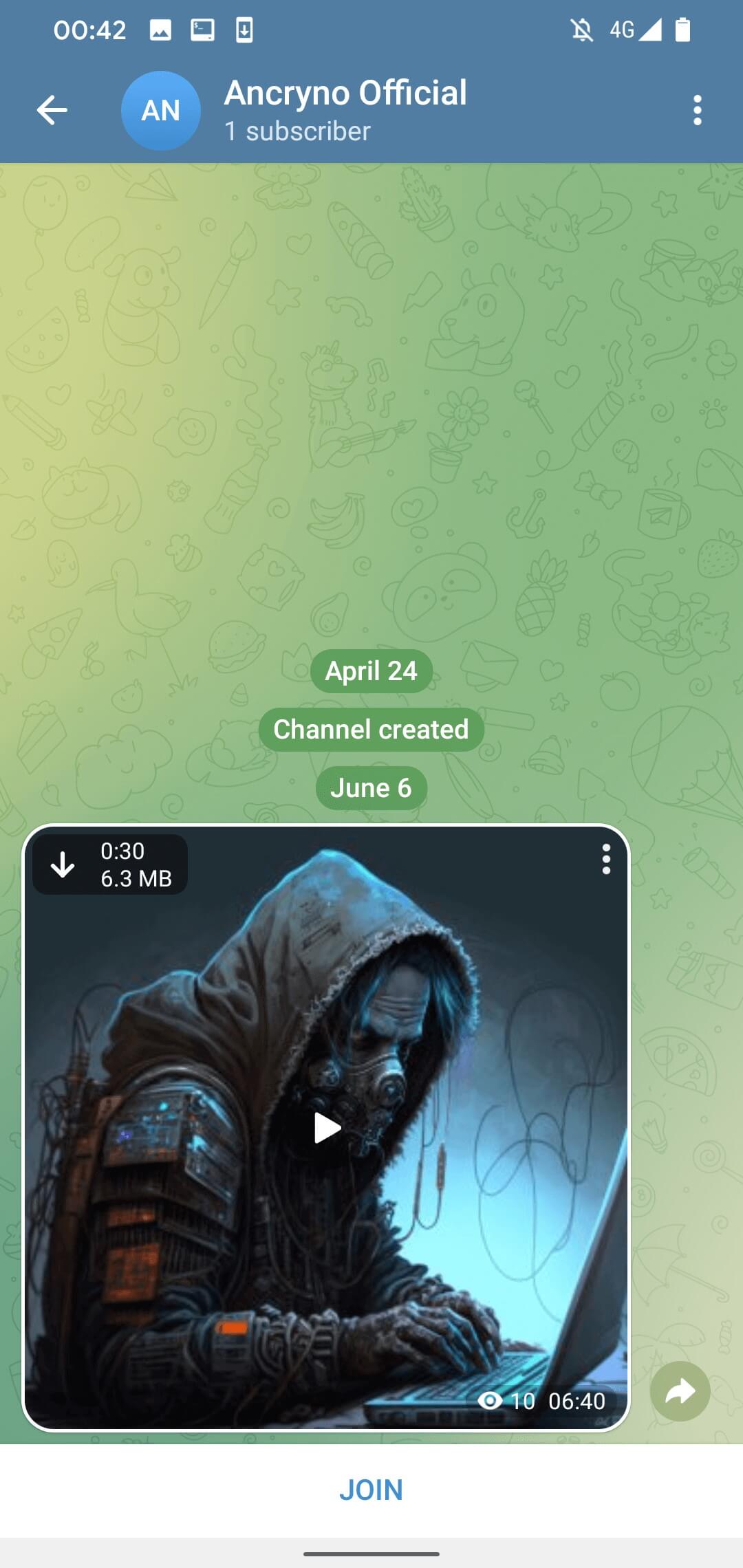
By default, media recordsdata acquired by way of Telegram are set to obtain mechanically. Which means that customers with the choice enabled will mechanically obtain the malicious payload as soon as they open the dialog the place it was shared. The choice could be disabled manually – in that case, the payload can nonetheless be downloaded by tapping the obtain button within the prime left nook of the shared, obvious video, as is seen in Determine 3.
If the consumer tries to play the “video”, Telegram shows a message that it’s unable to play it and suggests utilizing an exterior participant (see Determine 4). That is an unique Telegram warning we discovered within the supply code of the legit Telegram for Android app; it isn’t crafted and pushed by the malicious payload.
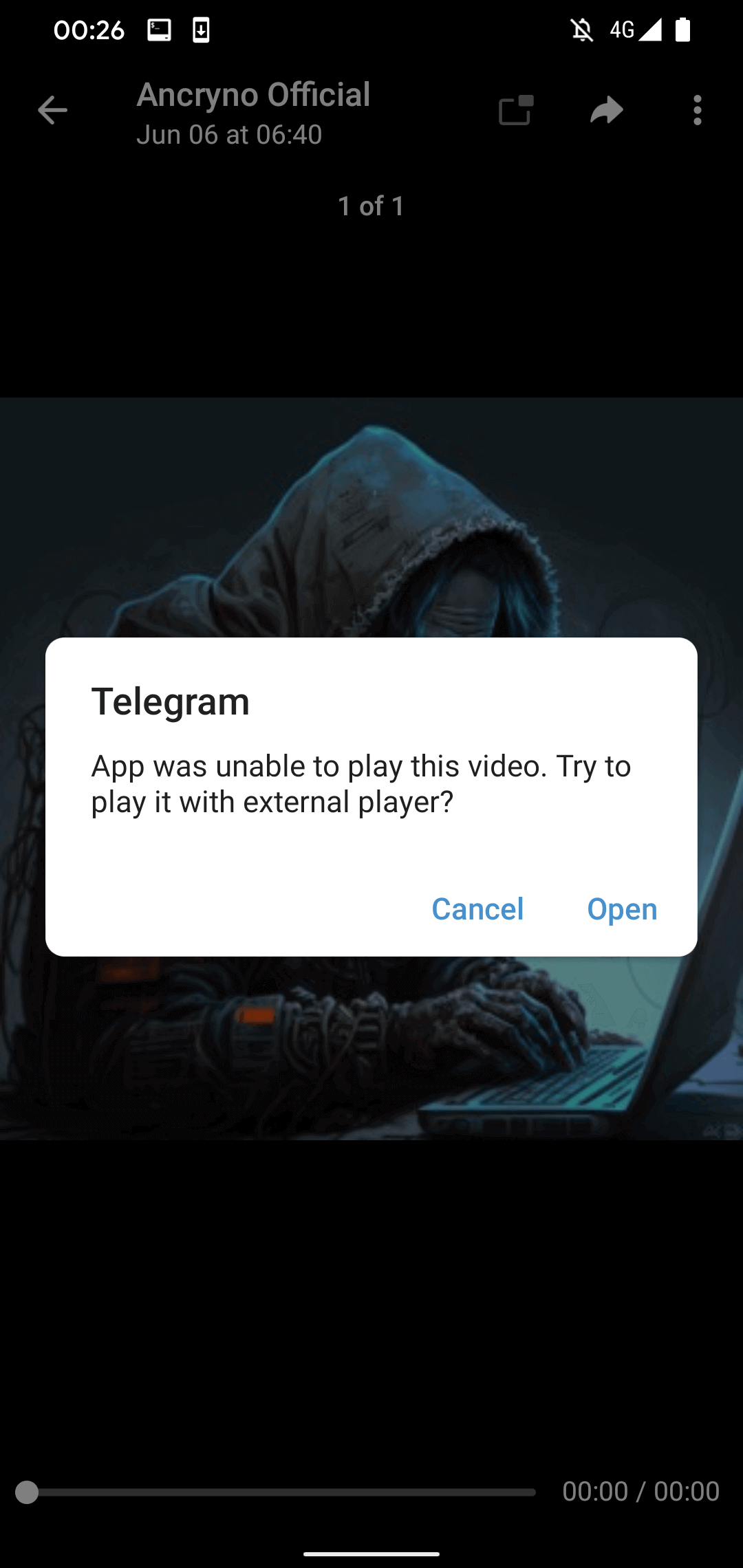
Nevertheless, if the consumer faucets the Open button within the displayed message, they are going to be requested to put in a malicious app disguised because the aforementioned exterior participant. As seen in Determine 5, earlier than set up, Telegram will ask the consumer to allow the set up of unknown apps.
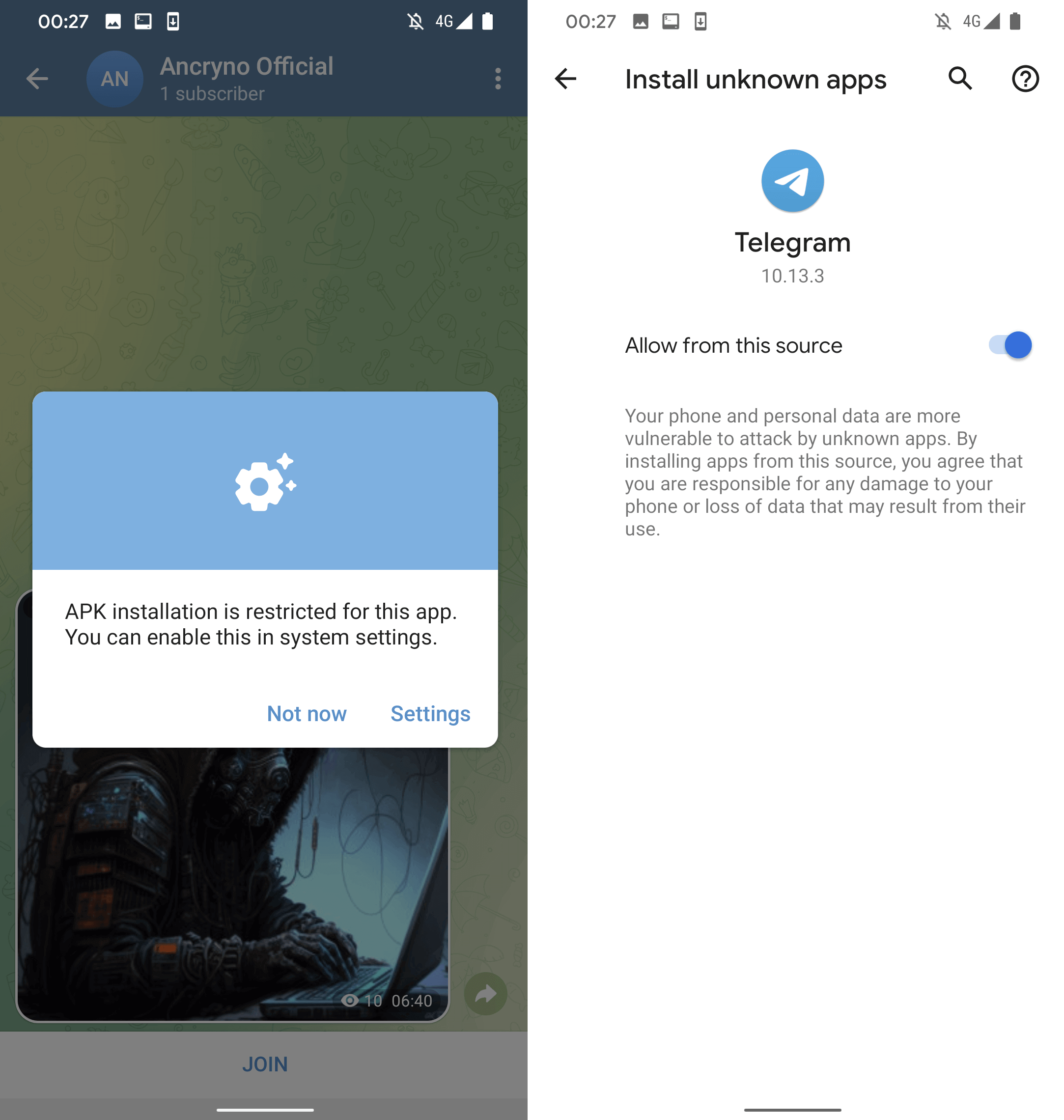
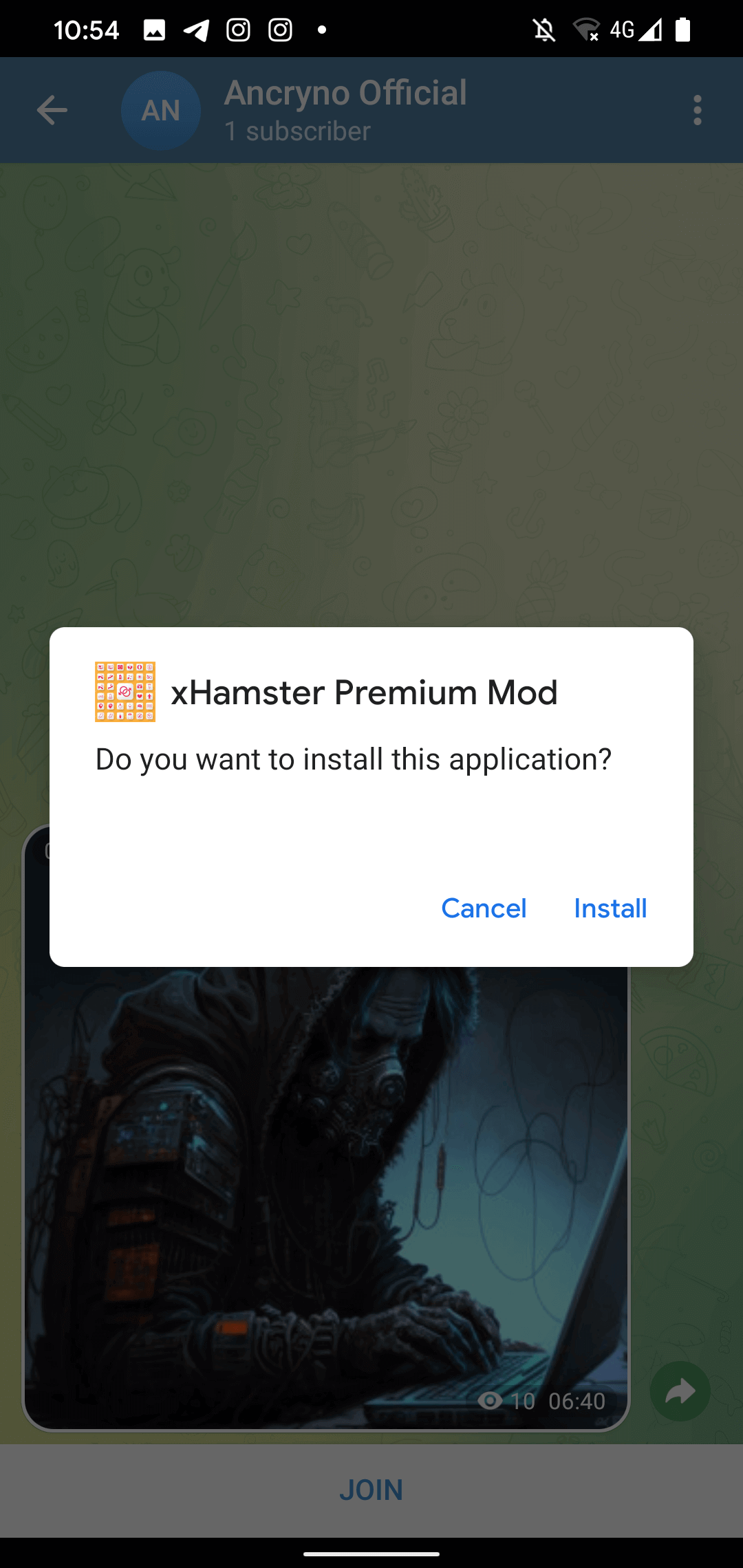
At this level, the malicious app in query has already been downloaded because the obvious video file, however with the .apk extension. Apparently, it’s the nature of the vulnerability that makes the shared file seem like a video – the precise malicious app was not altered to pose as a multimedia file, which means that the add course of was almost certainly exploited. The malicious app’s set up request could be seen in Determine 6.
Sadly, we had been unable to copy the exploit, solely examine and confirm the pattern shared by the vendor.
Telegram Internet and Desktop
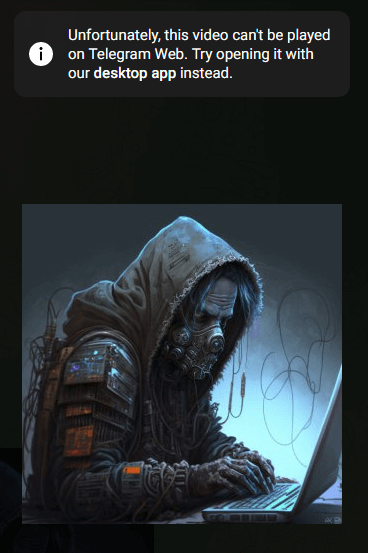
Though the payload was made solely to focus on Telegram for Android, we nonetheless tried to check its habits on different Telegram purchasers. We examined each the Telegram Internet shopper and the Telegram Desktop shopper for Home windows – as anticipated, the exploit didn’t work on both of them.
Within the case of Telegram Internet, after we tried taking part in the “video”, the shopper displayed an error message saying to strive opening the video with the desktop app as an alternative (see Determine 7). Downloading the connected file manually revealed its identify and extension to be Teating.mp4. Whereas the file itself was truly an Android executable binary (APK), Telegram treating it as an MP4 file stopped the exploit from working: to ensure that it to achieve success, the attachment would have needed to have the .apk extension.
A really related factor occurred with the Telegram Desktop shopper for Home windows: the downloaded file was named Teating.apk.mp4, so it was as soon as once more an APK binary file with a .mp4 extension. This means that even when an attacker crafted a Home windows executable for use as an alternative of the Android APK, it could nonetheless be handled as a multimedia file and the exploit wouldn’t work.
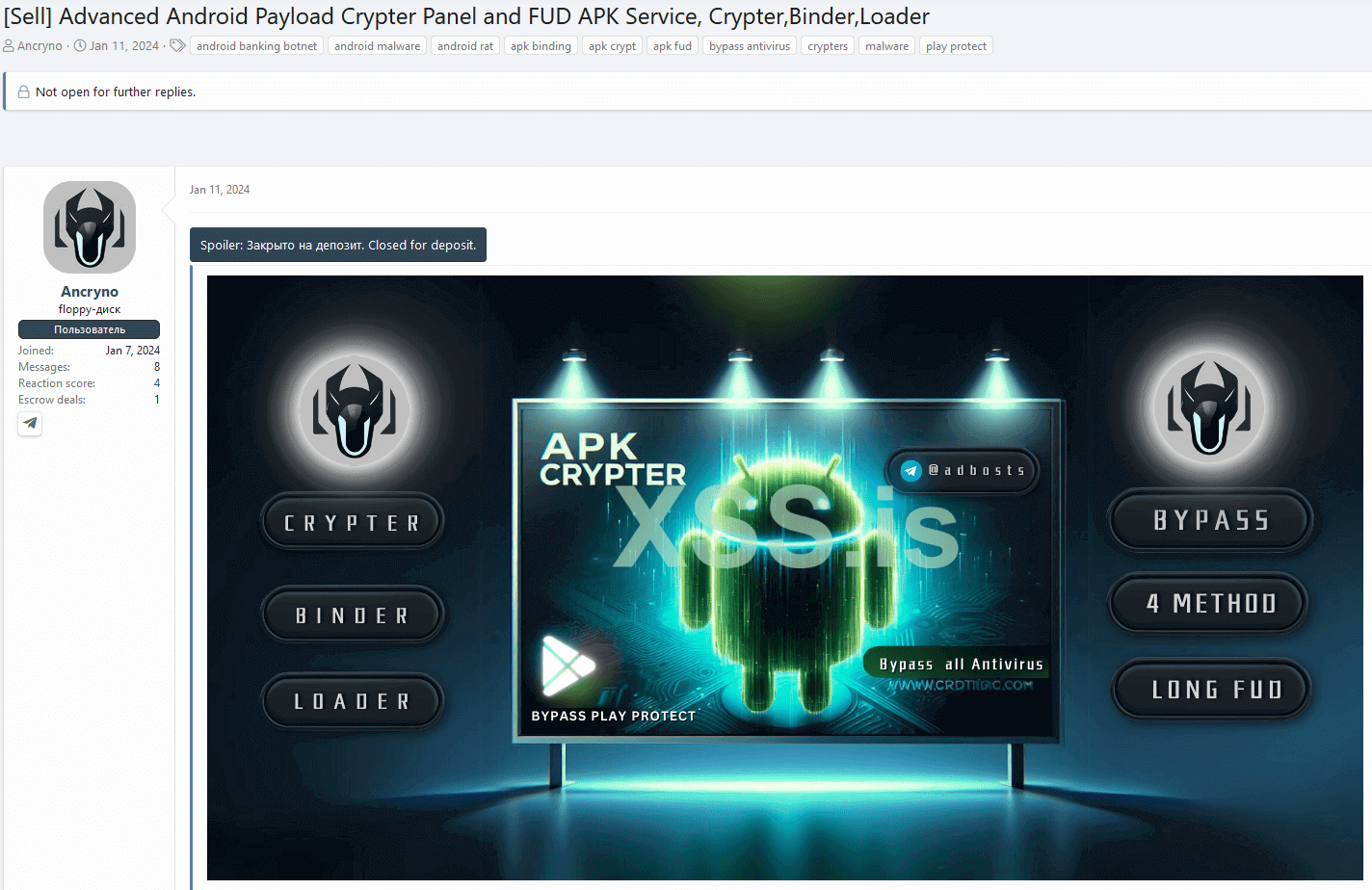
Risk actor
Whereas we have no idea a lot concerning the menace actor, we managed to search out one other shady service they’re offering primarily based on the Telegram deal with the vendor shared of their discussion board submit. Along with the exploit, they’ve been utilizing the identical underground discussion board to promote an Android cryptor-as-a-service that they declare is totally undetectable (FUD) since January 11th, 2024. The discussion board submit could be seen in Determine 8.
Vulnerability report
After discovering the EvilVideo vulnerability on June 26th, 2024, we adopted our coordinated disclosure coverage and reported it to Telegram, however acquired no response on the time. We reported the vulnerability once more on July 4th, and that point, Telegram reached out to us the identical day to verify its group was investigating EvilVideo. They fastened the difficulty, transport model 10.14.5 on July 11th, and knowledgeable us by way of e mail.
The vulnerability affected all variations of Telegram for Android as much as 10.14.4, however has been patched as of model 10.14.5. As we verified, the chat multimedia preview now appropriately shows that the shared file is an utility (Determine 9) and never a video.
Conclusion
We found a zero-day Telegram for Android exploit on the market on an underground discussion board. The vulnerability it exploits permits sending malicious payloads that seem like multimedia recordsdata by way of Telegram chat. If a consumer tries to play the obvious video, they’ll obtain a request to put in an exterior app, which truly installs the malicious payload. Fortunately, the vulnerability has been fastened as of July 11th, 2024, after we reported it to Telegram.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.comESET Analysis provides non-public APT intelligence reviews and information feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
A complete record of Indicators of Compromise (IoCs) and samples could be present in our GitHub repository.
Information
|
SHA-1 |
Filename |
Detection |
Description |
|
F159886DCF9021F41EAA |
Teating.apk |
Android/Spy.SpyMax.T |
EvilVideo payload. |
Community
|
IP |
Area |
Internet hosting supplier |
First seen |
Particulars |
|
183.83.172[.]232 |
infinityhackscharan. |
Administrator Beam Cable System |
2024‑07‑16 |
C&C server of EvilVideo payload. |
MITRE ATT&CK methods
This desk was constructed utilizing model 15 of the MITRE ATT&CK cell methods.
|
Tactic |
ID |
Identify |
Description |
|
Preliminary Entry |
Exploitation for Preliminary Entry |
The EvilVideo vulnerability could be abused by Android malware to realize preliminary machine entry. |
|
|
Execution |
Exploitation for Shopper Execution |
The EvilVideo vulnerability methods the sufferer into putting in a malicious app that impersonates a multimedia file. |



