Many GitHub customers this week acquired a novel phishing e mail warning of crucial safety holes of their code. Those that clicked the hyperlink for particulars have been requested to tell apart themselves from bots by urgent a mix of keyboard keys that causes Microsoft Home windows to obtain password-stealing malware. Whereas it’s unlikely that many programmers fell for this rip-off, it’s notable as a result of much less focused variations of it are more likely to be much more profitable in opposition to the common Home windows consumer.
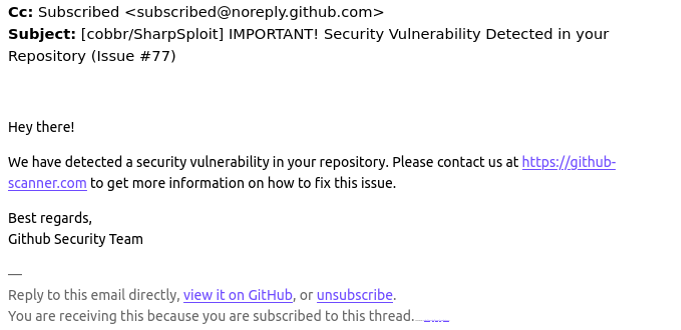
A reader named Chris shared an e mail he acquired this week that spoofed GitHub’s safety group and warned: “Hey there! Now we have detected a safety vulnerability in your repository. Please contact us at https://github-scanner[.]com to get extra info on the best way to repair this situation.”
Visiting that hyperlink generates an internet web page that asks the customer to “Confirm You Are Human” by fixing an uncommon CAPTCHA.
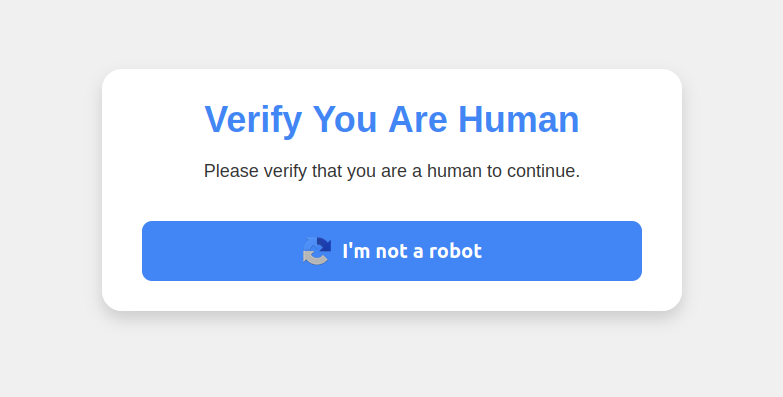
This malware assault pretends to be a CAPTCHA supposed to separate people from bots.
Clicking the “I’m not a robotic” button generates a pop-up message asking the consumer to take three sequential steps to show their humanity. Step 1 entails concurrently urgent the keyboard key with the Home windows icon and the letter “R,” which opens a Home windows “Run” immediate that can execute any specified program that’s already put in on the system.
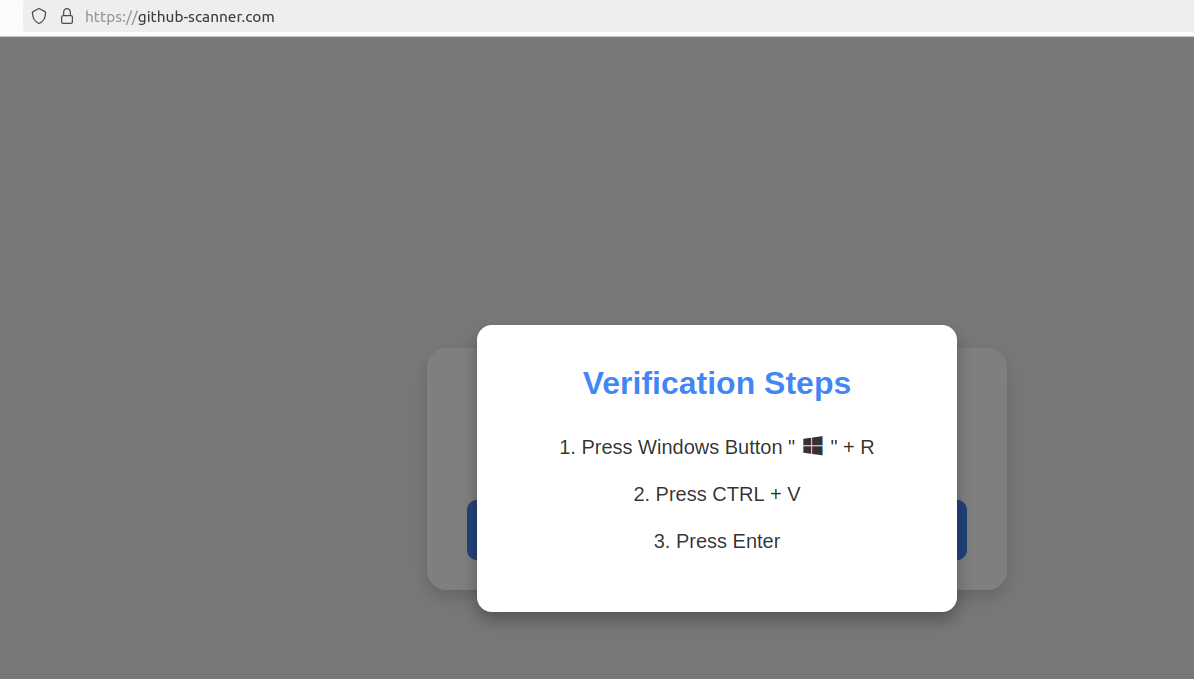
Executing this collection of keypresses prompts the built-in Home windows Powershell to obtain password-stealing malware.
Step 2 asks the consumer to press the “CTRL” key and the letter “V” on the identical time, which pastes malicious code from the location’s digital clipboard.
Step 3 — urgent the “Enter” key — causes Home windows to launch a PowerShell command, after which fetch and execute a malicious file from github-scanner[.]com known as “l6e.exe.”
PowerShell is a robust, cross-platform automation software constructed into Home windows that’s designed to make it easier for directors to automate duties on a PC or throughout a number of computer systems on the identical community.
In line with an evaluation on the malware scanning service Virustotal.com, the malicious file downloaded by the pasted textual content known as Lumma Stealer, and it’s designed to snarf any credentials saved on the sufferer’s PC.
This phishing marketing campaign might not have fooled many programmers, who little doubt natively perceive that urgent the Home windows and “R” keys will open up a “Run” immediate, or that Ctrl-V will dump the contents of the clipboard.
However I guess the identical strategy would work simply wonderful to trick a few of my much less tech-savvy associates and family members into working malware on their PCs. I’d additionally guess none of those individuals have ever heard of PowerShell, not to mention had event to deliberately launch a PowerShell terminal.
Given these realities, it might be good if there have been a easy strategy to disable or no less than closely limit PowerShell for regular finish customers for whom it may turn out to be extra of a legal responsibility.
Nonetheless, Microsoft strongly advises in opposition to nixing PowerShell as a result of some core system processes and duties might not operate correctly with out it. What’s extra, doing so requires tinkering with delicate settings within the Home windows registry, which could be a dicey enterprise even for the discovered.
Nonetheless, it wouldn’t harm to share this text with the Home windows customers in your life who match the less-savvy profile. As a result of this specific rip-off has a substantial amount of room for development and creativity.

